Tech
Resilience for resilience: Managing burnout among cyber leaders | Computer Weekly

While organisations invest in cyber resilience, the resilience of those leading the charge, chief information security officers (CISOs), is often overlooked. The CISO role is consistently ranked among the most high-pressure in the C-suite. According to ISACA’s State of Cybersecurity 2025 report, 66% of cyber security professionals say their role is more stressful now than it was five years ago.
CISOs often operate in environments where security is underfunded, under prioritised, or misunderstood at the board and C-suite level. A lack of senior-level buy-in trickles down into:
- Budget constraints that limit the scope and impact of the CISO function, including resources for tooling and automation.
- Skills shortages and restrictive operating models that prevent effective delegation.
- Strategic misalignment, where short-term delivery is prioritised over long-term business resilience and customer outcomes.
This creates a vicious cycle: CISOs are held accountable for outcomes without sufficient resources or executive backing, leading to stress, frustration, and burnout.
Security is still often perceived as a business inhibitor until a significant incident occurs. The constant need to ‘sell’ cyber security within conflicting C-suite priorities burns effort, while rising public and stakeholder awareness amplifies the pressure.
For example, in finance, CISOs face strict regulation and intense board and public scrutiny. In the public sector, bureaucratic friction and procurement constraints can complicate strategic investments, leaving CISOs exposed both operationally and reputationally.
To move the needle on cyber security, CISOs must go beyond technical defences and reposition security as a strategic business enabler. This starts with shifting board and C-suite mindsets, through education, influence, and persistent engagement, to see cyber security as integral to innovation and resilience.
Developing executive-level dashboards that articulate the organisation’s cyber security posture can provide visibility into progress, operational resilience, and how security initiatives align with strategy and enterprise goals. Equally critical is framing cyber risk in business terms, translating technical threats into quantifiable impacts on revenue, regulation, and user impact. This kind of communication elevates the CISO’s role from IT steward to strategic partner.
The ever-changing cyber landscape
Unlike other leadership roles, the CISO must constantly adapt to overlapping and complex regulations, such as the UK Data Protection Act, the EU General Data Protection Regulation (GDPR), and frameworks like DORA and FCA PS21/3. They also face threats including ransomware and AI-driven attacks. Additionally, CISOs must manage expanding attack surfaces resulting from offshoring, cloud adoption, and increasing third-party dependencies. Compounding these challenges are rapid technological shifts, such quantum computing and generative AI.
CISOs must simultaneously manage today’s risk, ensure operational integrity, steer future strategy, and monitor an evolving landscape, all in real time. The pace of threats means new systems, technologies, or vulnerabilities can be targeted within hours of going live, leaving little margin for error or recovery.
The rapid pace of digital transformation, while essential for business growth, expands risk and complexity beyond what traditional operating models can accommodate. CISOs must adapt at speed, safeguarding organisations against increasingly sophisticated threats.
In healthcare, for example, CISOs face ransomware threats that directly impact patient safety. In large global organisations, tool sprawl and third-party outsourcing increase complexity and reduce visibility, leaving CISOs with fragmented control capabilities.
Building a stronger cyber security posture requires a unified, risk-based approach that clearly delegates controls and accountability across teams and partners. By layering zero-trust architecture with continuous third-party monitoring, organisations can shrink their attack surface and keep vendor risk in check. Running threat simulation exercises further sharpens the security team’s agility, preparing them to respond to emerging threats before they escalate.
Systemic illusions and cognitive overload
While strategic misalignments and resource constraints put the CISO under pressure, the issue of a mismatch between accountability and authority persists. CISOs are expected to secure systems and manage risk across business units, outsourced services and technologies they don’t directly control which leaves them accountable for outcomes without clear decision rights or contractual levers.
The illusion of control arises when CISOs are accountable for cyber security risk but lack authority to enforce controls, especially across fragmented, outsourced, or federated environments. Their role shifts from decisive action to constant negotiation, increasing stress and accountability without power to drive change. In some public sector organisations, the CISO role is secondary or voluntary, often combined with IT delivery, forcing individuals to prioritise security against operational delivery.
Driving change in cyber security leadership demands structural and cultural alignment. Establishing cross-functional governance and defining risk ownership between security and business leaders ensures that cyber risk becomes part of everyday executive decision-making. Embedding security deliverables and risk criteria into all business projects further reinforces that cyber security is a shared accountability. At the same time, supporting the CISO’s own resilience and wellbeing is crucial. Access to peer networks, executive coaching, and setting clear boundaries can help mitigate cognitive overload.
From burnout to balance
CISO burnout is not a personal weakness but a consequence of conflicting organisational design. Until cyber security is embedded as a core business function, CISOs will continue to face impossible expectations and fragmented authority. Organisations must redefine accountability and empower CISOs with real decision-making authority, and invest in resilience, for both their people and their strategies. Only then will cyber security leadership become a source of business strength, rather than a burnout risk.
John Skipper and Farrukh Ahmad are cyber security experts at PA Consulting
Tech
Light-activated gel could impact wearables, soft robotics, and more
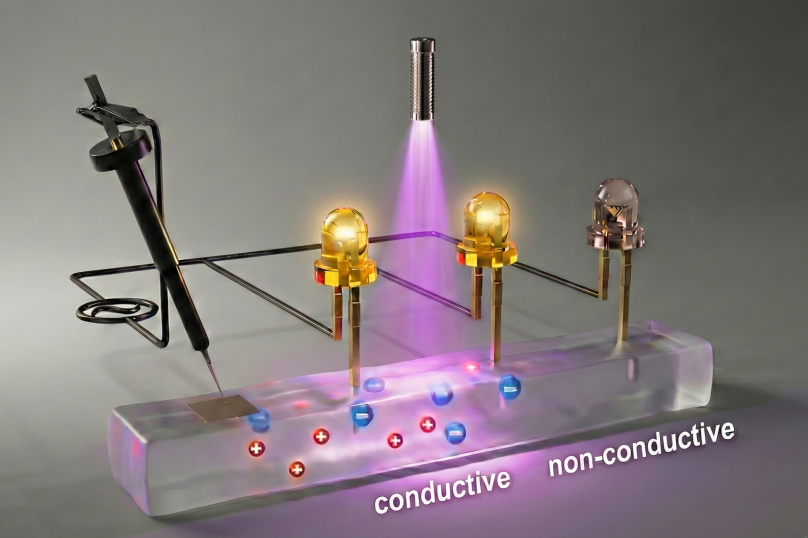
Consider the chief difference between living systems and electronics: The first is generally soft and squishy, while the latter is hard and rigid. Now, in work that could impact human-machine interfaces, biocompatible devices, soft robotics, and more, MIT engineers and colleagues have developed a soft, flexible gel that dramatically changes its conductivity upon the application of light.
Enter the growing field of ionotronics, which involves transferring data through ions, or charged molecules. Electronics does the same, with electrons. But while the latter is well established, ionotronics is still being developed, with one huge exception: living systems. The cells in our bodies communicate with a variety of ions, from potassium to sodium.
Ionotronics, in turn, can provide a bridge between electronics and biological tissues. Potential applications range from soft wearable technology to human-machine interfaces
“We’ve found a mechanism to dynamically control local ion population in a soft material,” says Thomas J. Wallin, the John F. Elliott Career Development Professor in MIT’s Department of Materials Science and Engineering and leader of the work. “That could allow a system that is self-adaptive to environmental stimuli, in this case light.” In other words, the system could automatically change in response to changes in light, which could allow complex signal processing in soft materials.
An open-access paper about the work was published online recently in Nature Communications.
A growing field
Although others have developed ionotronic materials with high conductivities that allow the quick movement of ions, those conductivities cannot be controlled. “What we’re doing is using light to switch a soft material from insulating to something that is 400 times more conductive,” says Xu Liu, first author of the paper and former MIT postdoc in materials science and engineering who is now an incoming assistant professor at King’s College London.
Key to the work is a class of materials known as photo-ion generators (PIGs). These can become some 1,000 times more conductive upon the application of light. The MIT team optimized a way to incorporate a PIG into polyurethane rubber by first dissolving a PIG powder into a solvent, and then using a swelling method to get it into the rubber.
Much potential
In the material reported in the current work, the change in conductivity is irreversible. But Liu is confident that future versions could switch back and forth between insulating and conducting states.
She notes that the current material was developed using only one kind of PIG, polymer (the polyurethane rubber), and solvent, but there are many other kinds of all three. So there is great potential for creating even better light-responsive soft materials.
Liu also notes the potential for developing soft materials that respond to other environmental stimuli, such as heat or magnetism. “We’re inspired to do more work in this field by changing the driving force from light to other forms of environmental stimuli,” she says.
“Our work has the potential to lead to the creation of a subfield that we call soft photo-ionotronics,” Liu continues. “We are also very excited about the opportunities from our work to create new soft machines impacting soft wearable technology, human-machine interfaces, robotics, biomedicine, and other fields.”
Additional authors of the paper are Steven M. Adelmund, Shahriar Safaee, and Wenyang Pan of Reality Labs at Meta.
Tech
Dark Matter May Be Made of Black Holes From Another Universe

A recent cosmological model combines two of the most eccentric ideas in contemporary physics to explain the nature of dark matter, the invisible substance that makes up about 85 percent of all matter in the universe. To understand it, it’s necessary to look beyond the Big Bang we all know and consider two concepts that rarely intersect: cyclic universes and primordial black holes.
A Different Kind of Multiverse
There are different versions of the “multiverse.” The most popular model—that of the Marvel Cinematic Universe—proposes that there are as many universes as there are possibilities and that these versions of reality are parallel. Physics proposes something more sober and mathematically consistent: the cosmic bounce.
In this model, the universe is not born from a singularity, but expands, contracts, and expands again in an endless cycle. Each “universe” is not parallel, but sequential—that is, one arises from the ashes of the previous one.
Is it possible for something to survive the end of its universe and endure into the next? According to a paper published in Physical Review D, yes. Author Enrique Gaztanaga, a research professor at the Institute of Space Sciences in Barcelona, shows that any structure larger than about 90 meters could pass through the final collapse of a universe and survive the rebound. These “relics” would not only persist, but could also seed the formation of giant, unexplained structures observed in the early stages of the present-day universe. Moreover, they could be the key to understanding dark matter.
For decades, the dominant explanation for dark matter has been that it is an unknown particle or particles. But after years of experiments without direct detections, physicists have begun to explore alternatives. One of them proposes that dark matter is not an exotic particle, but an abundant population of small black holes that we overlook.
The idea is appealing, but it has a serious problem. For these black holes to explain dark matter, they would have to exist from the earliest moments of the universe, long before the first stars could collapse. There are indications that these objects could exist, but a convincing physical mechanism to explain their origin is lacking.
A Universe Born With Black Holes
This is where Gaztanaga’s newly proposed model shines. If cosmic bouncing allows compact structures to survive the collapse of the previous universe, then the current universe would have already been born with pre-existing black holes. They would not have to have been generated by extreme fluctuations or finely tuned inflationary processes, but would simply have been there from the first instant.
The assumption has the potential to solve two riddles at once: the origin of black holes and the nature of dark matter. If this model is correct, dark matter would not be a mystery of the early universe but rather a legacy of a cosmos that predates our own.
“Much work remains to be done,” Gaztanaga, also a researcher at the Institute of Cosmology and Gravitation at the University of Portsmouth, said in an article for The Conversation. “These ideas must be tested against data—from gravitational-wave backgrounds to galaxy surveys and precision measurements of the cosmic microwave background.”
“But the possibility is profound,” he added. “The universe may not have begun once, but may have rebounded. And the dark structures shaping galaxies today could be relics from a time before the Big Bang.”
This story originally appeared in WIRED en Español and has been translated from Spanish.
Tech
Europe’s Online Age Verification App Is Here

The European online age verification app is ready.
The app works with passports or ID cards, is built to be “completely anonymous” for the people who use it, works on any device (smartphones, tablets, and PCs), and is open source. “Best of all, online platforms can easily rely on our age verification app, so there are no more excuses,” said European Commission president Ursula von der Leyen at a press conference on Wednesday. “Europe offers a free and easy-to-use solution that can protect our children from harmful and illegal content.”
High Expectations
“It is our duty to protect our children in the online world just as we do in the offline world. And to do that effectively, we need a harmonized European approach,” von der Leyen said at Wednesday’s press conference. “And one of the central issues is the question, how can we ensure a technical solution for age verification that is valid throughout Europe? Today, I can announce that we have the answer.”
This answer takes the form of an open source app that any private company can repurpose, as long as it complies with European privacy standards and offers the same technical solution throughout the European Union. The user downloads the app, agrees to the terms and conditions, sets up a pin or biometric access, and proves their age through an electronic identification system, or by showing a passport or ID card (in which case biometric verification is also provided). The app does not store your name, date of birth, ID number, or any other personal information, according to the European Commission—only the fact that you are over a certain age.
After that, when a person using the app wants to access a social network (minimum age: 13), pornographic site (minimum age: 18), or any other age-protected content, if they are logged in from a computer, they need only scan the QR code shown on the site they want to visit. If, on the other hand, the person logs in from a smartphone, the app sends the proof of age directly. The platform does not access the document with which the user proved it in the first place.
Adoption Event
The need to introduce a common system for the entire European Union has been discussed for some time, and according to commission technicians, the technical work is now complete. Of course, it will still be possible to circumvent the system—all it takes is for an adult to lend their phone to a younger friend—but the technological architecture exists, and it will be up to EU member states to decide whether to integrate it into national digital wallets or develop independent apps.
“No More Excuses”
For the app to really be effective, platforms must be obligated to verify the age of their users—that’s where things get tricky. The Digital Services Act, which went into effect in 2024, requires “very large online platforms”—those with more than 45 million monthly users in the European Union—to take concrete steps to mitigate systemic risks related to child protection, with heavy penalties for noncompliance.
“And that’s why Europe has the DSA: to call online platforms to their responsibilities. Because Europe will not tolerate platforms making money at the expense of our children,” European Commission executive vice president Henna Virkkunen told a press conference. She added that after an investigation into TikTok, the European institutions plan to take similar action against Facebook, Instagram, and Snapchat, as well as four porn sites. “Since the platforms do not have adequate age verification tools, we developed the solution ourselves,” he concluded. In short, as von der Leyen also remarked, “there are no more excuses.”
Bare Minimum
So far, this is the European framework that sets the general rules. On this basis, member states can consider more restrictive measures. Italy was among the first to discuss how to regulate the use of social media by minors but has so far not landed on anything concrete. Elsewhere in the EU, France’s Emmanuel Macron has been a trailblazer on the issue, pushing France to discuss a rule to ban social networks for minors under the age of 15 entirely. So far, this measure has received broad political support—but the outcome depends largely on compatibility with the Digital Services Act and the availability of effective age verification systems like the app the European Commission just released.
This article originally appeared on WIRED Italia and has been translated.
-

 Tech1 week ago
Tech1 week agoAzure customers up in arms over ‘full’ UK South region | Computer Weekly
-

 Entertainment1 week ago
Entertainment1 week agoQueen Elizabeth II emotional message for Archie, Lilibet sparks speculation
-

 Tech1 week ago
Tech1 week agoAs the Strait of Hormuz Reopens, Global Shipping Will Take Months to Recover
-

 Fashion1 week ago
Fashion1 week agoCII submits 20-pt agenda to Indian govt to back firms hit by Iran war
-

 Tech1 week ago
Tech1 week agoThis AI Button Wearable From Ex-Apple Engineers Looks Like an iPod Shuffle
-

 Politics7 days ago
Politics7 days agoIndian airlines hit hardest after Dubai limits foreign flights until May 31
-

 Politics7 days ago
Politics7 days agoChinese, Taiwanese will unite, Xi tells Taiwan opposition leader
-

 Entertainment4 days ago
Entertainment4 days agoPalace left in shock as Prince William cancels grand ceremony






