Tech
Microsoft patches 112 CVEs on first Patch Tuesday of 2026 | Computer Weekly
Microsoft has pushed fixes for 112 common vulnerabilities and exposures (CVEs) on the first Patch Tuesday of 2026, among them a number of zero-day flaws that were either publicly disclosed or actively exploited prior to patching, and no fewer than eight critical bugs.
Although this is a sharp increase in comparison to recent Patch Tuesdays – December 2025 saw Microsoft patch just 56 flaws – it is important to note that the festive season is frequently a quieter time for patches, sometimes by design, and January often brings an uptick in disclosures. Nevertheless, observed Jack Bicer, director of vulnerability research at patch management firm Action1, the volume of fixes in the latest update underscores “growing pressure” on security teams.
“This comes against a broader trend: in 2025, reported vulnerabilities increased by 12% over 2024, continuing the upward trajectory of disclosed security flaws,” said Bicer.
Paramount among these flaws is CVE-2026-20805, an information disclosure vulnerability in Desktop Window Manager, discovered by Microsoft’s own Threat Intelligence and Security Response Centers.
Although it bears a relatively low Common Vulnerability Scoring System (CVSS) score of just 5.5, active exploitation of CVE-2026-20805 has been observed in the wild, Microsoft said
“The flaw leaks a memory address from a remote ALPC [Asynchronous Local Procedure Call] port. This type of information disclosure vulnerability is often used to defeat Address Space Layout Randomisation (ASLR) – a security feature in modern operating systems designed to protect against buffer overflows and other exploits that rely on manipulating the memory of a running application,” explained Immersive senior director of cyber threat research, Kev Breen.
“Once they know where code resides in memory, they can chain this with a separate code execution bug to turn a difficult exploit into a reliable one,” he said. “Microsoft doesn’t provide any information on what other components that chain could involve – making it harder for defenders to threat hunt for potential exploitation attempts, meaning patching quickly is the only mitigation for now.”
Ivanti vice president of security product management, Chris Goettl, agreed with this assessment. “The vulnerability affects all currently supported and extended security update supported versions of the Windows OS,” he said, “[so] a risk-based prioritisation methodology warrants treating this vulnerability as a higher severity than the vendor rating or CVSS score assigned.”
Next up is a security feature bypass (SFB) flaw in Secure Boot Certificate Expiration, tracked as CVE-2026-21265. It, too, carries a comparatively low CVSS score and Microsoft only rates it as Important. However, said Goettl, it has been publicly disclosed and security teams would be wise to look into it.
“The fix provides a warning regarding certificates that will be expiring in 2026 and details on actions that are required to up renew certificates prior to their expiration in addition to the update,” he said.
“It is recommended to start investigating what actions your organisation may need to take to prevent potential serviceability and security as certificates expire.”
The remaining items on the zero-day list – again both publicly disclosed but not known to be exploited, date back three and four years respectively. Both are elevation of privilege (EoP) flaws affecting soft modem drivers that ship natively with supported Windows operating systems.
The older of the two, CVE-2023-31096, is to be found in Agere Soft Modem Driver, and the more recent one, CVE-2024-55414 in Windows Motorola Soft Modem Driver. Microsoft’s solution is to remove the affected drivers, agrsm64.sys and arsm.sys in the first instances and smserl64.sys and smserial.sys in the second, as part of the January cumulative update.
This means soft modem hardware that depends on them will now cease to work on Windows. Microsoft said admins should act quickly to remove any existing dependencies on the affected hardware.
Critical flaws
The critically-rated flaws in the January 2026 Patch Tuesday drop comprise six remote code execution (RCE) issues and two EoP issues.
The RCE flaws affect Microsoft Excel, Microsoft Office and Windows Local Security Authority Subsystem Service (LSASS). They have been assigned designations CVE-2026-20854, CVE-2026-20944, CVE-2026-20952, CVE-2026-20953, CVE-2026-20955 and CVE-2026-20957.
The EoP flaws are CVE-2026-20822, which impacts the Windows Graphics Component, and CVE-2026-20876, which impacts Windows Virtualization-Based Security (VBS) Enclave.
Mike Walters, president and co-founder at Action1, said the VBS flaw was worth particular attention because “it breaks the security boundary designed to protect Windows itself, allowing attackers to climb into the one of the most trusted execution layers of the system”.
Walters warned of a serious risk to organisations that lean on VBS in order to protect credentials and other secrets, or sensitive workloads, because if exploited successfully, an attacker might be able to bypass security controls, achieve persistence, evade detection, and hit systems that security teams believe to be strongly isolated.
“Although exploitation requires high privileges, the impact is severe because it compromises virtualisation-based security itself. Attackers who already have a foothold could use this flaw to defeat advanced defenses, making prompt patching essential to maintain trust in Windows security boundaries,” he said.
“If the patch cannot be applied immediately, restrict administrative access, enforce strong privilege management, and monitor for abnormal activity involving VBS or enclave-related processes.”
Tech
There’s New Evidence for How Loneliness Affects Memory in Old Age

Neuroscientists know that there is a link between loneliness and cognitive decline in older adults, although it is still difficult to understand the exact magnitude of the link. A new longitudinal study provides evidence that a proportion of people who feel lonely end up having more memory impairment, though this doesn’t necessarily mean that their brains age faster.
The report, published in Aging & Mental Health, shows that older adults with higher levels of loneliness scored lower on tests of immediate and delayed recall. Even so, the rate at which their memory declined over six years was virtually identical to those who were not lonely.
“It suggests that loneliness may play a more prominent role in the initial state of memory than in its progressive decline,” said Luis Carlos Venegas-Sanabria of the School of Medicine and Health Sciences at Universidad del Rosario, who led the research. “The study underscores the importance of addressing loneliness as a significant factor in the context of cognitive performance in older adults.”
Six-Year Study of Thousands of Single People
The team analyzed data from the Survey of Health, Ageing and Retirement in Europe (SHARE), one of the most robust longitudinal databases for studying aging. For six years, the researchers followed 10,217 adults, aged 65 to 94, from 12 European countries. They assessed their level of loneliness and their performance on memory tests.
The results show that age was the most important determinant of memory level and speed of decline. From the age of 75 onwards, scores began to fall more rapidly. After 85 the decline became more pronounced. Depression and chronic diseases such as diabetes also reduced the initial score. Loneliness, while influencing the starting point, did not accelerate the slope of cognitive decline.
The study also found that physical activity was associated with better initial memory scores. People who engaged in moderate or vigorous physical activity at least once a month recalled more words on immediate and delayed recall tests. This effect did not change the speed of decline, but it did raise the baseline level, which functions as a kind of “cognitive buffer.”
Although the study does not explore the causes of the link between loneliness and cognition, previous research has proposed plausible mechanisms. Loneliness is often associated with less social interaction, a factor that influences cognitive performance. It is also associated with increased risk of depression, which does directly affect memory tests. In addition, lonely people tend to have more health problems, such as hypertension or diabetes, which also affect cognitive function.
By 2050, according to United Nations projections, one in six people in the world will be over the age of 65. Societies are entering a stage where old age will no longer be the exception but will become the norm. Dementia, as well as other neurodegenerative diseases that appear with age, will be a major challenge for health care institutions.
Tech
Managing traffic in space
Chances are, you’ve already used a satellite today. Satellites make it possible for us to stream our favorite shows, call and text a friend, check weather and navigation apps, and make an online purchase. Satellites also monitor the Earth’s climate, the extent of agricultural crops, wildlife habitats, and impacts from natural disasters.
As we’ve found more uses for them, satellites have exploded in number. Today, there are more than 10,000 satellites operating in low-Earth orbit. Another 5,000 decommissioned satellites drift through this region, along with over 100 million pieces of debris comprising everything from spent rocket stages to flecks of spacecraft paint.
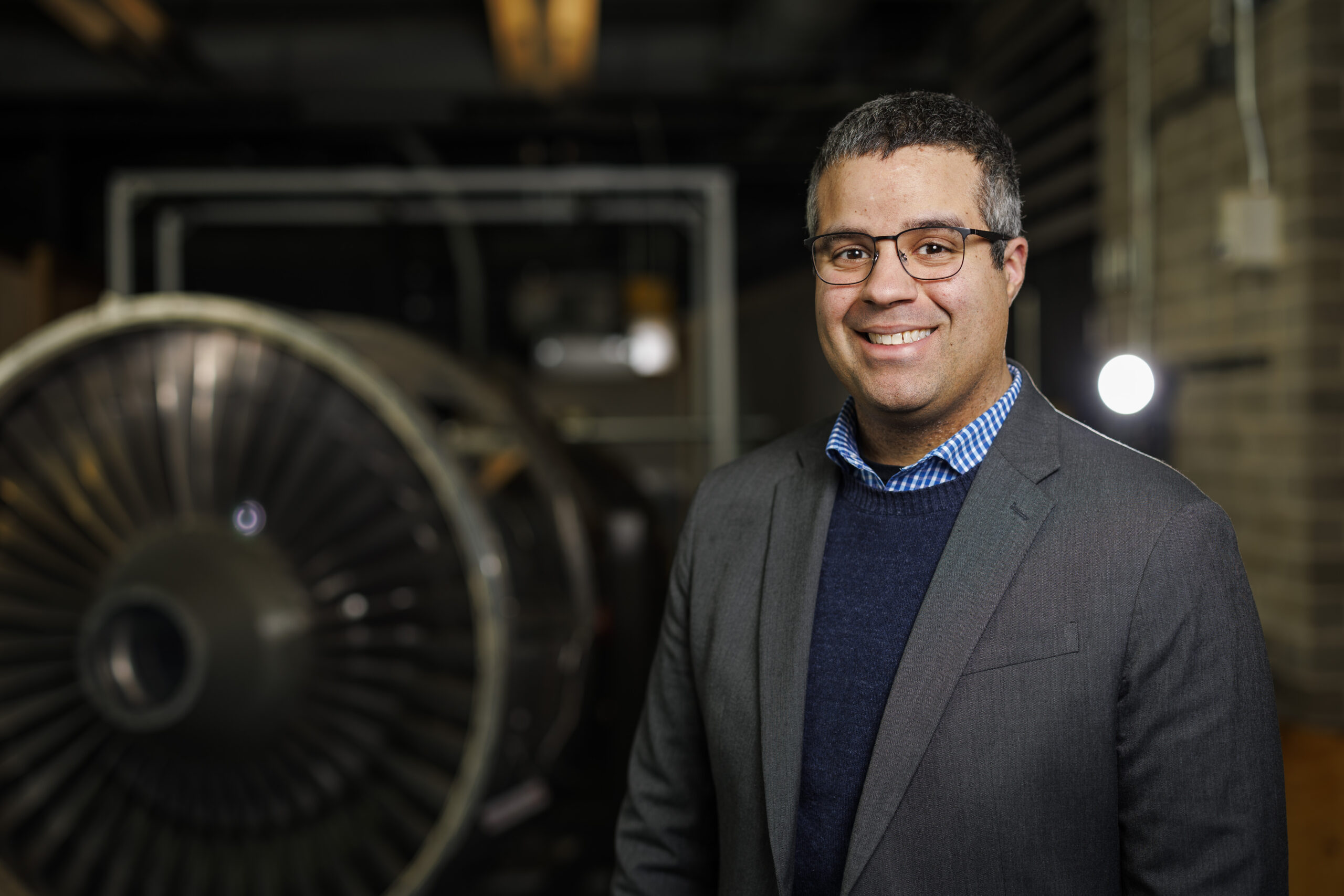
For MIT’s Richard Linares, the rapid ballooning of satellites raises pressing questions: How can we safely manage traffic and growing congestion in space? And at what point will we reach orbital capacity, where adding more satellites is not sustainable, and may in fact compromise spacecraft and the services that we rely on?
“It is a judgement that society has to make, of what value do we derive from launching more satellites,” says Linares, who recently received tenure as an associate professor in MIT’s Department of Aeronautics and Astronautics (AeroAstro). “One of the things we try to do is approach these questions of traffic management and orbital capacity as engineering problems.”
Linares leads the MIT Astrodynamics, Space Robotics, and Controls Lab (ARCLab), a research group that applies astrodynamics (the motion and trajectory of orbiting objects) to help track and manage the millions of objects in orbit around the Earth. The group also develops tools to predict how space traffic and debris will change as operators launch large satellite “mega-constellations” into space.
He is also exploring the effects of space weather on satellites, as well as how climate change on Earth may limit the number of satellites that can safely orbit in space. And, anticipating that satellites will have to be smarter and faster to navigate a more cluttered environment, Linares is looking into artificial intelligence to help satellites autonomously learn and reason to adapt to changing conditions and fix issues onboard.
“Our research is pretty diverse,” Linares says. “But overall, we want to enable all these economic opportunities that satellites give us. And we are figuring out engineering solutions to make that possible.”
Grounding practical problems
Linares was born and raised in Yonkers, New York. His parents both worked as school bus drivers to support their children, Linares being the youngest of six. He was an active kid and loved sports, playing football throughout high school.
“Sports was a way to stay focused and organized, and to develop a work ethic,” Linares says. “It taught me to work hard.”
When applying for colleges, rather than aim for Division I schools like some of his teammates, Linares looked for programs that were strong in science, specifically in aerospace. Growing up, he was fascinated with Carl Sagan’s “Cosmos” docuseries. And being close to Manhattan, he took regular trips to the Hayden Planetarium to take in the center’s immersive projections of space and the technologies used to explore it.
“My interest in science came from the universe and trying to understand our place within it,” Linares recalls.
Choosing to stay close to home, he applied to in-state schools with strong aeronautical engineering departments, and happily landed at the State University of New York at Buffalo (SUNY Buffalo), where he would ultimately earn his bachelor’s, master’s, and doctoral degrees, all in aerospace engineering.
As an undergraduate, Linares took on a research project in astrodynamics, looking to solve the problem of how to determine the relative orientation of satellites flying in formation.
“Formation flying was a big topic in the early 2000s,” Linares says. “I liked the flavor of the math involved, which allowed me to go a layer deeper toward a solution.”
He worked out the math to show that when three satellites fly together, they essentially form a triangle, the angles of which can be calculated to determine where each satellite is in relation to the other two at any moment in time. His work introduced a new controls approach to enable satellites to fly safely together. The research had direct applications for the U.S. Air Force, which helped to sponsor the work.
As he expanded the research into a master’s thesis, Linares also took opportunities to work directly with the Air Force on issues of satellite tracking and orientation. He served two internships with the U.S. Air Force Research Lab, one at Kirtland Air Force Base in Albuquerque, New Mexico, and the other in Maui, Hawaii.
“Being able to collaborate with the Air Force back then kind of grounded the research in practical problems,” Linares says.
For his PhD, he turned to another practical problem of “uncorrelated tracks.” At the time, the Air Force operated a network of telescopes to observe more than 20,000 objects in space, which they were working to label and record in a catalog to help them track the objects over time. But while detecting objects was relatively straightforward, the challenge came in correlating a detected object with what was already in the catalog. In other words, is what they were seeing something they had already seen?
Linares developed image analysis techniques to identify key characteristics of objects such as their shape and orientation, which helped the Air Force “fingerprint” satellites and pieces of space debris, and track their activity — and potential for collisions — over time.
After completing his PhD, Linares worked as a postdoc at Los Alamos National Laboratory and the U.S. Naval Observatory. During that time he expanded his aerospace work to other areas including space weather, using satellite measurements to model how Earth’s ionosphere — the upper layer of the atmosphere that is ionized by the sun’s radiation — affects satellite drag.
He then accepted a position as assistant professor of aerospace engineering at the University of Minnesota at Minneapolis. For the next three years, he continued his research in modeling space weather, tracking space objects and coordinating satellites to fly in swarms.
Making space
In 2018, Linares made the move to MIT.
“I had a lot of respect for the people and for the history of the work that was done here,” says Linares, who was especially inspired by the legendary Charles Stark “Doc” Draper, who developed the first inertial guidance systems in the 1940s that would enable the self-navigation of airplanes, submarines, satellites, and spacecraft for decades to come. “This was essentially my field, and I knew MIT was the best place to continue my career.”
As a junior faculty member in AeroAstro, Linares spent his first years focused on an emerging challenge: space sustainability. Around that time, the first satellite constellations were launching into low-Earth orbit with SpaceX’s Starlink, which aimed to provide global internet coverage via a huge network of several thousand coordinating satellites. The launching of so many satellites, into orbits that already held other active and nonactive satellites, along with millions of pieces of space debris, raised questions about how to safely manage the satellite traffic and how much traffic an orbit can sustain.
“At what level do we reach a tipping point, where we have too many satellites in certain orbital regimes?” Linares says. “It was kind of a known problem at the time, but there weren’t many solutions.”
Linares’ group applied an understanding of astrodynamics, and the physics of how objects move in space, to figure out the best way to pack satellites in orbital “shells,” or lanes that would most likely prevent collisions. They also developed a state-of-the-art model of orbital traffic, that was able to simulate the trajectories of more than 10 million individual objects in space. Previous models were much more limited in the number of objects they could accurately simulate. Linares’ open-source model, called the MIT Orbital Capacity Assessment Tool, or MoCAT, could account for the millions of pieces of space debris, in addition to the many intact satellites in orbit.
The tools that his group has developed are used today by satellite operators to plan and predict safe spacecraft trajectories. His team is continuing to work on problems of space traffic management and orbital capacity. They are also branching out into space robotics. The team is testing ways to teleoperate a humanoid robot, which could potentially help to build future infrastructure and carry out long-duration tasks in space.
Linares is also exploring artificial intelligence, including ways that a satellite can autonomously “learn” from its experience and safely adapt to uncertain environments.
“Imagine if each satellite had a virtual Doc Draper onboard that could do the de-bugging that we did from the ground during the Apollo missions,” Linares says. “That way, satellites would become instantaneously more robust. And it’s not taking the human out of the equation. It’s allowing the human to be amplified. I think that’s within reach.”
Tech
Meta Glasses Are Comfortable, Functional, and Make My Spouse Recoil in Fear

Every time I’ve written about Meta’s AI-enabled glasses, I invariably get asked these questions: Why do you even want these? Why do you want smart glasses that can play music or misidentify native flora in a weirdly cheery voice? I am a lifelong Ray-Ban Wayfarer wearer, and I’m also WIRED’s resident Meta wearer. I grab a pair of Meta glasses whenever I leave the house because I like being able to use one device instead of two or three on a walk. With Meta glasses, I can wear sunglasses and workout headphones in one!
Meta sold more than 7 million pairs in 2025. Take a look at any major outdoor or sporting event, and you’ll see more than a few people wearing these to record snippets for Instagram or TikTok. Meta’s partnership with EssilorLuxottica has made smart glasses accessible, stylish, and useful and is undoubtedly the reason why Google, and now Apple, are trying to horn in on the market. After the notable flop that is the Apple Vision Pro, Apple is recalibrating its face-wearable strategy, moving away from augmented reality (AR) toward simpler, display-less, and hopefully good-looking glasses.
That’s not to say that you shouldn’t be careful how you use these glasses. Meta doesn’t have the greatest track record on privacy, and the company has continued to push forward with policies that are questionable at best. Even if you’re not concerned that face recognition will allow Meta to target immigrants or enable stalkers to find their victims, at the very least, people really do not like the idea that you could start recording them at any moment.
Probably the biggest hurdle to wearing Meta glasses is that even doing so seems like a gross violation of the social contract. After all, these are Mark Zuckerberg’s “pervert glasses.” When I pop these on my head, I’ve had friends (and my spouse) recoil and say, “I have apps to warn me away from people like you.” The best part, though, is that Oakley and Ray-Ban already make really great sunglasses. Even if the battery runs out or you don’t use Meta AI at all, these are stellar at shading your eyes from the sun.
Anyway, if you decide to try them, here’s what you should get. If you do chicken out, check out our buying guides to the Best Smart Glasses or the Best Workout Headphones for more.
Table of Contents
Best Overall
Last year, Meta upgraded the original Meta Ray-Ban Wayfarers that became a smash hit. These are Meta’s entry-level glasses, and they come in a variety of lens styles. You can order them with clear lenses, prescription lenses, transition lenses, or the OG sunglass lenses, as well as in a variety of fits, including standard, large, or high-bridge frames. Improvements to this generation include an upgrade to a 12-MP camera and up to eight hours of battery life; writer Boone Ashworth’s testing clocked in at five to six hours.
-

 Fashion4 days ago
Fashion4 days agoFrance’s LVMH Q1 revenue falls 6%, shows resilience amid Iran war
-

 Sports7 days ago
Sports7 days agoThe case for Man United’s Fernandes as Premier League’s best
-

 Entertainment1 week ago
Entertainment1 week agoPalace left in shock as Prince William cancels grand ceremony
-

 Business1 week ago
Business1 week agoUK could adopt EU single market rules under new legislation
-
 Entertainment5 days ago
Entertainment5 days agoIs Claude down? Here’s why users are seeing errors
-

 Sports1 week ago
Sports1 week agoLamar Jackson hits back at critics with faithful message on social media
-

 Fashion1 week ago
Fashion1 week agoEnergy emerges as biggest cost driver in textile margins
-

 Business7 days ago
Business7 days agoDelta Air Lines unveils first new Delta One suite in premium cabin arms race


%2520Shiny%2520Black%2520Green%2520Lenses.png)




