Tech
French court ruling may lead to legal challenges over state Sky ECC and EncroChat phone hack | Computer Weekly

The French supreme court has turned to the European Court of Justice to decide whether EU citizens have the right to challenge the legality of evidence obtained by French law enforcement by hacking the Sky ECC cryptophone network.
The Cour de Cassation has asked the European Court of Justice to rule whether French law is in line with European law. It comes after the French courts refused the right of a German citizen to appeal against the lawfulness of the French hacking operation in the French courts.
The decision will have “significant consequences” for legal proceedings in the European Union against individuals who are charged with criminal offences based on evidence obtained by French police from hacking the Sky ECC and EncroChat encrypted phone networks.
French, Belgian and Dutch police infiltrated servers belonging to Sky ECC, the world’s largest cryptophone network, and decrypted millions of messages between June 2019 and March 2021, leading to the arrest of drug gangs across Europe.
French and Dutch police also harvested messages from tens of thousands of EncroChat cryptophone users after police infiltrated the network’s servers in a novel hacking operation in 2020. A three-year investigation led to 6,500 arrests of organised crime and drug groups worldwide and the seizure of nearly €900m in cash and assets.
France ‘breached European law’
A coalition of defence lawyers, known as the Joint Defence Team, are challenging the legality of the French hacking operation. They argue that France breached European law by obtaining millions of encrypted messages from Sky ECC and EncroChat without grounds for suspicion against the individuals targeted.
They also argue that the French failed to notify other EU states in advance about when they intercepted messages from phones outside of French territory, denying other EU member states the right to object to the operation.
The defence lawyers say that their argument gained extra weight after the French supreme court ruling in June 2025. The court stated that EU states engaged in cross-border digital investigations must formally notify other EU states when intercepting data in their jurisdiction – an obligation defence lawyers say has been ignored in the Sky ECC operation.
No legal recourse
Individuals facing prosecution have been denied the right to challenge the lawfulness of the French hacking operations before judges in their own country, because the “mutual recognition” principle requires EU member states to accept evidence provided by other member states under European Investigation Orders (EIOs).
At the same time, people have been denied the right to challenge evidence in the French courts, leaving people charged with offences based on intercepted Sky ECC or EncroChat messages without legal recourse to appeal.
German lawyer Christian Lödden and French lawyer Guillaume Martine filed an appeal on behalf of a man accused of crimes based partly on evidence from Sky ECC intercepts in Germany, in the Paris Court of Appeal in June 2024, seeking to challenge the lawfulness of the Sky ECC data. The court ruled that the man was not entitled to be heard by the French Court.
Lödden, working with a network of European defence lawyers, appealed the decision in the French supreme court in February last year.
Decision will have ‘significant consequences’
The supreme court found that under French law, it was not possible for people accused of crimes in other countries to bring an appeal in France to challenge the lawfulness of the evidence, when it had been shared with another country under an EIO.
But the court also recognised the right of defendants to seek legal redress, and in a ruling on 16 September, the French supreme court asked the Court of Justice of the European Union to determine if there is a conflict between French and European law.
“The interpretation requested is likely to have significant consequences…in proceedings currently underway in various member states of the EU, where prosecutions rely on evidence similar to that contested here, all originating from the Sky ECC procedure,” the court said in its ruling.
‘Fishing with dynamite’
Lödden told Computer Weekly that the French operation to hack Sky ECC, amounted to a mass surveillance operation against 170,000 devices across the world, without concrete grounds for suspicion against individual phone users required under European law. “It was like fishing with dynamite,” he said.
Under current law, it was not possible to have a court review the lawfulness of the interception operations against Sky ECC and EncroChat, he said, adding: “That is totalitarianism, not the rule of law.”
Justus Reisinger, a Dutch defence lawyer, said that the French supreme court decision “created a possibility of having a real effective remedy” against Sky ECC.
No judge has so far decided on the lawfulness of evidence obtained by French police by hacking encrypted phones in other countries without notifying those countries in advance and giving them a chance to object, he said.
“The Court of Justice of the European Union and the French Cour de Cassation agree that interception is unlawful if there is no notification, and there has been no notification. If this case is found admissible, then the outcome is almost certainly they will declare [the Sky ECC evidence] unlawful,” he added.
France, which carried out the Sky ECC hacking operation, obtained the data on the premise that it would bring prosecutions against individuals involved in running the Sky ECC network, including its founder Jean-Francois Eap and distributor Thomas Herdman.
French police went further and gathered data from Sky ECC phones worldwide, which it provided to law enforcement agencies in other countries investigating organised crime groups who were using the encrypted phones.
The Court of Justice of the European Union is expected to take up to a year and a half to respond to the French supreme court.
Tech
How Trump’s Plot to Grab Iran’s Nuclear Fuel Would Actually Work

President Donald Trump and top defense officials are reportedly weighing whether to send ground troops to Iran in order to retrieve the country’s highly enriched uranium. However, the administration has shared little information about which troops would be deployed, how they would retrieve the nuclear material, or where the material would go next.
“People are going to have to go and get it,” secretary of state Marco Rubio said at a congressional briefing earlier this month, referring to the possible operation.
There are some indications that an operation is close on the horizon. On Tuesday, The Wall Street Journal reported that the Pentagon has imminent plans to deploy 3,000 brigade combat troops to the Middle East. (At the time of writing, the order has not been made.) The troops would come from the Army’s 82nd Airborne Division, which specializes in “joint forcible entry operations.” On Wednesday, Iran’s government rejected Trump’s 15-point plan to end the war, and White House press secretary Karoline Leavitt said that the president “is prepared to unleash hell” in Iran if a peace deal is not reached—a plan some lawmakers have reportedly expressed concern about.
Drawing from publicly available intelligence and their own experience, two experts outlined the likely contours of a ground operation targeting nuclear sites. They tell WIRED that any version of a ground operation would be incredibly complicated and pose a huge risk to the lives of American troops.
“I personally think a ground operation using special forces supported by a larger force is extremely, extremely risky and ultimately infeasible,” Spencer Faragasso, a senior research fellow at the Institute for Science and International Security, tells WIRED.
Nuclear Ambitions
Any version of the operation would likely take several weeks and involve simultaneous actions at multiple target locations that aren’t in close proximity to each other, the experts say. Jonathan Hackett, a former operations specialist for the Marines and the Defense Intelligence Agency, tells WIRED that as many as 10 locations could be targeted: the Isfahan, Arak, and Darkhovin research reactors; the Natanz, Fordow, and Parchin enrichment facilities; the Saghand, Chine, and Yazd mines; and the Bushehr power plant.
According to the International Atomic Energy Agency, Isfahan likely has the majority of the country’s 60 percent highly enriched uranium, which may be able to support a self-sustaining nuclear chain reaction, though weapon-grade material generally consists of 90 percent enriched uranium. Hackett says that the other two enrichment facilities may also have 60 percent highly enriched uranium, and that the power plant and all three research reactors may have 20 percent enriched uranium. Faragasso emphasizes that any such supplies deserve careful attention.
Hackett says that eight of the 10 sites—with the exception of Isfahan, which is likely intact underground, and “Pickaxe Mountain,” a relatively new enrichment facility near Natanz—were mostly or partially buried after last June’s air raids. Just before the war, Faragasso says, Iran backfilled the tunnel entrances to the Isfahan facility with dirt.
The riskiest version of a ground operation would involve American troops physically retrieving nuclear material. Hackett says that this material would be stored in the form of uranium hexafluoride gas inside “large cement vats.” Faragasso adds that it’s unclear how many of these vats may have been broken or damaged. At damaged sites, troops would have to bring excavators and heavy equipment capable of moving immense amounts of dirt to retrieve them
A comparatively less risky version of the operation would still necessitate ground troops, according to Hackett. However, it would primarily use air strikes to entomb nuclear material inside of their facilities. Ensuring that nuclear material is inaccessible in the short to medium term, Faragasso says, would entail destroying the entrances to underground facilities and ideally collapsing the facilities’ underground roofs.
Softening the Area
Hackett tells WIRED that based on his experience and all publicly available information, Trump’s negotiations with Iran are “probably a ruse” that buys time to move troops into place.
Hackett says that an operation would most likely begin with aerial bombardments in the areas surrounding the target sites. These bombers, he says, would likely be from the 82nd Airborne Division or the 11th or 31st Marine Expeditionary Units (MEU). The 11th MEU, a “rapid-response” force, and the 31st MEU, the only Marine unit continuously deployed abroad in strategic areas, have reportedly both been deployed to the Middle East.
Tech
Amazon’s Spring Sale Is So-So, but Cadence Capsules Are a Bright Spot

The WIRED Reviews Team has been covering Amazon’s Big Spring Sale since it began at on Wednesday, and the overall deals have been … not great, honestly. So far, we’ve found decent markdowns on vacuums, smart bird feeders, and even an air fryer we love, but I just saw that Cadence Capsules, those colorful magnetic containers you may have seen on your social media pages, are 20 percent off. (For reference, the last time I saw them on sale, they were a measly 9 percent off.)
If you’re not familiar, they allow you to decant your full-sized personal care products you use at home—from shampoo and sunscreen to serums and pills—into a labeled, modular system of hexagonal containers that are leak-proof, dishwasher safe, and stick together magnetically in your bag or on a countertop. No more jumbled, travel-sized toiletries and leaky, mismatched bottles and tubes.
Cadence Capsules have garnered some grumbling online for being overly heavy or leaking, but I’ve been using them regularly for about a year—I discuss decanting your daily-use products in my guide to How to Pack Your Beauty Routine for Travel—and haven’t experienced any leaks. They do add weight if you’re trying to travel super-light, and because they’re magnetic, they will also stick to other metal items in your toiletry bag, like bobby pins or other hair accessories. This can be annoying, especially if you’re already feeling chaotic or in a hurry.
Otherwise, Capsules are modular, convenient, and make you feel supremely organized—magnetic, interchangeable inserts for the lids come with permanent labels like “shampoo,” “conditioner,” “cleanser,” and “moisturizer.” Maybe you love this; maybe you don’t. But at least if you buy on Amazon, you can choose which label genre you get (Haircare, Bodycare, Skincare, Daily Routine). If this just isn’t your jam, the Cadence website offers a set of seven that allows you to customize the color and lid label of each Capsule, but that set is not currently on sale.
Tech
Fellow Readers, Don’t Miss These E-Reader Sales
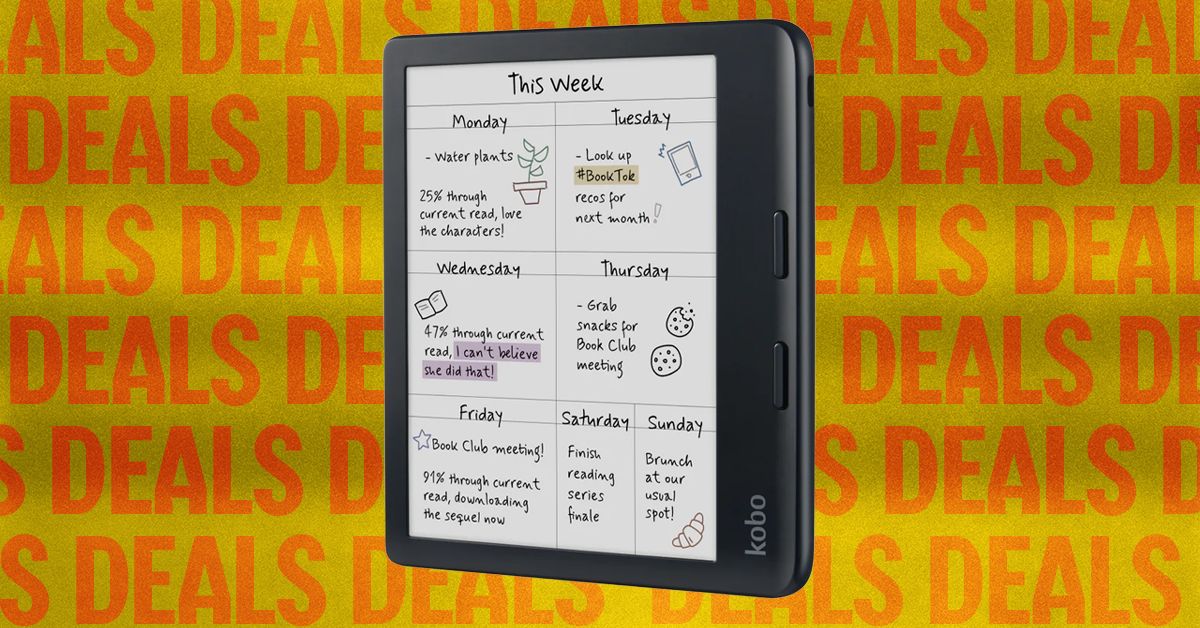
This is the older Kindle Scribe, but the price and features are the best you’ll get, especially when it’s on sale like this. I still reach for this model even though I have the newer third generation, and keep in mind the second generation will also get some of the newer software and experiences over time. With the sale, it’s half the price of the newer model.
If you’re already a Kindle reader and looking to upgrade, it’s likely because you want a new feature like a color screen. While the Kobo above is the better buy, if you want to stay in the Kindle ecosystem but add some color to your books, both the Colorsoft and Colorsoft Signature are on sale.
If you’re looking to spend as little as possible, the basic Kindle (11th generation) is still a great e-reader and is currently under $100. It can do almost everything the other Kindles can (except the Scribe) on a snappy black-and-white screen. It doesn’t have a warm front light either, but it’s still a great purchase for the price.
Power up with unlimited access to WIRED. Get best-in-class reporting and exclusive subscriber content that’s too important to ignore. Subscribe Today.
-

 Fashion1 week ago
Fashion1 week agoSales at US apparel, clothing accessories stores up 4% YoY in Jan 2026
-

 Tech1 week ago
Tech1 week agoJustice Department Says Anthropic Can’t Be Trusted With Warfighting Systems
-

 Fashion1 week ago
Fashion1 week agoSpain’s Inditex FY25 sales rise 3.2% to $46.28 bn amid strong demand
-

 Politics1 week ago
Politics1 week agoIran strikes Tel Aviv with cluster-warhead missiles in retaliation of Larijani’s martyrdom
-

 Sports1 week ago
Sports1 week agoMarch Madness 2026 – How to watch in SA, start time, schedule, TV channel for NCAA championship basketball tournament
-

 Entertainment1 week ago
Entertainment1 week agoVal Kilmer revived 1 year after death through AI
-

 Entertainment1 week ago
Entertainment1 week agoWith few new leads 45 days after Nancy Guthrie’s disappearance, investigation “becomes much harder,” expert says
-

 Business1 week ago
Business1 week agoBrits cashing in jewellery as gold price hits record high








