Tech
Cyber association launches code of conduct for security pros | Computer Weekly

ISC2, the non-profit membership association for cyber security professionals, has launched a code of conduct to spread more ethical, principled practices across the global cyber security trade.
The ISC2 Professional Code of Conduct builds on the association’s existing Code of Ethics, and has been developed with input from ISC2 members from all over the world.
It sets out to codify professional obligations and responsibilities, and reaffirms the importance of ethical behaviour, and offers guidance in areas such as sound decision-making, establishing and fostering trust, and upholding their professional integrity.
All this is set against the context of the rapidly evolving digital world, as the security profession works out how to navigate ethical challenges posed by artificial intelligence (AI), disinformation, and other threats. ISC2 said the code would help them navigate such challenges with confidence.
“Cyber security professionals have a profound responsibility not only to protect and secure individuals, organisations and systems around the world but also to uphold the integrity, accountability and trust that the profession depends on,” said ISC2 CEO Scott Beale.
“The Code provides a shared foundation for guiding ethical decision-making and professional conduct, especially as emerging technologies like AI reshape how organisations operate and how security decisions are made.
“Leveraging the collective input and decades of experience from ISC2 volunteers, the Code provides comprehensive guidance for everyone working in the cyber security field,” said Beale.
The code itself is organised around two core pillars – Ethics and Professional Conduct. The first of these sections covers topics such as integrity, client (or victim) confidentiality, respect for laws and regulations, and wider public safety and societal impact. The second section addresses areas such as accountability and responsibility, collaboration and teamwork, competence and continuous improvement, and reporting concerns and other issues.
Living document
The code was developed by a diverse taskforce of almost 1,400 ISC2 member volunteers, who have been meeting regularly to discuss the issues they face in their day-to-day work, and the opportunities that such a code could present.
Some of the key stages in its development included a major feedback-gathering exercise from ISC2 members, and external sources from the world of academia and industry. The volunteers themselves represented a diverse spread of ISC2 membership, with contributors ranging from the organisation’s basic Certified in Cybersecurity (CC) badge holders through to more advanced Certified Information Systems Security Professional (CISSP) practitioners, helping ensure and validate that the code is suitable for cyber pros at all stages of their careers.
Going forward, it will serve as a ‘living document’ subject to further amendment and refinement as the profession evolves in the coming years, and as-yet-unforeseen challenges emerge.
Panos Vlachos, an ISC2 member and code volunteer, said: “As emerging technologies, particularly AI, become more integrated into cyber security and organisational workflows, we created guidelines on ethical implementation and integration.
“Our goal with the global code is to ensure that AI and other transformative innovations align with ethical best practices, fostering responsible adoption while mitigating potential risks,” added Vlachos.
ISC2 member Srija Reddy Allam, who also sat on the panel, said they hoped both ISC2 members and non-affiliated security pros would use the code as a guide and mirror to inform their work, and reflect on their role in shaping a safer digital environment.
“In a field like cyber security, where not every situation has a clear rulebook, the Code can serve to navigate grey areas with integrity,” said Allam. “I also hope it becomes a shared foundation across the profession, encouraging accountability, fostering trust and reinforcing that how we work is just as important as what we do.”
Tech
Here’s What a Google Subpoena Response Looks Like, Courtesy of the Epstein Files

Last month, the Department of Justice released over 3 million documents related to convicted sex offender Jeffrey Epstein. While the dumps shed light on Epstein’s own social circle and activities, they also provide a rare window into the inner workings of a federal investigation, including how tech companies like Google respond to government requests for information.
WIRED found several grand jury subpoenas addressed to Google in the DOJ’s most recent release, along with files that appear to be Google data produced about specific users and letters on Google letterhead responding to specific subpoena requests.
Google declined to comment on the specific documents included in the dumps, but spokesperson Katelin Jabbari said in a written statement that the company’s “processes for handling law enforcement requests are designed to protect users’ privacy while meeting our legal obligations. We review all legal demands for legal validity, and we push back against those that are overbroad, including objecting to some entirely.”
The documents show how much the government will sometimes attempt to obtain without a judge’s sign-off, how Google pushes back against requests that it says are beyond what’s required by law, and what types of information the company has turned over about its users.
Secret by Design
Subpoenas are normally shrouded in secrecy. A 2019 letter signed by the then US attorney for the Southern District of New York and addressed to Google’s legal department prohibited the company by law from revealing the letter’s existence to Epstein coconspirator Ghislaine Maxwell, the subject of the subpoena, for 180 days from the date of the order. The letter also instructed Google to alert prosecutors if it planned to tell Maxwell about the existence of the order after the 180 days were up, “in case the investigation remains ongoing and the order needs to be renewed.”
Even when not required by law, prosecutors requested Google’s silence. A 2018 letter instructing Google to preserve all emails (including those in draft and trash folders) and Google Drive content associated with four gmail accounts also requested that Google not disclose the existence of the letter to anyone, including the people who owned the accounts. The letter also requested that Google notify federal prosecutors if the company intended to make a disclosure, so the prosecutors could “obtain a non-disclosure order if necessary.”
It’s unclear whether Google informed the account holders of the redacted emails after the 180-day period described in the 2019 letter were up. Google’s privacy and terms says that when it receives a request from a government agency, it will email the subject of that request before it discloses that information, unless it is prohibited by law.
Back to Basics
Many of the files included in the Epstein dumps were titled “GOOGLE SUBSCRIBER INFORMATION,” and contained the account name, recovery email address and phone numbers, what Google services the account can access, when the account was created, the “Terms of Service IP” address, and a log of IP address activity.
Mario Trujillo, a senior staff attorney at the Electronic Frontier Foundation, says that subscriber information requires the lowest legal bar for the government to access under the Stored Communications Act, a 1980s law that lays out a lot of the rules for what kind of information the government can access from electronic service providers like Google.
While some types of information, like email contents, require a search warrant under the law, “on the opposite end of that is basic subscriber information,” Trujillo says. The act explicitly permits the government to obtain that information with just a subpoena, which does not necessarily require judicial approval.
Tech
My Favorite Bluetooth Speaker Is on Sale for $50 Off Right Now

JBL makes a mean Bluetooth speaker, and the brand’s Flip series has been my all-time favorite for multiple generations. The JBL Flip 7 is its best yet, with good sound, a travel-ready size, and subtle but effective upgrades over the previous two models in both sound and features. I love this speaker and its nearly indestructible design, and now it’s finally getting some good sales. Right now, you’ll find it for $50 off its $150 retail price, the lowest we’ve seen it yet.
I used the Flip 5 as my go-to audio companion at home and on the road for years. The Flip 7 is better, providing even clearer and more powerful sound to enhance everything from barbecue jams to dialog as I watch movies from my PC in the hot tub (what can I say, I like to multi-task!). The Flip’s design works great for the hot tub since it’s fully dunkable, and offers convenient controls for my slippery hands when I need to adjust the volume or pause the fun.
The Flip 7 offers some cool new features, including a new detachable loop that breaks away with the press of a button (just make sure you don’t lose it), upgraded IP68 dust and water resistance, and a new shockproof casing tested for three-foot drops. The Flip line has always been pretty drop-friendly, and I can personally attest to dropping this thing a lot with no ill effects.
JBL has also begun to add Auracast to its new speaker line, a future-looking feature that uses a new Bluetooth protocol for latency-free transmission of an infinite number of devices. Auracast is still new, but it’s an extremely promising technology, and currently lets you connect the Flip 7 with other JBL Auracast speakers in tandem. The only downside is that JBL has done away with its older PartyBoost feature, so you can only group the Flip 7 with newer speakers like the Charge 6 and Clip 5.
As far as sound quality goes, this is a more refined Flip, with minor upgrades to instrumental definition, noticeable in instruments like brass, strings, and vocals. It’s not a big change over the Flip 6, but it’s good to see improvement, and the speaker has lost some of the more aggressive touch that sometimes led to minor distortion in older models. Like virtually any Bluetooth speaker, it will still distort if you push it too hard, but I clocked it at over 75 dB in my review without any audible issues.
You’ll also get a bit more battery life this time around, going from 12 hours in previous models to 14 (depending on volume), so you can take it off the grid for a bit longer. You can even push that up to 16 hours with its new Playtime Boost mode, though that cuts out some bass.
It all adds up to a sweet little package. It’s my first recommendation when anyone asks me about a great portable speaker, offering the perfect compromise between size, sound, and durability. While it’s been bouncing up and down in price lately, now’s a great time to catch it at the lowest price we’ve seen yet.
Power up with unlimited access to WIRED. Get best-in-class reporting and exclusive subscriber content that’s too important to ignore. Subscribe Today.
Tech
The Last Mystery of Antarctica’s ‘Blood Falls’ Has Finally Been Solved

There is a corner of Antarctica that looks like something out of a David Cronenberg movie. It’s located in the dry valleys of McMurdo, an immense frozen desert where, periodically, a jet of crimson liquid suddenly gushes from the dazzling white of the Taylor Glacier. They’re called the Blood Falls, and since their discovery in 1911 by geologist Thomas Griffith Taylor, they’ve fueled a century of scientific speculation.
Recently, a series of observations conducted since 2018 have clarified several mysteries, such as the nature of their reddish color and what keeps them liquid at almost –20 degrees Celsius. New research published this week in the journal Antarctic Science adds the final piece to the puzzle, clarifying what phenomena drive the falls to gush from underground.
The Science Behind the Blood Falls
At the time of their discovery, Taylor attributed the color to the presence of red microalgae. More than a century later, scientists have determined that the red is due to iron particles trapped in nanospheres along with other elements such as silicon, calcium, aluminum, and sodium. These were likely produced by ancient bacteria trapped underground in the area: Once in contact with air, the iron oxidizes, giving the mixture its characteristic rust color.
As for the presence of liquid water, it is actually a hypersaline brine, formed about 2 million years ago when the waters of the Antarctic Ocean receded from the valleys. The very high salinity of this brine prevents the water from freezing, thus allowing it to gush out periodically.
The New Discovery
With the temperature puzzle solved, the question remained as to what physically drove the fluid to erupt. The answer came from cross-referencing GPS data, thermal sensors, and high-resolution images collected in 2018 during an eruption. The analysis demonstrated that the Blood Falls are the result of pressure variations affecting the brine deposits beneath the glacier.
As Taylor Glacier slides downstream, the overlying ice mass compresses the subglacial channels, building up tremendous pressure. When the strain becomes unbearable, the ice gives way: Pressurized brine seeps into the crevices and is shot out in short bursts. Curiously, this release acts as a hydraulic brake, temporarily slowing the glacier’s march. With this discovery, the mysteries of the Blood Falls should finally have been solved, at least for now. The impact of global warming on this complex system in the coming decades remains unknown.
This story originally appeared on WIRED Italia and has been translated from Italian.
-

 Entertainment1 week ago
Entertainment1 week agoQueen Camilla reveals her sister’s connection to Princess Diana
-

 Tech1 week ago
Tech1 week agoRakuten Mobile proposal selected for Jaxa space strategy | Computer Weekly
-

 Politics1 week ago
Politics1 week agoRamadan moon sighted in Saudi Arabia, other Gulf countries
-
 Entertainment1 week ago
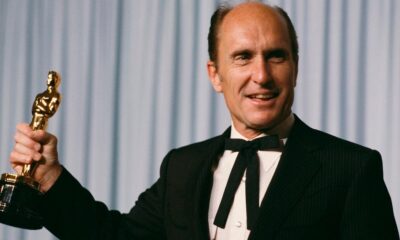
Entertainment1 week agoRobert Duvall, known for his roles in "The Godfather" and "Apocalypse Now," dies at 95
-

 Business1 week ago
Business1 week agoTax Saving FD: This Simple Investment Can Help You Earn And Save More
-

 Politics1 week ago
Politics1 week agoTarique Rahman Takes Oath as Bangladesh’s Prime Minister Following Decisive BNP Triumph
-

 Tech1 week ago
Tech1 week agoBusinesses may be caught by government proposals to restrict VPN use | Computer Weekly
-
 Sports1 week ago
Sports1 week agoUsman Tariq backs Babar and Shaheen ahead of do-or-die Namibia clash






