Tech
China Is Leading the World in the Clean Energy Transition. Here’s What That Looks Like
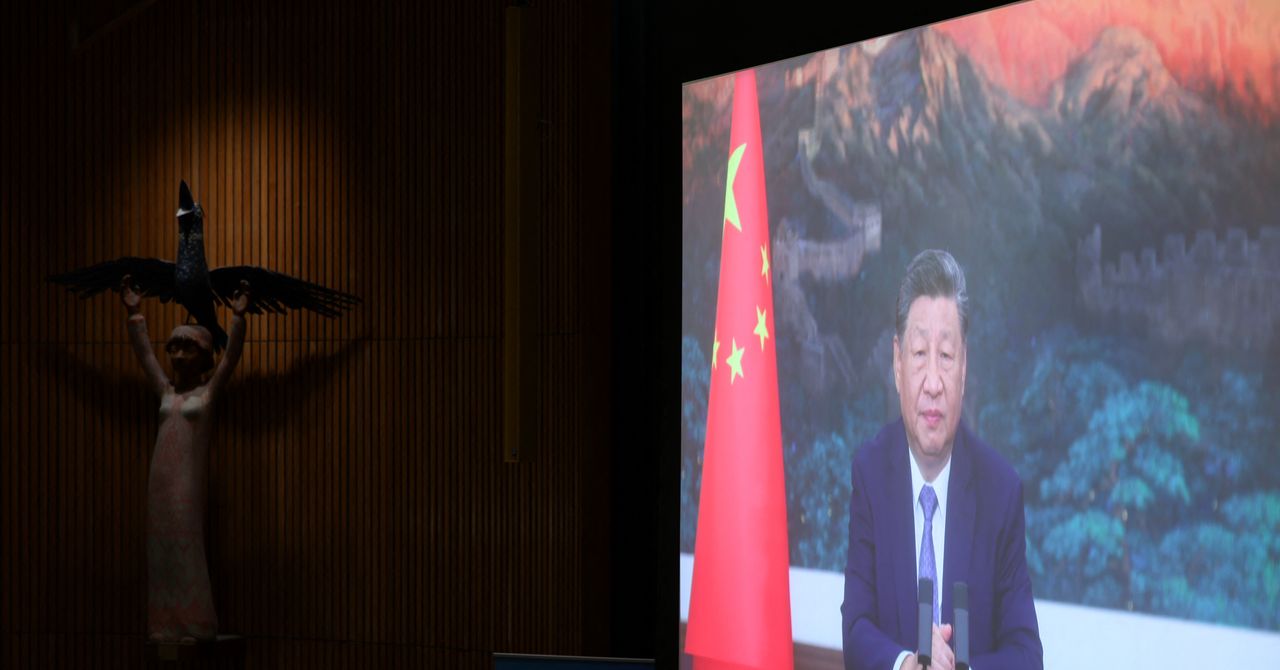
Speaking by video at the UN Climate Summit in New York last week, China’s president Xi Jinping laid out his country’s climate ambitions. While the stated goals may not have been aggressive as some environmentalists would like, Xi at least reaffirmed China’s green commitment.
“Despite some countries going against the trend, the international community should stay on the right track, maintain unwavering confidence, unwavering action, and undiminished efforts,” he said. Any reference to Donald Trump and the United States was surely intended (though not explicit).
The march of the energy transition is a long one, but it has to start somewhere. And with this approach, China has already taken quite a few steps.
Beijing Stands (Mostly) Alone
Today, there is no race to be a climate leader. The world is a far fry from the COP26 conference in November 2021, when tackling the threat of climate change seemed like a global priority. A few months later, Russia invaded Ukraine; the ensuing energy crisis and inflation kicked climate off of many political agendas.
While Joe Biden and the United States responded to soaring prices with the Inflation Reduction Act, which prioritized investment in renewable energy, Donald Trump subsequently withdrew the US from the Paris Agreement—an international accord to limit global warming—for the second time. The European Union has also stuttered: Too internally divided, it did not go beyond a drab declaration of intent at the UN Climate Summit. There hasn’t been much movement from India, a country of nearly 1.5 billion people. And other nations’ emissions are simply too small to matter.
Given this background, it becomes easy to understand how, in this scenario, China has become a global leader in the clean energy transition. Xi’s speech did not go into much detail, but it did mention all the main points of China’s strategy.
Cut Emissions Between 7 Percent and 10 Percent by 2035
In New York, Xi acknowledged the importance of the transition, and for the first time, agreed to reduce greenhouse gas emissions rather than simply promise to slow them down. China’s stated goal is between 7 percent and 10 percent reduction by 2035.
How do you evaluate these pledges? While the commitment is vague, it’s still significant; previously the regime had merely promised to reach peak emissions by 2030, tying the cuts to economic growth. In Xi’s speech you can seen China transition from a developing country approach to a role more akin to that of industrialized countries, whose emissions have been declining for decades.
Slow Going?
It should be pointed out that reducing emissions at the pace promised by Beijing means a decline of about 1 percent a year. According to an analysis by William Lamb of the Potsdam Institute for Climate Impact Research, this is a slower pace than that held by most industrialized nations. Italy, for example, has reduced them by an average of 3.2 percent every 12 months since their peak in 2006; the United Kingdom by an average of 2.8 percent since 2004; France by 2.3 percent.
“China has often promised little and achieved much,” notes Andreas Sieber, associate director for policy and campaigns for the global climate nonprofit 350.org, suggesting that China might overdeliver. The country’s lack of democracy also means its policies are not at risk of reversal every election cycle.
On Renewables
Xi Jinping’s speech included a commitment to reach 3,600 gigawatts (GW) of installed wind and solar capacity by 2035, six times the country’s 2020 figures. This is already the leading country in terms of installed renewable power, and a giant on the technology front as well, with universities churning out environmental and climate tech research at full speed, and attracting scientists from abroad across numerous fields. He also announced a commitment to an energy mix with more than 30 percent renewables.
On Electric Vehicles
Mobility has long been an issue for China, which has moved from bicycles, ubiquitous until the 1990s, to the mass automobile. The images of the 2008 Beijing Olympics are unforgettable: A blanket of smog buried the city. The government has in recent years given a strong boost to electric mobility: At the Climate Summit it announced plans to make EVs “mainstream,” that is, prevalent in sales. It helps that it has ready access to rare earth minerals that are essential for building batteries. And for that matter, the country hosts giant automotive companies like BYD and Catl, which supplies batteries to some 50 global brands including Tesla and Volkswagen.
On the carbon market
Xi has declared his intention to expand the national carbon emission trading market to more emission-intensive sectors than today.
On forests
China made additional commitments on forests, which it says will reach an extent of 34 billion cubic meters.
China has reshaped the market for green technologies.
To skeptics expecting broader measures and the mantle of true global leadership from China, well, that’s not a particularly coveted title these days—especially if the US continues to reverse course on climate science. As senior advisor Bernice Lee of the think tank Chatham House notes, China invested $625 billion in the clean energy transition last year alone; that’s nearly a third of the gobal total.
Not only that: Research and massive adoption of renewable technologies have led to the dramatic drop in prices, and China’s very large domestic market is a formidable driver in this regard. “The rise of Chinese renewables is reshaping the global economy and replacing coal in the domestic market,” Lee says.
The hope is that other countries, reassured by that commitment, will follow China’s example rather than America’s.
Tech
The ‘European’ Jolla Phone Is an Anti-Big-Tech Smartphone

“There are Chinese components as well—we are totally open about it—but the key is that as we compile the software ourselves and install it in Finland, we protect the integrity of the product,” Pienimäki says.
What makes Sailfish OS unique over competitors like GrapheneOS or e/OS is that it’s not based on the Android Open Source Project, but Linux. That means it has no ties to Google—no need for the company to “deGoogle” the software; meaning there’s a greater sense of sovereignty over the software (and now the hardware). Still, it’s able to run Android apps, though the implementation isn’t perfect. Another common criticism is that it’s not as secure as options like GrapheneOS, where every app is sandboxed.
There’s a good chance some Android apps on Sailfish OS will run into issues, which is why in the startup wizard, the phone will ask if you want to install services like MicroG—open source software that can run Google services on devices that don’t have the Google Play Store, making it an easier on-ramp for folks coming from traditional smartphones without a technical background. You don’t even need to create a Sailfish OS account to use the Jolla Phone.
Jolla’s effort is hardly the first to push the anti-Big Tech narrative. A wave of other hardware and software companies offer a “deGoogled” experience, whether that’s Murena from France and its e/OS privacy-friendly operating system, or the Canadian GrapheneOS, which just announced a partnership with Motorola. At CES earlier this year, the Swiss company Punkt also teamed up with ApostrophyOS to deploy its software on the new MC03 smartphone. Jolla is following a broader European trend of reducing reliance on US companies, like how French officials ditched Zoom for French-made video conference software earlier this year.
The Phone
A common problem with these niche smartphones is that they inevitably end up costing a lot of money for the specs. Take the Light Phone III, for example, a fairly low-tech anti-smartphone that doesn’t enjoy the benefits of economies of scale, resulting in an outlandish $699 price. The Jolla Phone is in a similar boat, though the specs-to-value ratio is a little more respectable.
It’s powered by a midrange MediaTek Dimensity 7100 5G chip with 8 GB of RAM, 256 GB of storage, plus a microSD card slot and dual-SIM tray. There’s a 6.36-inch 1080p AMOLED screen, the two main cameras, and a 32-megapixel selfie shooter. The 5,500-mAh battery cell is fairly large considering the phone’s size, though the phone’s connectivity is a little dated, stuck with Wi-Fi 6 and Bluetooth 5.4.
Uniquely, the Jolla Phone brings back “The Other Half” functional rear covers from the original. These swappable back covers have pogo pins that interface with the phone, allowing people to create unique accessories like a second display on the back of the phone or even a keyboard attachment. There’s an Innovation Program where the community can cocreate functional covers together and 3D print them. And yes, a removable rear cover means the Jolla Phone’s battery is user-replaceable.
Tech
Attacks on GPS Spike Amid US and Israeli War on Iran

Shipping through the Strait of Hormuz—the narrow but vital oil trade route in the Middle East—has almost ground to a halt since the start of the United States and Israel’s war against Iran. Tankers in the region have faced military strikes and a spike in GPS jamming attacks, a new analysis says.
Since the first US-Israeli strikes against Iran on February 28, more than 1,100 ships operating across the Gulf region have had their GPS or automatic identification system (AIS) communications technology disrupted, says Ami Daniel, the CEO of maritime intelligence firm Windward. Ships have been made to appear as if they were inland on maps, including at a nuclear power plant, the firm says.
The analysis comes as maritime officials have warned of a “critical” risk to ships operating in the region and as the initial conflict has quickly expanded to involve countries across the Middle East. At least three tankers in the region have been damaged in the conflict.
“We’re seeing a lot of GPS jamming,” Daniel says of shipping in the Strait of Hormuz and surrounding areas. The levels of electronic interference are “way above the baseline” of usual interference, he says. “It’s becoming very dangerous to go in and out.”
Over the last few years, attacks against GPS and navigation systems have been on the rise—largely driven by the wars in Ukraine and Gaza. They can impact people’s phones or devices, but also disrupt the safety and navigation systems in planes and ships. The electronic interference largely comes in two forms: jamming and spoofing. During jamming attacks, satellite signals are overwhelmed so that positioning data isn’t available. Whereas spoofing can create false signals that make an object appear incorrectly on a map—for instance, making ships appear as if they are inland at airports.
Inaccurate location data can lead to ships running off course, potentially increasing the chances of them crashing into other tankers, running aground, or causing damaging oil spills. In warzones, electronic interference is often used to try and disrupt the navigation systems of drones or missiles, which can rely on location data to find and hit their targets.
Analysis of shipping data by Windward found that there has been an “escalating” level of electronic interference across Iranian, United Arab Emirates, Qatari, and Omani waters since the initial strikes on February 28. Daniel says that the majority of the activity the company has identified so far has been jamming rather than spoofing. The company’s analysis says it has identified around 21 “new clusters” where ships have had their AIS data jammed in recent days.
“Ships were falsely positioned at airports, a nuclear power plant, and on Iranian land, creating navigation and compliance risks,” a report from the firm says. “AIS signals have also been diverted to the Barakah Nuclear Power Plant and nearby waters, while hundreds of other vessels are creating circle-like patterns off UAE, Qatari, and Omani waters.”
GPS and AIS interference within the Strait of Hormuz and the surrounding area is not new. In June 2025, as Israel and Iran exchanged missile fire, significant jamming in the region was reported.
While almost all commercial air travel has been grounded around the Middle East, there have been signs of electronic interference on aircraft flying ahead of and around the strikes. “There are at least six new spoofing signatures in the Middle East,” says Jeremy Bennington, vice president of positioning, navigation, and timing strategy and innovation at technology firm Spirent Communications. “Hundreds of flights have been impacted. However, that decreased significantly over the weekend as flights have been canceled.”
Tech
NCSC: No increase in cyber threat from Iran, but be prepared | Computer Weekly

In the wake of a major series of new US and Israel-led attacks on Iran and subsequent retaliatory strikes on Gulf states including Bahrain, Kuwait and the UAE, the UK’s National Cyber Security Centre (NCSC) has reassured British organisations that there is likely no significant change in the direct cyber threat posed by Iranian actors.
But that despite the attacks, Iranian state threat actors likely retain some ability to conduct cyber attacks, and more widely, there is a risk of collateral impacts – such as distributed denial of service (DDoS) attacks – originating from hacktivist groups sympathetic to Iran.
And, as the spreading conflict threatens to draw in the UK, the GCHQ-backed cyber agency said it this assessment was subject to change at short notice, and there was almost certainly a heightened risk of indirect cyber threat for any UK organisations with a presence in the Middle East.
“In light of rapidly evolving events in the Middle East, it is critical that all UK organisations remain alert to the potential risk of cyber compromise, particularly those with assets or supply chains that are in areas of regional tensions,” said NCSC director for national resilience, Jonathon Ellison.
“Today, the National Cyber Security Centre has published an alert outlining the current cyber threat to the UK and the practical steps organisations should take in response.
“This includes engaging with our guidance to reduce the likelihood of falling victim to an attack where the cyber risk is heightened, and how critical national infrastructure organisations can prepare for and respond to severe cyber threats.
“Organisations are strongly encouraged to act now, following the recommended actions to prioritise and strengthen their cyber security posture,” said Ellison.
Global conflict
Although no European states have taken part in the initial strikes, Dennis Calderone, principal and chief technology officer (CTO) at Suzu Labs, said that European organisations still needed to pay attention.
“Iran’s cyber operations don’t stop at US borders, and the proxy groups operating on Iran’s behalf are even less predictable in their targeting,” said Calderone. “When the motivation is retaliation and the conventional military is gone, cyber operators cast a wide net.
“Since it appears that conventional military options are looking increasingly to be off the table, cyber is what Iran has left,” he added.
“And even with their own internet down, pre-positioned implants and operators based outside Iran can still execute. If you’re in energy, water, financial services, or defense, assume you’re a target. Start hunting for anomalous access in your environment now. Don’t wait for something to break.”
James Turgal, vice president of global cyber risk and board relations at Optiv, said that over the next 30 days or so, there will likely be a surge of cyber activity linked to Iran, including website defacements, DDoS attacks, doxxing and leaks, and disruptive intrusions designed to create symbolic impact and public fear. This will likely include influence operations.
Threat actors will likely opportunistically exploit vulnerabilities in unpatched, internet-facing systems, and take advantage of other cyber weaknesses, such as exposed VPNs, and badly-secured operational technology (OT) or industrial control systems (ICS).
Within 72 hours, at-risk organisations should move to lock down internet-facing exposures, verify they are patched and up-to-date, have removed or limited unnecessary remote admin surfaces, rotated any exposed credentials, and validated multifactor authentication on any remote devices, said Turgal. CNI operators should also review their OT and ICS segmentation and monitoring.
More widely, security leaders should take steps to protect user identities against potential intrusion, and ensure their infrastructure is hardened against DDoS attacks.
Blended threat
Halcyon’s Cynthia Kaiser – who was previously deputy assistant director of the FBI’s cyber division, said she was already seeing increased activity in the Middle East, and calls to action from hacktivists, DDoS botnet operators, and ransomware gangs.
“Iran has a long track record of using cyber operations to retaliate against perceived political slights…. Tehran’s cyber playbook has been aggressive and evolving,” she said.
“Increasingly, ransomware is incorporated into these escalating operations. Last year, an Iranian national pleaded guilty to ransomware attacks that crippled Baltimore and other US municipalities, causing tens of millions in damages. Since at least 2017, Iranian operators have targeted US critical infrastructure … with ransomware campaigns that blur the line between criminal extortion and state-sponsored sabotage.”
In practice, Kaiser explained, Iranian cyber ops blend state sponsorship, personal profiteering, and outright criminal behaviour. For example, she said, financially-motivated hackers may attempt to monetise access gained through government-funded campaigns.
Like Moscow, she added, Tehran turns a blind – or at least indifferent – eye to criminal cyber ops against shared enemies such as the US, Israel and their regional allies.
“Having access to cyber criminals gives the government options. As Iran considers its response to US and Israeli military actions, it is likely to activate any of these cyber actors if it believes their operations can deliver a meaningful retaliatory impact,” said Kaiser.
-

 Business6 days ago
Business6 days agoHouseholds set for lower energy bills amid price cap shake-up
-

 Politics5 days ago
Politics5 days agoWhat are Iran’s ballistic missile capabilities?
-

 Entertainment1 week ago
Entertainment1 week agoTalking minerals and megawatts
-

 Sports1 week ago
Sports1 week agoEileen Gu comments on Alysa Liu’s historic gold medal
-

 Business6 days ago
Business6 days agoLucid widely misses earnings expectations, forecasts continued EV growth in 2026
-

 Sports5 days ago
Sports5 days agoSri Lanka’s Shanaka says constant criticism has affected players’ mental health
-

 Tech6 days ago
Tech6 days agoHere’s What a Google Subpoena Response Looks Like, Courtesy of the Epstein Files
-

 Business6 days ago
Business6 days agoIncome Tax Draft Rules 2026: Key Changes On How And When Pan Card Will Be Required?
















