Tech
Western cyber alliances risk fragmenting in new world order | Computer Weekly

The global cyber threat landscape was defined by fragmentation in 2025, driven in no small part by widening geopolitical fractures that threatened the 80-year-old rules-based international order that has kept the peace – at least in the global north – since the end of the Second World War, according to a report.
In a cyber threat report published last week, Recorded Future’s Insikt Group explored how the conduct of powerful nations – aptly demonstrated by the possibility of a unilateral US takeover of Greenland, threatening the integrity of the Nato alliance – is causing knock-on effects in the cyber world as long-standing security frameworks appear increasingly precarious.
Indeed, in some circumstances, legal ambiguity around US actions, particularly those taking place in the Caribbean and Venezuela, has in fact caused some of America’s core allies, including the UK, to restrict intelligence sharing. Recorded Future said that strained transatlantic relations were limiting coordinated responses to wider crises such as Russia’s four-year war on Ukraine, and that these geopolitical dynamics are directly shaping state behaviour in cyberspace.
Meanwhile, sustained law enforcement pressure led to some big wins last year in the form of disruptions and takedowns of cyber criminal infrastructure, along with arrests, but this is now resulting in a more decentralised, modular criminal ecosystem that, unfortunately, is also more resilient.
And on the technological front, this fragmentation was demonstrated by the growing split between China and the US as the two great powers vie for AI dominance.
“In 2025, Insikt Group tracked how cyber activity shifted from a primary focus on espionage toward increased use of cyber capabilities for signalling, coercion and disruption in both kinetic conflicts and grey-zone scenarios,” said the report’s authors.
“Securing access to identity systems, cloud environments and edge infrastructure emerged as a central feature of interstate competition, reflecting the growing strategic value of persistent digital access and pre-positioning.
“Disruption was equally visible in the information environment. Insikt Group observed hacktivist groups, patriotic volunteers and influence networks playing a growing role in conflicts involving Israel-Iran, India-Pakistan, Thailand-Cambodia, and Russia-Ukraine.
“These actors operated with varying degrees of state alignment, but consistently contributed to a threat landscape in which genuine intrusions, exaggerated claims and disinformation reinforced one another,” they said.
Speaking at the report’s launch at the annual Munich Security Conference in Germany, Recorded Future chief security and intelligence officer Levi Gundert said: “Uncertainty is no longer episodic – it’s the operating environment.
“As geopolitical norms weaken, state objectives, criminal capability and private-sector technology are increasingly reinforcing one another, compressing warning timelines and expanding plausible deniability. AI is accelerating that dynamic, not through autonomous attacks, but by scaling deception and eroding trust inside decision-making processes.
“In 2026, cyber risk will be defined less by singular events and more by persistent, fragmented pressure that reshapes competition, escalation, and stability over time.”
Cyber ops a routine tool
Against these general dynamics, Recorded Future said cyber operations are now becoming established as a routine tool of geopolitical competition, alongside more traditional instruments such as sanctions, tariffs or asset seizures.
“The cumulative effect is an international system with higher tolerance for risk and fewer constraints on escalation. For governments and businesses alike, resilience rather than stability is now the baseline operating assumption,” the team said.
This year, the report said, state-sponsored cyber operations will coalesce around low-visibility access and reconnaissance operations as a precursor to outright conflict, said Recorded Future co-founder Christopher Ahlberg.
“Cyber operations are no longer preparation for conflict – they are part of conflict. What we’re seeing is that adversaries are logging in, not hacking in. This is a shift toward access, influence and leverage that can be activated at moments of political or military tension, often below the threshold of traditional response,” he said.
Russia, said Recorded Future, will move away from malware-driven campaigns towards credential-based intrusions and the abuse of legitimate services such as identity platforms. This approach allows hackers to escalate to outright disruption while maintaining plausible deniability for their paymasters, and making it harder for security teams to detect them.
Chinese actors, meanwhile, are likely to expand from data theft towards information operations bombarding their targets with large volumes of AI slop in a form of “flooding the zone”. According to Recorded Future’s analysts, Beijing already has established doctrines on AI-driven “psychographic targeting” with the intent of eroding its rivals’ resolve through bespoke, emotionally provocative operations that complement its underlying attacks.
The Iranians, the report predicted, will remain largely focused on regional influence operations, with continued use of hacktivist proxies. Despite recent internal upheaval, and the US’s response to this, more widespread disruptive operations are probably unlikely, although they should not necessarily be ruled out.
North Korea will remain an active and dangerous cyber actor, with its operations likely to continue targeting workforce infiltration to enable data theft and, critically, revenue generation going forward.
Finally, defenders should also be on the lookout for commercial spyware, which will remain a key enabler of state-backed cyber risk. Such tools – the most infamous example being Israel-based NSO’s Pegasus malware – also muddy the waters somewhat in that they are now widely used by many governments against their own people.
Tech
A Single Strike Won’t Shut Off the Gulf’s Desalination System
Across the region, facilities tied to water and power—including desalination plants—have been damaged or exposed to risk as Iranian strikes extend beyond traditional targets.
A single strike, however, is unlikely to shut off the gulf’s water supply. The system is designed to absorb isolated disruption, but sustained or multisite attacks would begin to strain supply far more quickly.
“In the Gulf, desalination is built with enough breathing room that losing one plant doesn’t immediately show up at the tap,” says Rabee Rustum, professor of water and environmental engineering at Heriot-Watt University Dubai.
In Kuwait, Iranian drone attacks have damaged two power and desalination facilities and ignited fires at two oil sites. Other sites, including Fujairah in the UAE, have been identified as potentially exposed.
“Striking desalination plants would be a strategic move, but it would also come very close to, and in some cases cross, a red line,” says Andreas Krieg, senior lecturer at the School of Security Studies at King’s College London.
Water infrastructure, Krieg explains, occupies a distinct category. “Water infrastructure is not just another utility. In places that depend on desalination, it underpins civilian survival, public health, hospital function, sanitation, and basic state legitimacy.”
Krieg notes that international humanitarian law gives special protection to civilian objects and to objects indispensable to the survival of the civilian population. “Which is precisely why attacks on water systems carry such grave legal and moral weight,” Krieg adds.
The incidents highlight a structural reality: Desalination is central to water supply in the gulf, and disruption carries immediate implications for daily life.
How the System Absorbs Disruption
At first glance, desalination appears vulnerable. Shut down a plant, and supply is reduced. In practice, the system is designed with layers of redundancy.
Plants operate across multiple locations, allowing output to be redistributed if one facility slows down. Water is also stored at different points across the network, including central reservoirs and building-level tanks, creating a buffer that delays disruption.
According to a statement to WIRED Middle East by Veolia, an environmental services provider whose technologies account for nearly 19 percent of desalination capacity in the region, “the region’s water supply is diversified thanks to a network of numerous facilities distributed along the coastline.”
The company adds that distribution systems are interconnected, allowing plants to “support and substitute for one another when necessary,” helping maintain continuity of service.
In the UAE, storage capacity typically covers around one week, while in other parts of the region it may be limited to two to three days, Veolia says.
In practice, this means the system can absorb disruption for a limited period. Once reserves are depleted, water supply depends on whether plants can continue producing enough water to meet demand.
The System That Produces Water
Unlike most regions, the Gulf does not rely on rivers or rainfall. It depends on a network of desalination plants along its coastline that convert seawater into potable water on a continuous basis.
Seawater is drawn into treatment facilities, filtered and processed either through reverse osmosis—forcing it through membranes to remove salt and impurities—or through thermal methods that evaporate and condense water. The resulting supply is distributed through pipelines, stored in reservoirs, and delivered to homes, hospitals, and industry.
This is not a flexible system. It is designed to operate continuously, producing water at a scale that sustains cities, industrial activity, and essential services. Gulf states produce roughly 40 percent of the world’s desalinated water, operating more than 400 plants across the region.
Dependence varies by country but is high everywhere. In the UAE, desalination accounts for 41 to 42 percent of total water supply, while in Kuwait, it provides around 90 percent of drinking water, and in Saudi Arabia, approximately 70 percent.
When Disruption Becomes Visible
For residents, disruption would not be felt immediately—water would continue to flow.
Rustum explains that buildings are supported by internal storage and pumping systems, meaning early changes in supply may not be apparent. In many cases, water pressure remains stable, even as the wider system adjusts.
Tech
Border Patrol Agents Sold Challenge Coins With ‘Charlotte’s Web’ Characters in Riot Gear
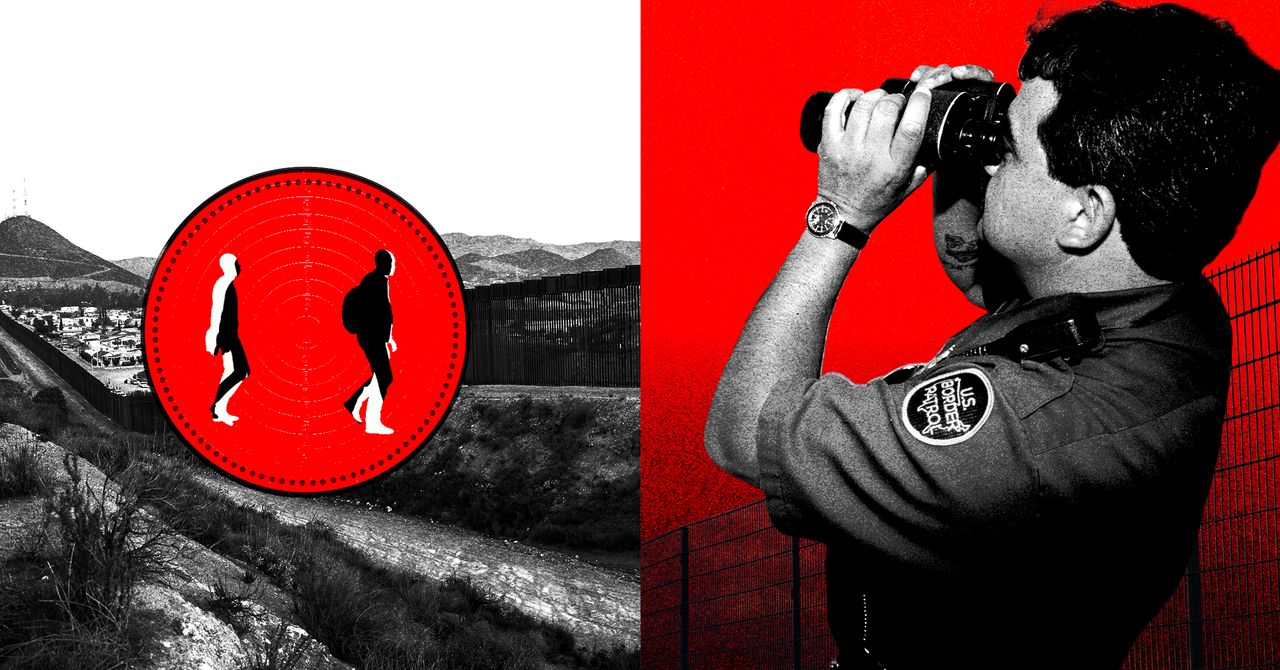
US Border Patrol agents are raising money by selling coins that commemorate last year’s wave of immigration enforcement “operations” across the country, along with other merchandise. The funds are for nonprofit organizations that list Border Patrol buildings as their address in IRS paperwork. At least two of the organizations have dedicated US Customs and Border Protection email addresses.
The front side of one coin for sale reads, “NORTH AMERICAN TOUR 2025,” along with the acronyms for US Border Patrol and the acronym for “fuck around and find out”—a phrase that was initially popularized by the far-right group the Proud Boys and has been used by various Trump officials. In the center, the coin depicts a gas mask, a riot control smoke grenade, and a pepper ball launcher. On the other side, the coin appears to have a portrait of Border Patrol’s now retired commander-at-large, Gregory Bovino, with his arm raised in a salute, along with the text “COMING TO A CITY NEAR YOU!” It lists seven cities, many of which actually saw federal enforcement surges in 2025: Chicago, Los Angeles, Memphis, Phoenix, Portland, Charlotte, and Atlanta.
The coin is for sale by Willcox Morale Welfare and Recreation, a nonprofit that the IRS most recently declared tax-exempt during the Biden administration and whose address on IRS paperwork matches that of the Willcox Border Patrol Station in Arizona. A request for comment sent to Willcox MWR’s dedicated CBP email address went unanswered.
Employees of the Department of Homeland Security, the parent agency for Border Patrol, are allowed to start private, not-for-profit employee associations within DHS, so long as they get formally recognized by the agency and follow certain rules. According to DHS policies, officially recognized groups can fundraise using government property and create merchandise with the agency’s name and logos–but they have to receive advance approval from the agency.
Willcox MWR is just one of several groups across the country that cater to Border Patrol agents and refer to themselves as MWRs, a reference to the US military’s “morale, welfare and recreation” programs. The groups tend to throw holiday events and retirement parties, and sometimes raise money for the families of agents going through hard times, including those not getting paid during the current shutdown.
Many MWRs also sell customized medallions known as “challenge coins” that commemorate specific teams or events. While anyone, including CBP alumni, can design and sell coins, current DHS employees are not supposed to use government resources to sell ones that use the agency’s seals or logos without permission, or ones that the agency considers inappropriate or unprofessional.
CBP did not provide comment about its relationship to Willcox MWR or any other nonprofit mentioned in this story, nor whether the agency had green-lit the “North American Tour” coin design, ahead of publication.
Under Willcox MWR’s Facebook post about the “North American Tour” coin, someone named Juan Diego commented, “Sign up SDC BK5 MWR for 10.”
“Shoot us an email,” someone managing the Willcox MWR account replied, giving out what appeared to be a dedicated cbp.dhs.gov email address for the group.
SDC BK5 MWR, also a registered nonprofit, lists an address on its website that matches that of a government facility in Chula Vista, California. It says on its site that it was started by San Diego Sector Border Patrol agents and sells custom merchandise “designed to raise funds for morale and relief efforts.”
Diego did not respond to a request for comment.
The SDC BK5 MWR website has listings for over 200 different products in addition to the North American Tour coin. One of those listings was a “Chicago Midway Blitz” challenge coin in the shape of a gas mask that doubles as a bottle opener. Embossed around the edges of the coin are the names of several municipalities and neighborhoods caught up in DHS’s immigration enforcement surge of the same name last fall. Like the North American Tour coin, it features the US Border Patrol logo and the acronym for “fuck around and find out.” Opponents of the Trump administration’s immigration enforcement activity in Illinois are unamused.
Tech
One of Our Favorite 360 Cams Is 35 Percent Off

Tired of taking your action camera on an adventure, only to get home and find out you missed the action with a bad angle? One option is to switch to a 360-degree action cam, so you can capture all of the action and then edit down to just the good stuff later. One of our favorite options, the DJI Osmo 360, is currently available for just $390 on Amazon, a $209 discount from its usual price, and it comes with a selfie stick and an extra battery.
The DJI Osmo 360 achieves its impressive all-around video quality by leveraging a pair of 1/1.1-inch sensors, larger than some other offerings, and by supporting 10-bit color. You can really see that in the camera’s output, with colors that are vivid and bold, to the point that you may need to dial them back a bit in post if you want something more natural. With support for up to 50 frames per second at 8K when recording in 360 degrees, or 120 fps at 4K when shooting with only one sensor, you’ll have plenty of material to work with. In our testing, it ran for just shy of two hours at 30 fps, which is also around the time the internal storage had filled up anyway.
If you plan on catching any serious discussions with your Osmo 360, you’ll be pleased to know it connects directly to DJI’s line of wireless lavalier microphones, including the excellent and frequently discounted DJI Mic 2 and Mic Mini. If you want to mount it to something other than the included 1.2-meter selfie stick, it has both DJI’s magnetic attachment system and a more traditional ¼”-20 tripod mount. The DJI Mimo app lets you control the camera and adjust any settings, and there’s even a simple editor for on-the-fly production. For desktop users, DJI Studio has even more in-depth settings and editing options, in case you don’t want to pay for Premiere.
The DJI Osmo 360 is one of our favorite action cameras, and is particularly appealing at the discounted price point, but make sure to check out our full review for more info, or head over to our full roundup to see what else is available.
-
Uncategorized4 days ago
[CinePlex360] Please moderate: “Trump signals p
-

 Sports1 week ago
Sports1 week ago2026 NCAA men’s hockey tournament: Schedule, results
-
Uncategorized1 week ago
[CinePlex360] Please moderate: “Further tariff
-

 Tech3 days ago
Tech3 days agoOur Favorite iPad Is $50 Off
-

 Entertainment3 days ago
Entertainment3 days agoJoe Jonas shares candid glimpse into parenthood with Sophie Turner
-

 Politics7 days ago
Politics7 days agoTrump considers asking Arab allies to help to pay for Iran war
-

 Sports1 week ago
Sports1 week agoHow Arizona beat Purdue and Illinois defeated Iowa in Saturday’s Elite Eight
-

 Sports1 week ago
Sports1 week agoFakhar Zaman denies ball-tampering charge in PSL match | The Express Tribune






