Tech
PromptSpy Android malware may exploit Gemini AI | Computer Weekly
An Android-specific malware targeting mobile device takeover appears to use generative AI (GenAI) services in its execution flows to maintain persistence on the victim’s smartphone, researchers at ESET have reported.
The raison d’être of the newly-discovered PromptSpy malware is to deploy and run a virtual network computing (VNC) module on the victim’s device, enabling attackers to capture lockscreen data, gather device information, take screenshots and record activity, and block uninstallation.
But to do so it must first establish persistence on the device, and it is here that GenAI comes into play, said the ESET team. They claimed that PromptSpy uses the onboard Google Gemini service to interpret onscreen elements and provide it with dynamic instructions on how to execute a specific gesture that will enable it to remain in the device’s recent app list. This, in theory, stops it being easily swiped away by the user or killed by the system.
ESET researcher Lukáš Štefanko said that while GenAI plays only a minor role in PromptSpy’s execution flow it could have a significant impact on the malware’s potential adaptability.
“Since Android malware often relies on UI-based navigation, leveraging generative AI enables threat actors to adapt to more or less any device, layout, or operation system version, which can greatly increase the pool of potential victims,” he said.
“Even though PromptSpy uses Gemini in just one of its features, it still demonstrates how implementing these tools can make malware more dynamic, giving threat actors ways to automate actions that would normally be more difficult with traditional scripting.”
Štefanko said that based on localisation clues and distribution vectors, PromptSpy seems to be run by a financially-motivated threat actor, exploits Morgan Chase branding, and may primarily target users in Argentina.
However, he also stressed that the malware has not yet popped up in ESET’s wider telemetry, which may suggest it is a proof of concept (PoC) at this point in time. Nor has it been observed on the Google Play store – it can only be downloaded by a dedicated website that its victims would need to be conned into visiting.
Computer Weekly understands that Štefanko’s discovery has been shared with Google via the App Defense Alliance programme, and Android users should already be automatically protected against known versions of it by the Google Play Protect service.
In the unlikely event that PromptSpy has somehow infected their device, victims can remove it by rebooting their phone into Safe Mode, which disables third-party applications and enables them to be uninstalled normally.
GenAI malwares. Hype or threat?
PromptSpy is not the first alleged malware exploiting GenAI to have been surfaced by the ESET team, which last year also discovered a ransomware – named PromptLock – which ran a locally accessible AI language model to autonomously plan, adapt and execute a ransomware attack.
PromptLock turned out to be the fruit of a research project conducted by a team of PhD and post-doctoral researchers at New York University’s (NYU’s) Tandon School of Engineering – specifically to illustrate the potential dangers of AI malwares.
Other supposed AI malwares found so far include FruitShell, which included GenAI promps to bypass detection and analysis, PromptSteal or Lamehug, a data miner linked to Russian state activity that queried a GenAI model to generate commands for execution via the Hugging Face API, and QuietVault, a credential stealer targeting GitHub and NPM tokens. Details on these malwares were published by the Google Threat Intelligence Group (GTIG) in November 2025.
However, their discovery has prompted widespread debate as to exactly how much of a threat such malwares really are, with some researchers arguing that the industry is overblowing their significance.
Tech
One of Our Favorite 360 Cams Is 35 Percent Off

Tired of taking your action camera on an adventure, only to get home and find out you missed the action with a bad angle? One option is to switch to a 360-degree action cam, so you can capture all of the action and then edit down to just the good stuff later. One of our favorite options, the DJI Osmo 360, is currently available for just $390 on Amazon, a $209 discount from its usual price, and it comes with a selfie stick and an extra battery.
The DJI Osmo 360 achieves its impressive all-around video quality by leveraging a pair of 1/1.1-inch sensors, larger than some other offerings, and by supporting 10-bit color. You can really see that in the camera’s output, with colors that are vivid and bold, to the point that you may need to dial them back a bit in post if you want something more natural. With support for up to 50 frames per second at 8K when recording in 360 degrees, or 120 fps at 4K when shooting with only one sensor, you’ll have plenty of material to work with. In our testing, it ran for just shy of two hours at 30 fps, which is also around the time the internal storage had filled up anyway.
If you plan on catching any serious discussions with your Osmo 360, you’ll be pleased to know it connects directly to DJI’s line of wireless lavalier microphones, including the excellent and frequently discounted DJI Mic 2 and Mic Mini. If you want to mount it to something other than the included 1.2-meter selfie stick, it has both DJI’s magnetic attachment system and a more traditional ¼”-20 tripod mount. The DJI Mimo app lets you control the camera and adjust any settings, and there’s even a simple editor for on-the-fly production. For desktop users, DJI Studio has even more in-depth settings and editing options, in case you don’t want to pay for Premiere.
The DJI Osmo 360 is one of our favorite action cameras, and is particularly appealing at the discounted price point, but make sure to check out our full review for more info, or head over to our full roundup to see what else is available.
Tech
Artemis II: Everything We Know as Its Crew Approaches the Far Side of the Moon

On day six of its mission, Artemis II is closing in on the far side of the moon. Meanwhile, the historic journey has not been without fascinating and curious stories, from the images and videos that its four crew members have shared with the world to the inevitable unforeseen events—including a tricky toilet situation.
A few hours before the crew begins its lunar flyby, here’s how things are going on Artemis II.
When Will They Reach the Far Side of the Moon?
While Artemis II won’t actually land on the moon (that won’t happen until Artemis IV), that does not make this mission any less compelling. Once the Artemis II astronauts finish flying over the dark side of the moon, they will have the historic distinction of being the humans who have traveled the farthest from Earth.
They will also test all the systems needed for future lunar missions, validating life support, navigation, spacesuits, communications, and other human operations in deep space.
But when are they supposed to reach this far-off point? First, the Orion capsule reached what is known as the moon’s “sphere of influence” on Sunday night. This is the point where the moon’s gravitational force is stronger than the force of the Earth.
At present, Orion is circling the moon. Once the capsule is on the dark side of the moon, approximately 7,000 kilometers from the surface, communications with Earth will be interrupted. For six hours, they will be able to view the far side of the moon, something no human being has ever seen with their own eyes—not even the astronauts of the Apollo program, as this region of the moon was always too dark or difficult for them to reach.
That six-hour flyby of the dark side of the moon is expected to begin Monday, April 6, at 2:45 pm EDT and 7:45 pm London time.
After that, the capsule will use the moon’s gravity to propel itself back to Earth. Splashdown, when the astronauts reach Earth, is scheduled for April 10 in the Pacific Ocean, not far from the coast of California, the tenth day of the mission.
Remember that you can follow the live broadcast of the Artemis II mission from NASA’s official channels.
What Has Happened so Far?
Since its successful launch on April 1 from Kennedy Space Center, the Artemis II crew has shared several spectacular photos, such as the featured image in this post, which shows mission specialist Christina Koch looking down at Earth through one of Orion’s main cabin windows.
This incredible photo of a Earth, taken on April 2, went viral on social media, referencing the famous “Blue Marble” image captured by the Apollo 17 astronauts in 1972.
View of Earth taken by astronaut Reid Wiseman from the window of the Orion spacecraft after completing the translunar injection maneuver on April 2, 2026.Photograph: Reid Wiseman/NASA/Getty Images
Tech
The DOJ Misled a Judge About How It’s Using Voter Roll Data
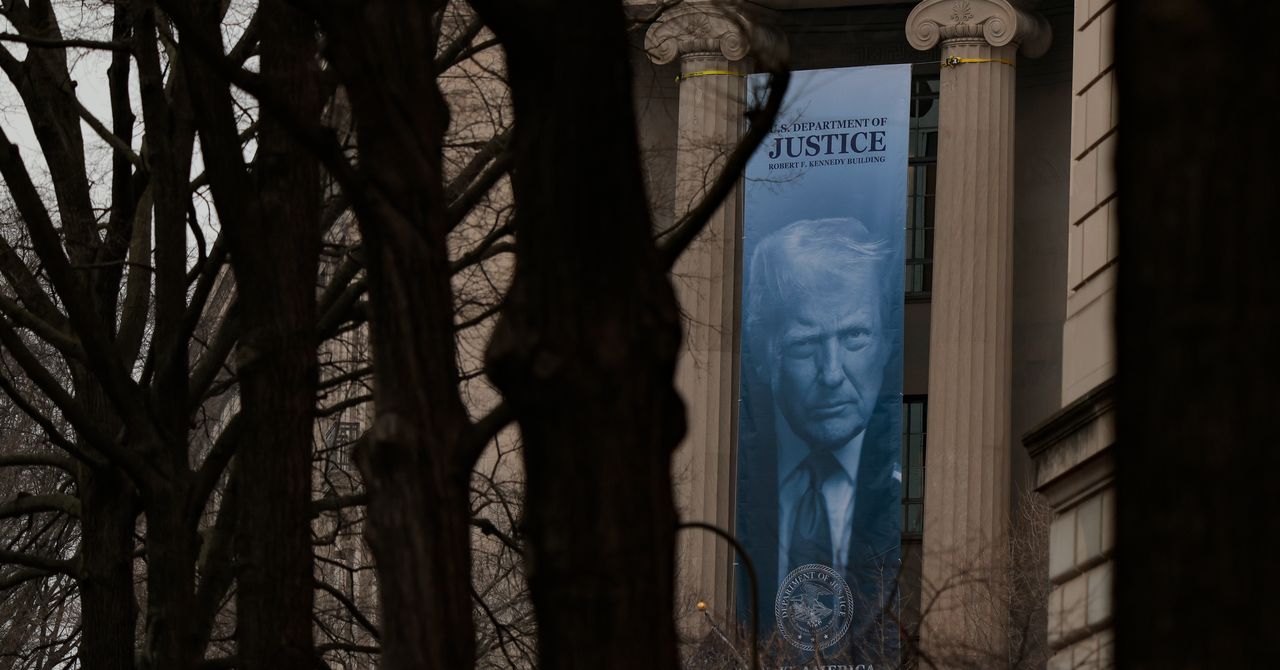
Last week in Rhode Island, in a hearing over the Trump administration’s efforts to access the state’s unredacted voter lists, US district judge Mary McElroy asked a Department of Justice lawyer what the agency had been doing with the voter roll data it already amassed from other states in recent months.
“We have not done anything yet,” said Eric Neff, the acting chief of the agency’s voting section, a core part of the DOJ’s civil rights division that focuses on enforcing federal laws that protect the right to vote. Neff added that the data the DOJ collected from states—which can include Social Security numbers, drivers licenses, dates of birth, and addresses—was being kept separate.
“The United States is taking extra concern to make sure that we’re complying with the Privacy Act in every conceivable way,” Neff added. The Privacy Act of 1974 regulates how government agencies collect and use personally identifiable information about US residents.
But Neff was not telling the truth: The DOJ, he later admitted, was pooling the data and already analyzing it to identify voting irregularities.
In a court document filed on March 27, Neff walked back his claims. “The United States represented that each data set was stored separately,” Neff wrote. “The United States also stated that no analysis had yet been conducted on the data. To correct and clarify the record, preliminary internal data analysis of the nonpublic voter registration data has begun. In particular, the Civil Rights Division has begun the process of identifying and quantifying the number and type of duplicate and deceased registered voters in each state.”
The revelation confirms what was widely speculated, which is that the DOJ appears to be pooling the data and using it to identify potential issues with suspected voting irregularities ahead of the midterms, which is a core part of Trump’s broad attack on elections.
Neff and the DOJ did not respond to repeated requests for comment.
Critics have grown increasingly concerned about the DOJ’s voting section, which has undergone a stark transformation since President Donald Trump has retaken office. A newly installed coterie of inexperienced but ultra-loyal lawyers in the DOJ’s voting section, many of whom have supported election denial conspiracy theories, have spent their time on forcing states to hand over their voter roll information.
The initiative began in May last year, when the Department of Justice sent letters to election officials in at least 48 states and Washington, DC, asking for unredacted voter rolls. Some Republican-led states immediately handed over the information, but dozens of others pushed back. As a result, Neff and his colleagues have sued 30 states, asking courts to force them to hand over the information. So far, courts have sided with the states, with judges already dismissing cases in California, Michigan, and Oregon.
In many of the lawsuits, state election officials pointed out the huge security risk involved in sharing such sensitive data, especially when it was unclear how the data would be stored or who it would be shared with. “We still have no idea what the government is doing with this data,” says David Becker, the head of the Center for Election Innovation and Research and a former Justice Department lawyer. “No idea where it is being stored, how it is being protected, or who has access to it. This data is incredibly sensitive. If someone has any of these three data points on any of us, Social Security number, driver’s license number, or date of birth, they can wreck us financially. This is why the states protect this data, and they do a good job of it.”
-

 Sports1 week ago
Sports1 week agoUSMNT handed reality check by Doku, Belgium ahead of World Cup
-

 Sports1 week ago
Sports1 week ago2026 NCAA men’s hockey tournament: Schedule, results
-
Uncategorized4 days ago
[CinePlex360] Please moderate: “Trump signals p
-
Uncategorized1 week ago
[CinePlex360] Please moderate: “Further tariff
-

 Entertainment3 days ago
Entertainment3 days agoJoe Jonas shares candid glimpse into parenthood with Sophie Turner
-

 Tech3 days ago
Tech3 days agoOur Favorite iPad Is $50 Off
-

 Sports1 week ago
Sports1 week agoMan City show why they are worthy WSL title winners as tired United wilt
-

 Entertainment1 week ago
Entertainment1 week agoDemystifying the PTI






