Tech
Top AirDoctor Coupon Codes for January 2026

Thanks to the COVID pandemic and seemingly never ending wildfires, air purifiers have become an essential home appliance for overall health. Pretty much every building lets in a lot of particulate matter, volatile organic compounds, and vaporous chemicals. Not to mention off-gassing from indoor plastics, furniture, and paint. It’s important to ensure that the air you’re breathing is clean—from stopping coughs and allergy symptoms to helping us wake up with clearer sinuses and less raspy throats—air purifiers can make all the difference. AirDoctor makes a myriad of efficient air purifiers for every type of home, and we have AirDoctor promo codes and deals to help you save big on clean air.
Get $400 Off With AirDoctor Coupon
With something as serious as the health of your home, it’s important to act now and stay prepared. We know air purifiers can be pricey, and AirDoctor has made it more accessible for all. In preparation for the launch of their newest air purifying system, the AirDoctor 4000, you’ll get an extra $400 off when you pre-order (a total of $400 in savings instead of $800 under regular pricing). Their sleek design has advanced triple filtration and 360-degree air intake that traps 99.99% of particles, like allergens, smoke, mold, and bacteria.
Save 15% on AirDoctor Filter Combo Packs
We all know buying in bulk is the cheaper option almost always (See Costco, Sam’s Club, et. al), and purifying your home’s air is no different. AirDoctor has a deal right now, where you’ll save 15% when you purchase a filter combo pack (as opposed to individual filters). There’s no promo code required, either, so all you need to do is add it to your cart and you’re golden.
What Does an AirDoctor Purifier Do?
As mentioned at the top, air purifiers can help clean the air in your home, especially against some of those less-known (or noticed) toxins on top of everyday things like smoke, paint, and pet dander. We know the importance of clean air, and that’s why we’ve set up a handy guide on How to Buy an Air Purifier, including important, but often overlooked points, like how to fit your room to an air purifier and how to best pick out one that will best fit your home’s needs. We also have spent months testing air purifiers, and have rounded up the Best Air Purifiers for your home, including our picks for small or large rooms, and those with built-in fans or heaters.
We thought the AirDoctor Smart 5500i was the best purifier for PM 2.5 and gases because it captures fine particulates with its HEPA filters and gases with its dual action/carbon volatile organic compound trap filters, all while exchanging the air four times an hour in a 1,000-square-foot space. The purifier also has a handy alert to let you know when it is time to change the filter. There are tons of different AirDoctor options for various sized rooms, so make sure you read our guides and measure your home before purchasing to ensure you have the best AirDoctor air purifier for your space.
Best AirDoctor Air Purifier for Mold and Pets in 2025
As a cat parent living with someone who suffers from cat allergies, I know just how important an air purifier is to keep your home clean. One of the best air purifiers on the market is the AirDoctor 3500, which is great at tackling mold and pet dander. It’s ideal for medium to large rooms like your bedroom, living room, or kitchen. It’s great for rooms with a lot of odors, as it circulates 630 square feet four times per hour to give you continuous clean air, and it also has 3-stage filtration with UltraHEPA.
Tech
These Earbuds Drown Out Your Mouth-Breathing Roommates at $50 Off

Bose’s QuietComfort Ultra 2 earbuds are the best noise-canceling earbuds you can buy. Right now, they’re $50 off, which matches the best price we tend to see outside of special events like Black Friday and Cyber Monday. If you want to wait until November, they might hit $200 again, but otherwise $250 is a very fair deal—especially since they pop back up to $300 regularly. The discounted price applies to all five color options, including Black, Deep Plum, Desert Gold, Midnight Violet, and White Smoke (another rarity, as usually only the vivid colors go on sale).
Sometimes you just need to quiet the world. Whether it’s to play 10 hours of Coconut Mall on a loop to help you lock in and meet your Friday deadlines (thanks to my colleague Julia Forbes for that suggestion); muffle the crying babies, sniffling neighbors, and mysterious, potentially concerning clunking noises on an airplane; or to help you better appreciate the mix on Space Laces’ Vaultage 004 EP, active noise cancellation makes a huge difference to your listening experience.
The Bose QuietComfort Ultra 2 earbuds also have some of the best active noise cancellation you can find. They sound great out of the box, thanks to a custom sound profile based on the shape of your ears, but you can customize the EQ by using the app. The app also allows you to tweak touch controls and spatial audio.
The battery life lasts for about six hours, or 24 with the charging case. And while the noise cancellation can’t be beaten, these also have a pass-through feature called Aware mode, which filters in outside noise but smooths the loudest bits. That means you’ll be able to hear what’s going on, but you won’t be startled. True-crime podcast listeners, this one’s for you.
In fact, just about the only drawback we can find is that these might not be ideal for folks with super-small ears. Otherwise, they’re great all around, with solid call quality, excellent sound overall, and a sleek aesthetic. We think they offer good value at full price, so an extra $50 off is especially nice.
If you’re in the market for new headphones, but these don’t exactly fit what you’re looking for, we have plenty of other recommendations. Check out our guides to the Best Wireless Earbuds, Best Headphones for Working Out, Best Noise-Canceling Headphones, and Best Open Earbuds for additional hand-tested picks.
Tech
The Weird, Twisting Tale of How China Spied on Alysa Liu and Her Dad
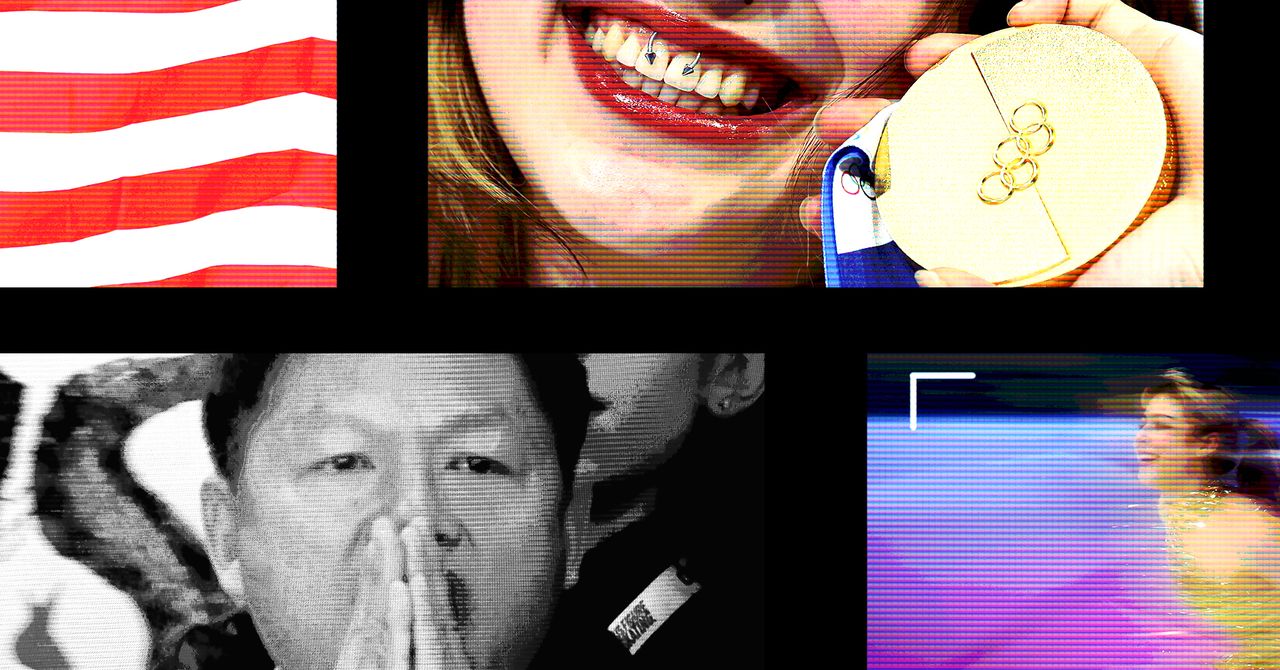
On November 16, 2021, Matthew Ziburis sat in his car in a residential neighborhood in the Bay Area stalking an “enemy,” as he put it. A veteran of both the US Army and Marine Corps, Ziburis had previously served in Iraq. But on this mission, he was working at the behest of China’s government. The targets that autumn day were American citizens: Arthur Liu and his teenage daughter, Alysa.
Arthur’s personal story was an exemplar of the American Dream. As a university student, he took part in the 1989 pro-democracy movement in China. After the crackdown at Tiananmen Square that year, he fled to the United States, settling in California. Arthur poured a small fortune and an equal amount of energy into molding Alysa into a figure skating phenom. As a national champion at age 13, she bantered along with Jimmy Fallon on The Tonight Show, and was at the time on track to represent America at the Winter Olympics the following year in Beijing.
Ziburis was surveilling the Liu home when he called Arthur, falsely claiming that he was a member of the US Olympic Committee who needed to discuss upcoming travel to Beijing, Arthur says. Ziburis was adamant that Arthur fax him copies of his and his daughter’s passports as part of a travel “preparedness check,” Liu tells WIRED. This struck Arthur as odd. In his many years dealing with sports bodies, he had never fielded such a request. Alysa’s agent did not respond to a request for comment.
Ziburis’ surveillance of Arthur and Alysa Liu that November day five years ago was just one episode in a bizarre saga that spanned from California to Beijing, touched New York City mayors and members of the US Congress, and has seen two people plead guilty and two more awaiting trial.
Unbeknownst to Ziburis, as he sat outside Aurthur and Alysa’s Northern California home, he too was being watched.
Ziburis had allegedly been dispatched to Northern California by Frank Liu, a self-styled fixer in the Chinese community from Long Island, New York, who was in turn receiving orders from a person in China named Qiang Sun. According to US authorities, Sun was working at the behest of the Chinese government. A concerned private investigator who once worked for Frank Liu had alerted the FBI to Frank’s escapades and was assisting authorities. Law enforcement was already on to Ziburis by the time he arrived. Anthony Ricco, Ziburis’ lawyer, did not respond to requests for comment.
Officers watched as Ziburis surveyed Arthur’s home and visited his law office. The heavy-set man sulking around Arthur’s office also caught the attention of a neighbor, who approached Ziburis and asked him if he needed help, Arthur says. Apparently concerned, the FBI called Arthur to warn him that Ziburis was heading to his home. By then, in part because of the harassment, Arthur and Alysa were boarding a plane to fly out of California. “It was like a movie,” Arthur says.
Alysa’s showing in Beijing in 2022 was disappointing. Burned out, she retired from the sport. Then in February, after returning to the ice after a two year hiatus, Alysa became the first US women’s figure skater to win Olympic gold since 2002—intentionally without her father by her side.
Despite her much-publicized complicated relationship with Arthur, Alysa’s success—punctuated by her signature pierced smile, racoon-tail dye job, and palpable joy for her sport—has reignited interest in the long-running case of transnational repression against her and her father. Human rights advocates and researchers have documented in recent years the lengths Beijing has taken to suppress critical voices, even those residing abroad or whose perceived transgressions date back decades.
Tech
There’s New Evidence for How Loneliness Affects Memory in Old Age

Neuroscientists know that there is a link between loneliness and cognitive decline in older adults, although it is still difficult to understand the exact magnitude of the link. A new longitudinal study provides evidence that a proportion of people who feel lonely end up having more memory impairment, though this doesn’t necessarily mean that their brains age faster.
The report, published in Aging & Mental Health, shows that older adults with higher levels of loneliness scored lower on tests of immediate and delayed recall. Even so, the rate at which their memory declined over six years was virtually identical to those who were not lonely.
“It suggests that loneliness may play a more prominent role in the initial state of memory than in its progressive decline,” said Luis Carlos Venegas-Sanabria of the School of Medicine and Health Sciences at Universidad del Rosario, who led the research. “The study underscores the importance of addressing loneliness as a significant factor in the context of cognitive performance in older adults.”
Six-Year Study of Thousands of Single People
The team analyzed data from the Survey of Health, Ageing and Retirement in Europe (SHARE), one of the most robust longitudinal databases for studying aging. For six years, the researchers followed 10,217 adults, aged 65 to 94, from 12 European countries. They assessed their level of loneliness and their performance on memory tests.
The results show that age was the most important determinant of memory level and speed of decline. From the age of 75 onwards, scores began to fall more rapidly. After 85 the decline became more pronounced. Depression and chronic diseases such as diabetes also reduced the initial score. Loneliness, while influencing the starting point, did not accelerate the slope of cognitive decline.
The study also found that physical activity was associated with better initial memory scores. People who engaged in moderate or vigorous physical activity at least once a month recalled more words on immediate and delayed recall tests. This effect did not change the speed of decline, but it did raise the baseline level, which functions as a kind of “cognitive buffer.”
Although the study does not explore the causes of the link between loneliness and cognition, previous research has proposed plausible mechanisms. Loneliness is often associated with less social interaction, a factor that influences cognitive performance. It is also associated with increased risk of depression, which does directly affect memory tests. In addition, lonely people tend to have more health problems, such as hypertension or diabetes, which also affect cognitive function.
By 2050, according to United Nations projections, one in six people in the world will be over the age of 65. Societies are entering a stage where old age will no longer be the exception but will become the norm. Dementia, as well as other neurodegenerative diseases that appear with age, will be a major challenge for health care institutions.
-

 Fashion4 days ago
Fashion4 days agoFrance’s LVMH Q1 revenue falls 6%, shows resilience amid Iran war
-

 Sports1 week ago
Sports1 week agoThe case for Man United’s Fernandes as Premier League’s best
-

 Entertainment1 week ago
Entertainment1 week agoPalace left in shock as Prince William cancels grand ceremony
-

 Business1 week ago
Business1 week agoUK could adopt EU single market rules under new legislation
-
 Entertainment5 days ago
Entertainment5 days agoIs Claude down? Here’s why users are seeing errors
-

 Sports1 week ago
Sports1 week agoLamar Jackson hits back at critics with faithful message on social media
-

 Fashion1 week ago
Fashion1 week agoEnergy emerges as biggest cost driver in textile margins
-

 Business1 week ago
Business1 week agoDelta Air Lines unveils first new Delta One suite in premium cabin arms race


















