Tech
Auditing, classifying and building a data sovereignty strategy | Computer Weekly

Data sovereignty is a hot topic. For commercial and public sector organisations, compliance to ensure personal data is secure is a primary objective. And that means it cannot be subject to foreign laws or interference.
Data sovereignty is also a matter for international relations, where states strive to ensure citizen and organisation data is secure from foreign interference. And, for states, achieving data sovereignty is also a way of protecting and developing national economies.
In this article, we look at data sovereignty, and the key steps CIOs need to take to build their data sovereignty strategy. This centres on auditing, classification and building controls over data location and movement.
What is data sovereignty, and why is it an issue?
At the most general level, data sovereignty is the retention of data within the jurisdiction – usually state boundaries – whose laws govern its use.
Interest in data sovereignty has been building for some time. In one sense, it looks a lot like law catching up with the “wild west” early years of cloud use and popularity. Here, organisations rushed to this new, highly flexible location to process and store data, then later discovered the risks to which they – and their customer data – had become exposed.
More recently, the drive to digital sovereignty stepped up to the level of states. That trend got a big boost during US president Donald Trump’s first term. That saw the country’s introduction of the Clarifying Lawful Overseas Use of Data (Cloud) Act, for example, which potentially allows US law enforcement to access data stored by US companies anywhere. Alarm bells started ringing, especially in Europe.
Organisations achieve digital sovereignty in their operations by making data subject to the laws and control of the state they operate in, or from. But we are far from achieving that, when, for example, Amazon Web Services (AWS), Microsoft Azure and Google Cloud Platform (GCP) have around 70% of the European cloud market, and many European state organisations are completely or overwhelmingly dependent on US hyperscalers for cloud services.
What are the concerns about data sovereignty, and what do CIOs plan to do?
Surveys regularly find IT decision-makers are concerned about data sovereignty. A Gartner survey conducted among 241 IT decision-makers globally found the majority (75%) of those outside the US plan to have a digital sovereignty strategy in place by 2030. Meanwhile, 53% said concerns over geopolitics would restrict future use of global cloud providers, and 61% said such worries would increase their use of regional or local cloud providers.
Complexity – and the potential for contradictory regulations and increased costs – is also a major concern, says Simon Robinson, principal analyst for storage and data infrastructure at Omdia.
“Our research found 74% of organisations say sovereign clouds have become more important over the last two years,” he says.
“However, it is a complex and fast-moving area. The regulatory and compliance environment is evolving rapidly. But the challenge for global organisations is that some regulations may actually conflict, potentially forcing them to contemplate whether they might break one law or regulation to satisfy another.”
Robinson adds: “At the very least it pushes up costs, may lead to inconsistent data policies around retention, and could slow down the adoption of advanced technologies, such as AI [artificial intelligence].”
So, while risks around stored data being in datacentres in a foreign country, on foreign infrastructure and subject to that country’s laws are a major worry, resolving that situation can bring its own issues too.
What is a data sovereignty audit, and why is it so important?
Core to an organisation’s responses to an unknown or uncontrolled data sovereignty situation is an audit of its data. This is the first step towards ensuring data is kept and processed within the appropriate state boundaries.
That will likely take the form of identification of the risks around different classes of data, according to Jon Collins, vice-president of engagement and field chief technology officer at GigaOm.
“Not all data is created equal, and not all parts of the architecture are created equal,” he says. “The first step is to classify what you’ve got. Identify whether it needs to fall within the scope of sovereignty, understand what kind of data it is, and consider how it might be impacted in terms of privacy, localisation and compliance.”
Key parts of a digital sovereignty strategy include mapping digital assets and data flows throughout their lifecycle and the laws to which they are subject at all stages. Then classify the data to assess risk levels for each class.
This can include geo-tagging, and should be part of an ongoing process, says Bettina Tratz-Ryan, vice-president and analyst at Gartner. “Automated discovery tools help identify and tag sensitive data, whether in physical storage or incidental locations like shared drives and folders,” she adds.
“Regular audits and compliance checks are non-negotiable and require strong governance policies and periodic manual reviews.”
How to minimise exposure to data storage risks
A data storage strategy that addresses data sovereignty builds on the classification of data in the data audit to limit what data can go where.
As part of the classification process, data will be subject to a policy that manifests in metadata tagging that indicates its sensitivity and tolerance for movement.
“Organisations should adopt a data governance as code approach, automating compliance through infrastructure as code techniques for consistent enforcement and rapid remediation,” says Tratz-Ryan.
That means sensitive data should be stored locally or in regional datacentres to meet residency requirements, with the cloud used for scalability under strict, region-specific compliance requirements.
“Continuous monitoring, encryption and geo-fencing are essential, and governance must be built in, not bolted on,” adds Tratz-Ryan.
Such approaches address the difficulties that potentially arise with data in transit. With the ability to monitor compliance and auditability built in via classification and tagging, critical workloads can be more easily segregated from less sensitive data at rest and in transit.
“Strict governance over location and movement is the cornerstone of risk mitigation,” says Tratz-Ryan.
Challenges in maintaining knowledge and control
There are many challenges to data sovereignty auditing. Data moves, and it moves across borders. We might believe we have nailed down data in our infrastructure, while data finds other backdoor routes across frontiers. Meanwhile, proprietary systems present huge challenges to audits and tagging, and staff create shadow IT, use emails, attach files, and so on.
In short, data movement in an organisation can be very complex indeed. It is potentially simple to audit and control the vast bulk of our data, but the problems come with incidental cases of data movement, says Tratz-Ryan.
“In globally connected organisations, sovereignty risks will occur even if data is stored in local servers. Remote access, backups, and software-as-a-service integrations can create cross-border exposure, triggering compliance challenges under laws like the US Cloud Act. Also, governance can be bypassed by incidental data movement via virtual private networks, personal devices, or email,” she says.
“And, for example, an automotive manufacturer may store design files on-premise in one location, but metadata and backups can flow through global product lifecycle management systems, creating sovereignty exposure.
“Incidental data movement, such as emails, shared drives and collaboration tools, often push data into unsanctioned cloud folders, outside sovereign governance. Shadow IT compounds the problem when employees use external apps without IT oversight, creating blind spots.”
GigaOm’s Collins believes that for most, the key elements needed to incorporate data sovereignty compliance are already present in their organisation.
“It’s practical to consider it within your broader governance, risk and compliance framework,” he says. “The advantage is, as a larger organisation, you already have practices, processes and people in place for audit, reporting and oversight. Sovereignty requirements can be incorporated into those mechanisms.”
Collins says we should not assume all data needs to meet sovereignty rules, and that in many cases, it’s not possible to do so.
“For example, it’s not realistic to make email a fully sovereign, locally contained application because it’s inherently distributed,” says Collins. “But you can prevent sovereign data from being transmitted by email. That’s where data loss prevention and data protection policies come in, to make sure data from certain repositories, or of certain classifications, is not emailed out.”
Similarly with cloud. Rather than try to make all cloud folders sovereign, we should instead decide what data can and cannot be stored there. And if data needs to be stored locally, then it goes to a local on-premise or domestic cloud service or availability zone.
“The core debate is deciding whether a particular dataset is sovereign,” says Collins. “If you operate in a given country and you hold customer data about people in that country, then that data stays in that country. That gives you a clear list of what cannot go into cloud folders, be sent by email, or managed by a system that can’t guarantee localisation. Once you frame it that way, the whole thing becomes much more straightforward.”
Tech
This M5 MacBook Air Discount Has Renewed My Faith in Cheap Laptops for 2026

In a time when almost everything is getting more expensive, this deal on the M5 MacBook Air has me hopeful about how laptop pricing will play out the rest of the year. The M5 MacBook Air has dropped back down to $949, which is $150 off its retail price. It’s only been at this price one other time since the product launched in early March and has more consistently sold for $1,049. As someone who’s reviewed every available MacBook and their strongest competitors, I can unequivocally say that this MacBook Air is one of the very best laptop deals right now.
Take the Surface Laptop 7th Edition, for example, which has been one of my favorite alternatives to the MacBook Air through all of 2025. It had been at competitive prices with the M4 MacBook Air all along, with both laptops sometimes dropping to as low as $799 during sales events like Prime Day throughout the year. But now, the Surface Laptop has gotten an official price hike due to the RAM shortage and is currently sitting at $1,200. It’s still a laptop I like quite a lot, but at $350 more than a similarly configured M5 MacBook Air, it’s very difficult to recommend.
Or consider the MacBook Neo, Apple’s new budget laptop that also launched in March. While it’s much cheaper overall, it’s only ever been sold for $10 off its full price. At this reduced price for the M5 MacBook Air of $949, that leaves only a dangerously small $260 gap between the Neo and the Air. It’s almost embarrassing how much better the Air is by comparison—in every way imaginable. If you’re curious how these two laptops stack up, I’ve done a comprehensive comparison between them that’s worth checking out. But to put it simply, despite all the excitement (and controversy) around the much cheaper MacBook Neo, the MacBook Air still has the most price flexibility in terms of deals.
Tech
A Brain Implant for Depression Is About to Be Tested in Humans
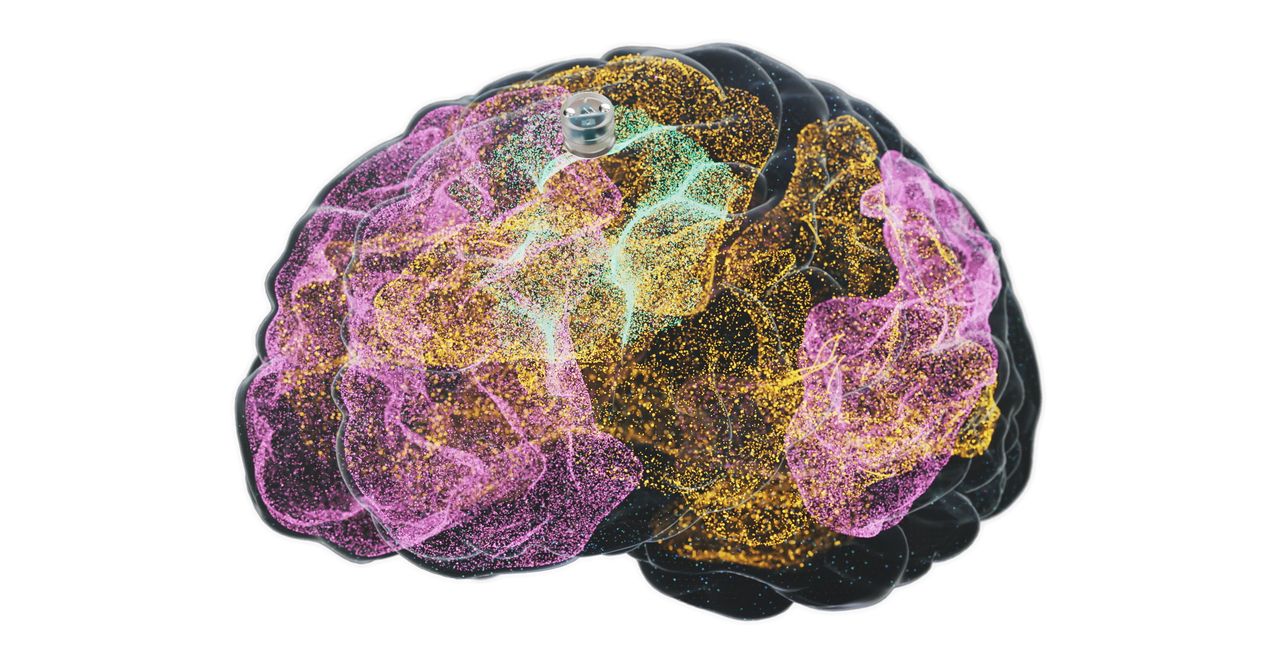
The latest brain-computer interface could help people recover from severe depression. Motif Neurotech announced Monday that the US Food and Drug Administration has approved a human study to trial the company’s blueberry-sized brain implant that sits in the skull and delivers electrical stimulation to treat depression.
The Houston-based startup, founded in 2022, is part of a budding industry pursuing technology to read and interpret brain signals. While other companies exploring similar technology, like Elon Musk’s Neuralink, Paradromics, and Synchron, are developing devices to enable paralyzed people to communicate and use computers, Motif is aiming to ease depression in people who have not benefited from medication.
The company’s device is implanted in the skull just above the dura, the brain’s protective membrane. It targets the central executive network, a part of the brain that is responsible for high-level cognitive functions and is underactive in major depressive disorder. The implant emits specific patterns of stimulation to turn “on” this network.
Motif’s device would allow patients to receive therapeutic brain stimulation at home. “Through frequent electrical stimulation, we think we can drive that neuroplasticity that creates stronger connectivity within the central executive network for patients with depression, so that they can get out of bed in the morning, call their friends, go to the gym,” says Jacob Robinson, Motif’s cofounder and CEO.
Courtesy of Motif
Electrical stimulation has been used for decades to treat depression, and Motif’s approach is just the latest iteration. Electroconvulsive or “shock” therapy began in the 1930s and is still used today in cases where patients don’t benefit from antidepressants. Deep brain stimulation, which involves surgically implanting electrodes into the brain, is occasionally used experimentally but is not FDA approved. A much milder form of stimulation known as transcranial magnetic stimulation, or TMS, was approved in 2008. While it can be highly effective, it typically requires a lengthy treatment regimen of five treatments a week for six weeks.
A study from 2021 found that during a 12-month period in the United States, nearly 9 million adults were undergoing treatment for major depressive disorder, and of those, almost 3 million were considered to have treatment-resistant depression, when symptoms do not improve after at least two, and often more, antidepressant medications.
Motif’s device can be implanted in a 20-minute outpatient procedure without the need for brain surgery. It’s powered by wireless magnetoelectric technology that Robinson developed while at Rice University and is charged with a baseball cap that patients will wear when receiving the stimulation.
Tech
The Man Behind AlphaGo Thinks AI Is Taking the Wrong Path

David Silver gave the world its very first glimpse of superintelligence.
In 2016, an AI program he developed at Google DeepMind, AlphaGo, taught itself to play the famously difficult game of Go with a kind of mastery that went far beyond mimicry.
Silver has since founded his own company, Ineffable Intelligence, that aims to build more general forms of AI superintelligence. The company will do this, Silver says, by focusing on reinforcement learning, which involves AI models learning new capabilities through trial and error. The vision is to create “superlearners” that go beyond human intelligence in many domains.
This approach stands in contrast to how most AI companies plan to build superintelligence, by exploiting the coding and research capabilities of large-language models.
Silver, speaking to WIRED from his office in London, says he thinks this approach will fail. As amazing as LLMs are, they learn from human intelligence—rather than building their own.
“Human data is like a kind of fossil fuel that has provided an amazing shortcut,” Silver says. “You can think of systems that learn for themselves as a renewable fuel—something that can just learn and learn and learn forever, without limit,” he says.
I’ve met Silver a few times and—despite this proclamation—he’s always struck me as one of the more humble people in AI. Sometimes, when talking about ideas he considers silly, he flashes a puckish grin. Right now, though, he’s deadly serious.
“I think of our mission as making first contact with superintelligence,” he says. “By superintelligence I really mean something incredible. It should discover new forms of science or technology or government or economics for itself.”
Five years ago, such a mission might have seemed ridiculous. But tech CEOs now routinely talk about machines outpacing human intelligence and replacing entire categories of workers. The idea that some new technical twist might unlock superhuman AI capabilities has recently spawned a raft of billion-dollar startups.
Ineffable Intelligence has so far raised $1.1 billion in seed funding at a valuation of $5.1 billion—an enormous sum by European AI standards. Silver has also recruited top AI researchers from Google DeepMind and other frontier labs to join his endeavor.
Silver says he will give all of the money he makes from equity in Effable Intelligence—a sum that could amount to billions if he is successful—away to charity.
“It’s a huge responsibility to build a company focusing on superintelligence,” he tells me. “I think this is something that has to be done for the benefit of humanity, and any money that I make from Ineffable will will go to high-impact charities that save as many lives as possible.”
Total Focus
Silver met Demis Hassabis, the CEO of Google DeepMind, at a chess tournament when they were kids, and the pair later became lifelong friends and collaborators.
They remained close after Silver left Google DeepMind, which he did only because he wanted to chart a completely new path. “I feel it’s really important that there is an elite AI lab that actually focuses a hundred percent on this approach,” he says. “That it’s not just a corner of another place dedicated to LLMs.”
The limits of the LLM-based approach can be seen, Silver says, with a simple thought experiment. Imagine going back in time and releasing a large language model in a world that believed the world was flat. Without being able to interact with the real world, the system, he says, would remain an avid flat-earther, even if it continued to improve its own code.
An AI system that can learn about the world for itself, however, could make its own scientific discoveries.
-

 Sports1 week ago
Sports1 week agoNCAA men’s gymnastics championship: All-time winners list
-

 Sports1 week ago
Sports1 week agoWWE WrestleMania 42 Night 2: Live match results and analysis
-

 Politics7 days ago
Politics7 days agoUK’s Starmer seeks to deflect blame over Mandelson appointment
-

 Fashion1 week ago
Fashion1 week agoUK’s Sosandar returns to profitability amid robust FY26 performance
-

 Entertainment1 week ago
Entertainment1 week agoLee Anderson, Zarah Sultana kicked out of UK Parliament for calling PM ‘liar’
-

 Business1 week ago
Business1 week agoNo fuel shortage: Govt assures 100% domestic LPG, PNG, CNG supply amid Hormuz energy crunch – The Times of India
-

 Business1 week ago
Business1 week agoHow Trump’s psychedelics executive order could unlock stalled cannabis reform
-

 Sports1 week ago
Sports1 week agoQuetta Gladiators opt to bowl after winning toss against Peshawar Zalmi in PSL 11 clash






