Tech
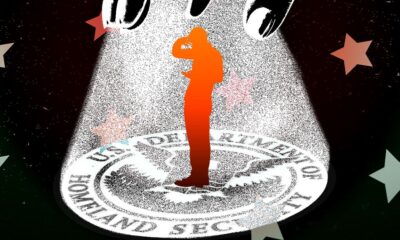
Iranian Hackers Breached Kash Patel’s Email—but Not the FBI’s

Handala’s second claim, however—that it hacked the FBI—seems, for now, to be fiction. All evidence points to Handala having breached Patel’s older, personal Gmail account. Widely believed to be a “hacktivist” front for Iran’s intelligence agency the MOIS, Handala suggested on its website that the emails contained classified information, but the messages initially reviewed by WIRED didn’t appear to be related to any government work. TechCrunch did find, however, that Patel appears to have forwarded some emails from his Justice Department email account to his Gmail account in 2014.
Handala, which cybersecurity experts have described to WIRED as an “opportunistic” hacker group whose cyberattacks and breaches are often calculated more for their propaganda value than their tactical impacts, has nonetheless made the most of Patel’s embarrassing breach. “To the whole world, we declare: the FBI is just a name, and behind this name, there is no real security,” the group wrote in its statement. “If your director can be compromised this easily, what do you expect from your lower-level employees?”
Handala Hackers Put $50 Million Bounty on Trump and Netanyahu’s Heads
For further evidence of Handala’s bombastic rhetoric, look no further than another post on its website earlier this week (we’re intentionally not linking to it) that offered a $50 million bounty to anyone who could “eliminate” US president Donald Trump and Israeli prime minister Benjamin Netanyahu. “This substantial prize will be awarded, directly and securely, to any individual or group bold enough to show true action against tyranny,” the hackers’ statement read, along with an invitation to any would-be assassins to reach out via the encrypted messaging app Session. “All our communication and payment channels utilize the latest encryption and anonymization technologies, your safety and confidentiality are fully guaranteed.”
That bounty, Handala explained, was posted in answer to a statement about Handala published on the US Department of Justice website last week that offered $10 million for information leading to the identity or location of anyone who carries out “malicious cyber activities against US critical infrastructure” on behalf of a foreign government.
“Our message is clear: If you truly have the will and the power, come and find us!” Handala wrote in its response. “We fear no challenge and are prepared to respond to every attack with even greater force.”
In yet another post on its website this week, Handala also claimed to have doxed 28 engineers at military contractor Lockheed Martin working in Israel and threatened them with personal harm if they didn’t leave the country within 48 hours. When WIRED tried calling the phone numbers included in Handala’s leaked data, however, most of them didn’t work.
Apple says no device with its Lockdown Mode security feature enabled has ever been successfully compromised by mercenary spyware in the nearly four years since its launch. Amnesty International’s security lab head, Donncha Ó Cearbhaill, also says his team has seen no evidence of a successful attack against a Lockdown Mode–enabled iPhone. And Citizen Lab, which has documented several successful spyware attacks against iPhones, says none involve a Lockdown Mode bypass, while in two cases its researchers found the feature actively blocked attacks against NSO Group’s Pegasus and Intellexa’s Predator. Google researchers, meanwhile, found one spyware strain that simply abandons infection attempts when it detects the feature is enabled.
Lockdown Mode works by disabling commonly exploited iPhone features, such as most message attachment types and features like links and link previews. Incoming FaceTime calls are blocked unless the user has previously called that person within the past 30 days. When the iPhone is locked, it blocks connections with computers and accessories. The device will not automatically join nonsecure Wi-Fi networks, and 2G and 3G support is disabled. Apple has also doubled bounties for researchers who detect any Lockdown Mode bypass, with payouts up to $2 million.
Tech
IDCA datacentres report: Global concentration and the Goldilocks zone | Computer Weekly

Datacentre capacity has reached 67.7GW globally, with five countries accounting for 69% of that total, and the US alone accounting for 43%, according to the International Datacentre Authority’s (IDCA) Datacentre report 2026.
The study based its research on data from organisations such as the International Energy Agency, World Bank, United Nations and International Telecommunications Union, as well as governments, datacentre developers and operators.
It discovered that where datacentres account for 5% or more of electricity grid usage, there seemed to be a threshold at which public opposition rises significantly and governments move from incentives to regulation.
And while there was huge growth in the datacentre industry, whether a nation or region can profit optimally depended on using its resources wisely and attaining tech sector skills among 2.5% of the workforce, it found.
The US was the site for the most datacentre capacity, with 29.2GW of a global total 67.7GW. US datacentres accounted for 6% of the country’s electricity supply. Behind the US are: China, 8.5GW and 0.8% of electricity use; Germany, 5.5GW (9.5%), UK, 2GW (5.8%), and Japan, 1.7GW (1.5%). Those five states accounted for 69% of global datacentre capacity.
In the US, however, the IDCA research estimated that 13% of datacentre consumption – around 3GW – was unused but still live capacity.
China emerged as the “sleeping giant”, according to the report, because less than 1% of electricity production was devoted to datacentres, despite producing almost twice the amount of electricity as the US.
International haves and have-nots
The report concluded that 5% of electricity grid usage going to datacentres was the threshold at which public concern, government regulation and grid supply can be seen to increase. It pointed to the US, which has seen community pushback and connection difficulties in the Midwest, Texas and California, with multi-year delays in the ability to provision power new facilities.
Meanwhile, in Europe, the Netherlands, Germany, and Switzerland have exceeded the 9% consumption level, while that’s also the case for Singapore.
Also in Europe, the report found that countries with electricity grids driven by nuclear power – such as France, Slovakia and Slovenia – may relieve these constraints.
At the other end of the scale, it discovered that more than 70 countries devoted less than 0.1% of their power to datacentres, and for more than 30 countries that figure was less than 0.01%.
Datacentre energy use league table
Singapore used the highest proportion of its electricity to power datacentres at 19.5% of the total generated. Next in the IDCA report was Lithuania (11.1%), the Netherlands (9.7%), Denmark (8.4%), Ireland (8.2%), Estonia (6.9%), Luxembourg (6.3%), Germany (6.1%), Hong Kong (6%) and the US (6%). Further down the rankings are Australia (5.1%), the UK (3.6%), South Korea (2%), Japan (1.2%), and India and China (both 0.8%).
IDCA built what it described as an optimised national model of ideal consumption levels for each nation, noting that construction of new datacentres was contingent on stronger electricity grids and robust fibre-optic networks.
For developed nations, IDCA said 6.25% of national electricity consumption was an effective cap on datacentre growth – i.e., it was the point at which the correlation was very strong between datacentre consumption and political actions and community pushback that result in projects being cancelled or slowed.
Meanwhile, IDCA ranked countries by the headroom they possess to build datacentres without significantly needing to develop new electricity generation. Here, IDCA ranked countries by headroom measured in GW. China led the way with 58.9GW of headroom, followed by India (12.7GW), Russia (6.7GW), Japan (5.5GW), Brazil (4.5GW), Canada (3.6GW), South Korea (3.2GW), Saudi Arabia (2.6GW), Iran (2.4GW) and Mexico (2.4GW).
The water stress scale
IDCA pointed out that modern AI datacentres require liquid cooling but that a lot of pushback around perceived worries over water use are misguided. That’s because the latest direct-to-chip cooling systems are closed systems that recycle water somewhat similar to a car radiator.
Having said that, the IDCA report stated: “The vast majority of existing traditional cloud and enterprise facilities rely on older, less efficient cooling architectures like water-cooled chillers or evaporative cooling towers. In these legacy designs, water is evaporated to remove the latent heat of vaporisation from the air, and that evaporated water is never recovered.”
The IDCA report ranked countries on a “water stress” scale of 0-100, where those with deserts are unsurprisingly high on the scale and mountainous and riverine states at the low end. Most at risk are Bahrain (100), Belize (86), Libya (80), Kuwait (80) and South Sudan (73). The least at risk are Norway (0), New Zealand (0), Iceland (1), Canada (2) and Bhutan (3).
Servers per head differential of 100,000x
The IDCA report said there was a difference of 100,000x in the number of servers per head of population between the most and least dense in this respect. Providing connectivity alongside this, IDCA said there was an estimated 1.3 to 1.5 million km of subsea cables, in around 550 systems, with about 1,200 landing stations.
Out of these, there are around 70 landing stations in the US, 50 in the UK and more than 12 in countries that include the Philippines, Indonesia, Japan, Spain, Denmark, Sweden and some Middle Eastern countries. Meanwhile, there are around 14 million km of terrestrial cables in main networks.
IT jobs deficit
IDCA found that IT jobs worldwide account for between 0.1% and 4% of populations. According to IDCA, 2.5% of the workforce employed in tech was optimum to “to ensure a thorough, successful digital economy creation and management”, though this varied based on local conditions and expectations.
Overall, the IDCA found that there was a deficit of 100 million IT-related jobs worldwide, with developing nations accounting for 80% of that.
Ranking countries with the most deficit, top of the list was India, with a shortfall of 28.8 million in the IT workforce, followed by China (17.5 million), Pakistan (5.8 million), Nigeria (5.8 million), and Indonesia (5.3 million).
Gamma, Sigma and Goldilocks
The report covered a number of other areas in connection with datacentres that include datacentre security, standards, design, investment and community pushback. It also provided three indexes: Gamma, Sigma and Goldilocks, with countries ranked 0-100.
The Gamma index looked at technological and social factors in digital readiness. Top of the list was: Finland at 85 (with Scandinavia collectively ranking 83), the Netherlands (83), Estonia (80), New Zealand (79) and Switzerland (79). Bottom of the list was: Equatorial Guinea (4), South Sudan (12), Turkmenistan (17), Haiti (17), and Democratic Republic of Congo (19). The UK ranked 14th, with a score of 74.
The Sigma index integrated the Gamma index, with adjustments for stress on water and electricity grids, such as the amount of headroom they possess, for example. The Sigma index was topped by Finland (99), followed by Sweden (97), Norway (97), New Zealand (94) and Iceland (94). The UK was ranked 15th (84).
“The Sigma Index is useful in determining a nation’s overall suitability for rapid datacentre growth and the digital infrastructure that would accompany it,” the report said.
Finally, the IDCA report provided a Goldilocks index, which technological factors are separated from the rest then comparing those to the cost of living and income. That way, it hoped to provide an idea of countries for whom rapid development would not be disruptive and would hit “just right”. Top of the Goldilocks index was Colombia with a score of 5.2, followed by North Macedonia, China, South Africa and Montenegro, all on 5.2 except the last of these (5.1).
Tech
Microsoft releases rare zero-day free Patch Tuesday update | Computer Weekly

Microsoft has addressed around 140 newly discovered common vulnerabilities and exposures (CVEs) in its May Patch Tuesday update, but for the first time in a long time, the latest monthly drop contains no zero-day flaws, meaning that none of the issues in scope have been actively exploited or publicly disclosed.
But while a less panic-inducing drop will be welcomed by security teams around the world, the May 2026 Patch Tuesday update contains almost 20 critical severity flaws that will inevitably draw the attention of threat actors in the coming days and weeks.
Jack Bicer, Action1 director of vulnerability research, said: “Although the absence of zero-days is a positive sign, the high number of critical vulnerabilities – particularly compared to recent months – means organisations should still move quickly to evaluate and deploy updates across affected systems.”
This month’s update is also particularly significant as it heralds a critical Secure Boot certificate expiration deadline on 26 June, a few weeks from now. Devices that fail to receive updated Secure Boot certificates – which are now rolling out – face potentially catastrophic failures or as-yet-undiscovered security flaws that may prove impossible to fix.
“The May 2026 update cycle is a high-stakes bridge to the 26 June certificate expiration deadline, making fleet-wide rotation to new trust anchors the month’s absolute priority,” said Rain Baker, senior incident response specialist at Nightwing’s ShadowScout team.
“For those who haven’t patched for last month’s releases for the Windows Shell and Microsoft Defender bypass flaws, it is imperative that security teams give these the highest priority,” added Baker.
Bugs abounding
Among some of the critical updates issued this month is a fix for a Windows DNS Client remote code execution (RCE) flaw tracked as CVE-2026-41096. This vulnerability stems from a heap-based buffer overflow condition in Windows NetLogon and could enable an unauthenticated actor to take over the target system by sending it a malicious DNS response.
“Because DNS is a core networking service used across enterprise environments, exploitation could impact a large number of systems rapidly,” said Action1’s Bicer.
“Successful attacks may lead to widespread endpoint compromise, ransomware deployment, credential harvesting, and operational disruption across corporate networks.
Bicer added: “This CVE requires immediate attention considering its severity rating, network-based attack vector, no authentication requirements, and no user interaction. DNS-related vulnerabilities are especially dangerous because they target foundational network services that are broadly exposed across enterprise infrastructure.”
Also drawing attention this evening is CVE-2026-42898, another RCE issue, this one in on-prem versions of Microsoft Dynamics 365, which bears a common vulnerability scoring system (CVSS) score of 9.9. Again, this issue requires no user interaction and because it can impact systems beyond the original security scope of the vulnerable component, carries an extreme risk to enterprises.
Previous attacks on Dynamics 365 infrastructure have exposed important, privileged data, and because CRM environments plug into so many other important systems, successful exploitation could lead to wholesale compromise.
Meanwhile, Automox chief technology officer Jason Kikta weighed in on CVE-2026-41089, an RCE flaw in Windows Netlogon, and CVE-2026-40402, an elevation of privilege (EoP) vulnerability in Hyper-V.
“CVE-2026-41089 – CVSS 9.8 out of 10 – is a stack-based buffer overflow in Windows Netlogon,” explained Kikta. “An attacker sends a crafted network request to a domain controller. No authentication required. No user interaction required. If you’ve been doing this long enough, the description language sounds sadly familiar.
“I’d be careful drawing a direct line to Zerologon. The underlying bug is a stack overflow, not a crypto protocol flaw, and Microsoft has not labeled this one as wormable. The mechanism is different, but the blast radius is still ugly when you’re talking about pre-auth code execution on a domain controller.”
The Hyper-V issue can be exploited by a low-privileged account inside a guest virtual machine (VM) to execute code on the host with system-level privileges. Kikta warned that one compromised guest could serve as a pivot point for every other VM on the same host, and the host fabric into the bargain. Hosted desktop environments and shared virtualisation platforms are likely to be swiftly targeted.
“Multi-tenant VDI, on-premises virtualisation with untrusted workloads, or any Hyper-V host running guests you don’t fully control. Same-week, same-day patch depending on what’s on top of it,” Kikta advised.
Patch apocalypse?
Lacking though it is in zero-days, Redmond’s latest meaty update will do little to assuage the concerns of onlookers alarmed at the supposedly earth-shattering vulnerability discovery capabilities of Anthropic’s Claude Mythos frontier AI model.
Chris Goettl, vice president of security product management at Ivanti, said that these concerns were being taken seriously by many key software suppliers and other tech firms that are becoming far more aggressive in their patching in response to the changes of the past few weeks.
“Oracle announced a new release cadence starting in May 2026 to address the acceleration of vulnerability detection introduced by Mythos and other AI security models; monthly Critical Security Patch Update (CSPUs) will fill in the two-month gap between their quarterly Critical Patch Update (CPU),” he said.
“Apple is another early participant in Project Glasswing and has seen a recent spike in the number of exposures resolved. They typically average around 20 CVEs per iOS security update [but] for their most recent update on May 11, there is a spike of 52 CVEs resolved. Across the 11 Apple updates, the CVE counts range from 25 at the low end to 52 on the high end and Apple backported changes all the way to iPhone 6s and iOS 15. While there are not actively exploited vulnerabilities, there are a lot of updates to manage.”
Meanwhile, Mozilla, the backers of the Firefox browser, which is said to have had over 270 vulnerabilities identified after Claude Mythos was applied to it, has also moved to a more aggressive weekly cadence for its security updates since the release of Firefox 150.0.0 in April 2026 – version 150.0.3 of Firefox dropped earlier today (12 May).
Tech
Hantavirus Conspiracy Theories Are Already Spreading Online

Conspiracy theorists, wellness influencers, and grifters have already started promoting wild claims about the hantavirus outbreak that began aboard the MV Hondius, a cruise ship on the Atlantic.
Some conspiracy theorists compared the outbreak to the Covid-19 pandemic, claiming it was another effort to control the global population, while others pushed a false narrative that the Covid-19 vaccine caused hantavirus. Many others promoted ivermectin as a treatment, using the incident as a way to sell emergency medical kits featuring the antiparasitic drug typically used as a horse dewormer.
In more recent days, many of these same people spreading conspiracy theories have promoted the baseless and antisemitic claims that the entire incident is a false flag orchestrated by Israel.
Conspiracy theories flooding social media in response to breaking news are nothing new, but what is notable about those being pushed around the hantavirus outbreak is just how closely they echo the conspiracy theories promoted during the Covid-19 pandemic.
“One of the most striking shifts since the Covid pandemic is how rapidly misinformation narratives now organize themselves around emerging outbreaks,” Katrine Wallace, an epidemiologist at University of Illinois Chicago School of Public Health, tells WIRED.
“Within hours of the first hantavirus headlines, social media accounts were already promoting ivermectin, attributing the outbreak to Covid vaccines, and warning about a hantavirus vaccine that does not exist. The claims themselves were often contradictory, but that contradiction no longer appears to limit their spread.”
Once the hantavirus outbreak started making headlines around the world, conspiracy theorists and grifters jumped into action, spreading dangerously ill-informed claims and, of course, trying to sell people ivermectin.
“Ivermectin should work against it,” Mary Talley Bowden wrote on X. Bowden, a doctor, is a prominent promoter of medical misinformation who has promoted ivermectin as a treatment for Covid-19 and prescribed ivermectin to a Covid-19 patient. Hours after her first post on Hantavirus went viral, she followed up to say that she is selling ivermectin to Texans. Bowden did not respond to a request for comment.
Her post, which has been viewed 4 million times, was shared by former Congresswoman Marjorie Taylor Greene, who added that vitamin D and zinc would help fight the infection. Greene even claimed that not getting the Covid-19 vaccine had somehow allowed her to “develop natural immunity” against hantavirus.
Greene separately claimed, without evidence, that the pharmaceutical company Moderna had purposely manipulated the virus in order to allow them to cash in by developing a hantavirus vaccine. Greene did not respond to a request for comment.
Other prolific health disinformation promoters boosted the ivermectin claims, including Simone Gold, the founder of Covid denial group America’s Frontline Doctors, and Peter McCullough, a disinformation peddler who promoted the “sudden death” conspiracy theory about the Covid-19 vaccine, which falsely claimed that those who received the shot were at risk of dropping dead without any warning.
McCullough is also the chief scientific officer for The Wellness Company, which has been described as “Goop for the GOP.” The company has used the hantavirus outbreak to promote a $325 “Contagion Emergency Kit” which includes both ivermectin and hydroxychloroquine.
All the false claims and posts about ivermectin gained enough traction online that the World Health Organization responded to say that there is no research to suggest ivermectin is an effective treatment for hantavirus.
Conspiracy theorists have, meanwhile, been pushing the baseless idea that a side effect of Covid vaccines includes a hantavirus infection.
-
 Tech1 week ago
Tech1 week agoDHS Demanded Google Surrender Data on Canadian’s Activity, Location Over Anti-ICE Posts
-

 Business1 week ago
Business1 week agoHeineken plans huge investment in hundreds of UK pubs ahead of World Cup
-

 Tech5 days ago
Tech5 days agoA new frontier: Identity stack evolves for agentic systems | Computer Weekly
-

 Tech4 days ago
Tech4 days ago‘Orbs,’ ‘Saucers,’ and ‘Flashes’ on the Moon: Pentagon Drops New UFO Files
-

 Business1 week ago
Business1 week agoIndia among most resilient large EMs, better placed for future global shocks; policy reforms & strong buffers help: Moody’s – The Times of India
-

 Fashion5 days ago
Fashion5 days agoNew orders in German manufacturing up 5% MoM in Mar 2026: Destatis
-

 Tech5 days ago
Tech5 days agoWhat Microsoft Executives Really Thought About OpenAI in 2018
-

 Business1 week ago
Business1 week agoUS denies Iranian report warship was struck by missiles

















