Tech
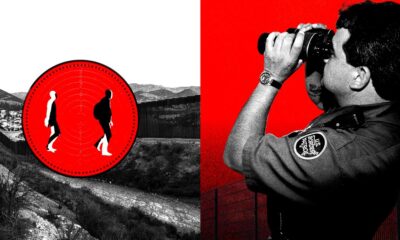
DHS Kept Chicago Police Records for Months in Violation of Domestic Espionage Rules

On November 21, 2023, field intelligence officers within the Department of Homeland Security quietly deleted a trove of Chicago Police Department records. It was not a routine purge.
For seven months, the data—records that had been requested on roughly 900 Chicagoland residents—sat on a federal server in violation of a deletion order issued by an intelligence oversight body. A later inquiry found that nearly 800 files had been kept, which a subsequent report said breached rules designed to prevent domestic intelligence operations from targeting legal US residents. The records originated in a private exchange between DHS analysts and Chicago police, a test of how local intelligence might feed federal government watchlists. The idea was to see whether street-level data could surface undocumented gang members in airport queues and at border crossings. The experiment collapsed amid what government reports describe as a chain of mismanagement and oversight failures.
Internal memos reviewed by WIRED reveal that the dataset was first requested by a field officer in the DHS’s Office of Intelligence & Analysis (I&A) in the summer of 2021. By then, Chicago’s gang data was already notorious for being riddled with contradictions and error. City inspectors had warned that police couldn’t vouch for its accuracy. Entries created by police included people purportedly born before 1901 and others who appeared to be infants. Some were labeled by police as gang members but not linked to any particular group.
Police baked their own contempt into the data, listing people’s occupations as “SCUM BAG,” “TURD,” or simply “BLACK.” Neither arrest nor conviction was necessary to make the list.
Prosecutors and police relied on the designations of alleged gang members in their filings and investigations. They shadowed defendants through bail hearings and into sentencing. For immigrants, it carried extra weight. Chicago’s sanctuary rules barred most data sharing with immigration officers, but a carve-out at the time for “known gang members” left open a back door. Over the course of a decade, immigration officers tapped into the database more than 32,000 times, records show.
The I&A memos—first obtained by the Brennan Center for Justice at NYU through a public records request—show that what began inside DHS as a limited data-sharing experiment seems to have soon unraveled into a cascade of procedural lapses. The request for the Chicagoland data moved through layers of review with no clear owner, its legal safeguards overlooked or ignored. By the time the data landed on I&A’s server around April 2022, the field officer who had initiated the transfer had left their post. The experiment ultimately collapsed under its own paperwork. Signatures went missing, audits were never filed, and the deletion deadline slipped by unnoticed. The guardrails meant to keep intelligence work pointed outward—toward foreign threats, not Americans—simply failed.
Faced with the lapse, I&A ultimately killed the project in November 2023, wiping the dataset and memorializing the breach in a formal report.
Spencer Reynolds, a senior counsel at the Brennan Center, says the episode illustrates how federal intelligence officers can sidestep local sanctuary laws. “This intelligence office is a workaround to so-called sanctuary protections that limit cities like Chicago from direct cooperation with ICE,” he says. “Federal intelligence officers can access the data, package it up, and then hand it off to immigration enforcement, evading important policies to protect residents.”
Tech
Europe’s Online Age Verification App Is Here

The European online age verification app is ready.
The app works with passports or ID cards, is built to be “completely anonymous” for the people who use it, works on any device (smartphones, tablets, and PCs), and is open source. “Best of all, online platforms can easily rely on our age verification app, so there are no more excuses,” said European Commission president Ursula von der Leyen at a press conference on Wednesday. “Europe offers a free and easy-to-use solution that can protect our children from harmful and illegal content.”
High Expectations
“It is our duty to protect our children in the online world just as we do in the offline world. And to do that effectively, we need a harmonized European approach,” von der Leyen said at Wednesday’s press conference. “And one of the central issues is the question, how can we ensure a technical solution for age verification that is valid throughout Europe? Today, I can announce that we have the answer.”
This answer takes the form of an open source app that any private company can repurpose, as long as it complies with European privacy standards and offers the same technical solution throughout the European Union. The user downloads the app, agrees to the terms and conditions, sets up a pin or biometric access, and proves their age through an electronic identification system, or by showing a passport or ID card (in which case biometric verification is also provided). The app does not store your name, date of birth, ID number, or any other personal information, according to the European Commission—only the fact that you are over a certain age.
After that, when a person using the app wants to access a social network (minimum age: 13), pornographic site (minimum age: 18), or any other age-protected content, if they are logged in from a computer, they need only scan the QR code shown on the site they want to visit. If, on the other hand, the person logs in from a smartphone, the app sends the proof of age directly. The platform does not access the document with which the user proved it in the first place.
Adoption Event
The need to introduce a common system for the entire European Union has been discussed for some time, and according to commission technicians, the technical work is now complete. Of course, it will still be possible to circumvent the system—all it takes is for an adult to lend their phone to a younger friend—but the technological architecture exists, and it will be up to EU member states to decide whether to integrate it into national digital wallets or develop independent apps.
“No More Excuses”
For the app to really be effective, platforms must be obligated to verify the age of their users—that’s where things get tricky. The Digital Services Act, which went into effect in 2024, requires “very large online platforms”—those with more than 45 million monthly users in the European Union—to take concrete steps to mitigate systemic risks related to child protection, with heavy penalties for noncompliance.
“And that’s why Europe has the DSA: to call online platforms to their responsibilities. Because Europe will not tolerate platforms making money at the expense of our children,” European Commission executive vice president Henna Virkkunen told a press conference. She added that after an investigation into TikTok, the European institutions plan to take similar action against Facebook, Instagram, and Snapchat, as well as four porn sites. “Since the platforms do not have adequate age verification tools, we developed the solution ourselves,” he concluded. In short, as von der Leyen also remarked, “there are no more excuses.”
Bare Minimum
So far, this is the European framework that sets the general rules. On this basis, member states can consider more restrictive measures. Italy was among the first to discuss how to regulate the use of social media by minors but has so far not landed on anything concrete. Elsewhere in the EU, France’s Emmanuel Macron has been a trailblazer on the issue, pushing France to discuss a rule to ban social networks for minors under the age of 15 entirely. So far, this measure has received broad political support—but the outcome depends largely on compatibility with the Digital Services Act and the availability of effective age verification systems like the app the European Commission just released.
This article originally appeared on WIRED Italia and has been translated.
Tech
Anthropic Plots Major London Expansion

Anthropic is moving into a new London office as it seeks to expand its research and commercial footprint in Europe, setting up a scrap between the leading AI labs for talent emerging from British universities.
The company, which opened its first London office in 2023, is moving to the same neighborhood as Google DeepMind, OpenAI, Meta, Wayve, Isomorphic Labs, Synthesia, and various AI research institutions.
Anthropic’s new, 158,000-square-foot office footprint will have space enough for 800 people—four times its current head count—giving it room to potentially outscale OpenAI, which itself recently announced an expansion in London.
“Europe’s largest businesses and fastest-growing startups are choosing Claude, and we’re scaling to match,” says Pip White, head of EMEA North at Anthropic. “The UK combines ambitious enterprises and institutions that understand what’s at stake with AI safety with an exceptional pool of AI talent—we want to be where all of that comes together.
UK government officials had reportedly attempted to coax Anthropic into expanding its presence in London after the company recently fell out with the US administration. Anthropic refused to allow its models to be used in mass surveillance and autonomous weapon systems, leading to an ongoing legal battle between the AI lab and the Pentagon.
As part of the expansion, Anthropic says it will deepen its work with the UK’s AI Security Institute, a government body that this week published a risk evaluation of its latest model, Claude Mythos Preview. According to Politico, the UK government is one of few across Europe to have been granted access to the model, which Anthropic has released to only select parties, citing concerns over the potential for its abuse by cybercriminals.
The increasing concentration of AI companies in the same London district is an important step in creating a pathway for research to translate into AI products, says Geraint Rees, vice-provost at University College London, whose campus is around the corner from Anthropic’s new office.
“This cluster didn’t emerge from a planning document. It grew because serious researchers and companies understand that proximity isn’t a nice-to-have,” he said last month, speaking at an event attended by WIRED. “That’s how the innovation system actually works. It’s not a clean, linear transfer from lab to market. It’s messier, richer, more human than that.”
Tech
CYBERUK ’26: UK lagging on legal protections for cyber pros | Computer Weekly

The increasingly long-in-the-tooth Computer Misuse Act (CMA) of 1990 remains an albatross around the neck of British cyber security professionals, and even though the UK government committed last December to reforming it, every minute of delay is holding back the nation’s security innovation, resilience, talent, and ability to defend itself against cyber attacks, campaigners have warned.
Ahead of the National Cyber Security Centre’s (NCSC’s) upcoming CYBERUK conference in Glasgow, the CyberUp Campaign for reform of the Computer Misuse Act (CMA) has published a new report, titled Protections for Cyber Researchers: How the UK is being left behind to maintain pressure on Westminster.
The CMA defines the vague offence of unauthorised access to a computer, which the campaigners want changed because it was written 35 years ago and fails to account for the development of the cyber security profession, and the fact that in the course of their day-to-day work, cyber pros may sometimes need to hack into other systems.
“Cyber attacks are growing in scale, sophistication and severity, with a devastating impact on infrastructure, businesses and charities,” said a CyberUp campaign spokesperson.
“While other countries have moved to refresh their cyber laws in response, the UK’s Computer Misuse Act hasn’t been updated since before the modern internet – hardly the best platform for accelerating our defences into the next decade.”
The group’s report highlights how other nations, Australia, Belgium, France, Germany, Hong Kong, Malta, Portugal, and the USA, have already secured legal protections for cyber professionals that enable them to go about their business without fear of prosecution.
In Portugal – Britain’s oldest formal ally under a treaty dating back to the 14th Century – the government last year published Decreto-Lei 125/2025, implementing the European Union (EU) Network and Information Systems (NIS2) Directive and revising the country’s cyber crime law to ensure that ethical hackers and professional cyber security practitioners working in good faith are both recognised and protected.
Portgual’s laws now accept some elements of cyber work may have to happen without explicit permission or involve unanticipated technical overreach that has a legitimate purpose.
As such, Portugal says that security work undertaken in good faith won’t be punished as long as the researcher fulfills a set of conditions. For example, they can act only to find vulnerabilities and these must be reported immediately, they must avoid taking harmful actions, like conducting DDoS attacks or installing malware, and they must respect the integrity of any data they may find or access and delete it within 10 days once the issue is addressed.
CyberUp said Portugal’s example demonstrates how cyber crime laws can be modernised to legally protect research carried out in the public interest.
“Portugal has demonstrated how to modernise their equivalent law through cyber legislation. We urge the government to follow this example and act swiftly through the Cyber Security and Resilience Bill to achieve meaningful reform, or risk lagging even further behind our peers,” the spokesperson said.
Defence Framework
Working with cyber security experts and legal advisors, the CyberUp campaign has developed its own Defence Framework that would allow cyber professionals to present a statutory defence in court as long as they adhere to the Framework’s four core principles.
- Harm Vs. Benefit: The benefits of the activity must outweigh the potential harms;
- Proportionality: Cyber pros must take all reasonable steps to minimise the risks of their activity;
- Intent: They must act honestly, sincerely, and clearly direct themselves towards improving security;
- Competence: Their qualifications and professional memberships should demonstrate they are suitably equipped to perform cyber security work.
The campaigners say this framework will bring clarity and confidence to the security sector, enabling cyber pros to run essential research tasks without fear of criminal prosecution, helping organisations operate to recognised legal standards, and enabling a more open and collaborative relationship between the cyber sector and the UK government.
-

 Entertainment1 week ago
Entertainment1 week agoQueen Elizabeth II emotional message for Archie, Lilibet sparks speculation
-

 Tech1 week ago
Tech1 week agoAzure customers up in arms over ‘full’ UK South region | Computer Weekly
-

 Tech1 week ago
Tech1 week agoAs the Strait of Hormuz Reopens, Global Shipping Will Take Months to Recover
-

 Fashion1 week ago
Fashion1 week agoCII submits 20-pt agenda to Indian govt to back firms hit by Iran war
-

 Tech1 week ago
Tech1 week agoThis AI Button Wearable From Ex-Apple Engineers Looks Like an iPod Shuffle
-

 Politics6 days ago
Politics6 days agoIndian airlines hit hardest after Dubai limits foreign flights until May 31
-

 Entertainment4 days ago
Entertainment4 days agoPalace left in shock as Prince William cancels grand ceremony
-

 Politics6 days ago
Politics6 days agoChinese, Taiwanese will unite, Xi tells Taiwan opposition leader