Tech
Labour scarcity is forcing IT leaders to rethink automation economics | Computer Weekly

It often feels as though every enterprise technology conversation now begins and ends with artificial intelligence (AI). New models, valuations and promises of transformation dominate the headlines. But when I speak with CIOs and CFOs, their urgency sounds different. They are not debating which AI platform will win. They are asking a more immediate question: how do we run this organisation with fewer people and tighter budgets and navigate more volatility than at any point in recent memory?
Labour has become a critical binding constraint — and the pressure is structural rather than cyclical.
Labour costs are now the biggest cost pressure facing firms, cited by 72% of UK businesses in the latest British Chambers of Commerce survey. And as the population ages, fewer working-age people will be available to support rising demand. The OECD forecasts that by 2060, the working-age population will decline by more than 30% in a quarter of advanced economies. The labour equation is tightening, not loosening. In a recent Censuswude survey of nearly 4,300 C-suites, 98% say a talent shortage is affecting their IT vision.
For enterprise and public sector organisations alike, that reality fundamentally changes the logic of IT investment.
Automation becomes economic logic
Labour is typically the largest operating expense in any organisation. When labour becomes scarcer and more expensive, automation stops being an innovation initiative and becomes an economic imperative. The CBI reports that 38% of businesses have been unable to grow or respond to demand due to labour shortages. We are approaching an automation tipping point: the moment when deploying intelligent automation becomes cheaper, faster and lower-risk than finding, hiring and retaining additional staff.
In highly competitive markets, lowering the cost-to-serve is not optional, but mandatory for survival. Organisations that thrive will not necessarily be those with the latest shiny toy systems, but those with a good product and the lowest sustainable operating cost. For UK public sector bodies, including NHS trusts and central government departments, the challenge is particularly acute. Consumer and citizen expectations continue to rise while budgets and recruitment capacity remain constrained. Doing more with the same or fewer resources is no longer aspirational. It is an operational reality.
The question, therefore, is not whether to automate, but how to do so pragmatically and without introducing unnecessary complexity or risk.
The reprioritisation moment
Many organisations remain tied to expensive maintenance cycles and vendor-driven upgrade roadmaps. Core enterprise software such as ERP still continue to run mission-critical processes, bringing together finance, HR, procurement and logistics. But high maintenance costs and forced platform upgrades, migrations and replatforming consume capital and scarce talent that could otherwise be directed toward productivity gains.
Increasingly, leaders are questioning whether every upgrade delivers real economic value, or whether capital would be better deployed on automation capabilities that sit above existing systems and target operational bottlenecks directly.
CIOs and CFOs face a simple reality: there is not enough time, money or people to pursue every vendor roadmap simultaneously. In fact, a recent IDC survey of 700 IT leaders across 10+ countries reveal 47% of organisations have delayed innovation due to upgrade requirements, and 92% feel locked into their ERP provider’s roadmap, limiting flexibility and driving dissatisfaction. Cloud migrations, AI add-ons, compliance initiatives and security upgrades may each have merit, but when bundled and mandated, siloed into a single system, they not only exceed available budgets and internal capacity, but erode their agility needed to adapt to changing landscapes and business needs.
Prioritisation is a strategic discipline rather than a tactical exercise.
Building on top of what already works
The most effective organisations are not ripping out core systems. Instead, they are building new capabilities on top of them using agentic AI. Rather than embarking on multi-year transformation programmes, they are identifying specific operational bottlenecks — such as manual data entry, slow procurement workflows or compliance reporting burdens — and layering targeted automation on top of existing platforms.
This incremental model delivers measurable time-to-value in weeks or months, not years. It reduces risk and allows organisations to prove returns before expanding further. Not every solution requires advanced AI. While AI is a powerful tool, it remains just one tool among many. The objective should always be to solve clearly defined business problems faster, better and more economically — not to pursue technology for its own sake.
For organisations balancing fiscal responsibility with investing in growth, that distinction matters.
Beyond the hype cycle
Technology markets will remain volatile. IT providers will reposition, new platforms will emerge and investment cycles will rise and fall. Demographic change, however, will outlast the hype.
Labour scarcity is not a temporary disruption. It is a structural shift that will define the next two decades of enterprise and public sector strategy. AI and automation can play a decisive role in responding to that shift — not as speculative transformation projects, but as pragmatic tools that enable organisations to adapt faster and to put people to work for higher-value, strategic initiatives rather than keeping the lights on.
The organisations that lead will not be those that adopt AI most aggressively. They will be those that apply automation deliberately; aligned with economic reality, workforce constraints, measurable time-to-value and long-term operational resilience.
Seth Ravin is CEO and chairman at third-party software support company, Rimini Street.
Tech
This Is the Next Wave of Political Fundraising
On Monday, streamer and content creator Hasan Piker helped raise more than $56,000 in one stream for Oliver Larkin, a former Bernie Sanders campaign staffer who is seeking to primary Jared Moskowitz, a moderate Democratic congressman from Florida. It was the most the campaign had raised “in a single day,” Larkin said on X shortly after the stream ended.
Over the past few years, creators have become an essential piece of campaign messaging strategy. But Piker’s recent stream for Larkin is the latest sign that online influence is being leveraged for direct fundraising as well.
Piker isn’t alone. Trisha Paytas, a YouTuber with more than 5 million subscribers and a long history of provocative stunts, isn’t known for her political activism, but in February she donated more than $10,000 to a campaign called Creators Against ICE. The campaign, organized by the creator collective Creators for Peace, is just one in a string of fundraisers organized by coalitions of creators turning social media followings into political fundraising machines.
Unlike traditional fundraising models like super PACs that pool funds from publicly reported donors, these creator collectives pool audiences and leverage social networks and off-the-shelf tools like Shopify and Tiltify to convert followers into donors. Creators for Peace is one of the most prominent groups in a line of creator coalitions mobilizing around causes from Gaza relief to immigration aid—establishing a model that could reshape grassroots fundraising ahead of the midterm elections.
“There are a lot of creators that I think recognize the power of having a platform,” says Hassan Khadair, one of the Creators for Peace organizers. “There’s more of a call to action culturally with creators than I think there’s ever been before.”
Creators for Peace was established in 2024 by Nikki Carreon in an Instagram group DM with a handful of other creators to raise money for Gaza relief. That group chat expanded into a more than 120-person Discord server that included influencers with millions of followers on platforms like Instagram, Twitch, and YouTube. People like Kurtis Conner, Hasan Piker, and the Try Guys, who collectively boast more than 15 million followers on their primary platforms, got involved. Members shared infographics with their audiences and organized a livestream. By the end of the campaign, the group had raised more than $1.6 million.
“We largely start from zero on each new campaign. I will individually reach out to several creators, we’ll get something out, and then once we allow that to catch fire on its own, a bunch of creators will reach out to us,” says Khadair. For the Creators for Peace immigration fundraiser, Khadair says, “we really wanted to try and move out of the leftist bubble just a little bit, because a lot of our audiences tend to align with us on these issues.”
By connecting with more apolitical creators like Paytas, the Creators Against ICE campaign has raised nearly $140,000 for the National Immigration Law Center, according to the group’s Tiltify fundraiser.
Creators have come under fire for remaining silent on political issues for years. During the 2020 Black Lives Matter protests, audiences began demanding that influencers creating content on anything from fashion to food publicly speak out and take sides on political issues. In these online spaces, silence is often seen as complicity.
Groups of Democratic political influencers, like UnderTheDeskNews, have also started raising funds for whistles to alert communities about the presence of ICE agents and community watch support as well. In February, around 80 creators were part of an anti-ICE merch fundraiser tied to Bad Bunny’s Super Bowl performance, selling T-shirts, hats, and stickers featuring the singer’s Sapo Concho mascot. The campaign raised more than $100,000 for immigration legal defense funds.
Tech
Meta Developed 4 New Chips to Power Its AI and Recommendation Systems
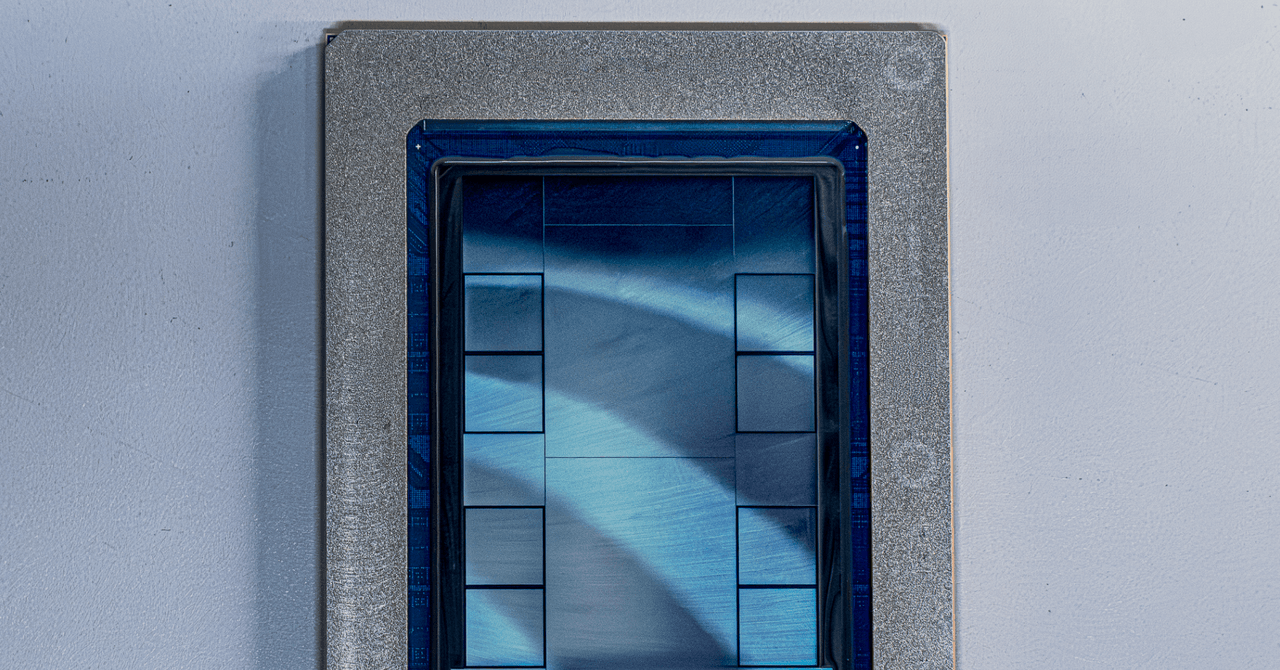
Meta announced Wednesday that it has developed four new computer chips that will be used to power generative AI features and content ranking systems within the tech giant’s own apps. The hardware will become part of Meta’s existing chip line known as MTIA, or Meta Training and Inference Accelerators.
Meta partnered with Broadcom to develop its latest semiconductors, which are built on top of the open-source RISC-V architecture. They’re being fabricated by Taiwan Semiconductor Manufacturing Corporation, the world’s leading chip producer.
One of the new MTIA chips, the MTIA 300, is already in production, and Meta says the other three—the MTIA 400, 450, and 500—are expected to ship sometime between early and late 2027. Putting out fresh silicon this quickly is unusual by most chip industry standards, but is essentially unheard of for a social media company that historically didn’t produce its own physical computing infrastructure.
YJ Song, a vice president of engineering at Meta, says that AI models are evolving faster than traditional chip development cycles, so AI workloads may change substantially by the time new hardware typically reaches production. “Rather than placing a bet and waiting for a long period of time, we deliberately take an iterative approach. Each MTIA generation builds on the last, using modular chiplets and incorporating the latest AI workload insights and hardware technologies,” Song said in a blog post.
The MTIA 300 will be used primarily for training algorithms that rank and recommend content to the hundreds of millions of people who use apps like Facebook and Instagram each day. The other three chips are designed to support inference, the process of running trained AI models to produce outputs like text or images.
The MTIA 400, which Meta claims delivers performance “competitive with leading commercial products,” has been tested and is expected to arrive at data centers soon. The MTIA 450 will have double the amount of high-bandwidth memory as the MTIA 400, and is supposed to ship in early 2027. Meta says the MTIA 500, which is slated to arrive later next year, will have even more memory than MTIA 450 and include “innovations in low-precision data.”
The MTIA chips are part of Meta’s broader strategy to hoard as much computing power as possible in order to develop cutting-edge artificial intelligence. Meta first shared details about its chip development plans in 2023, when it released its first product under the MTIA banner. As software companies and AI labs continue to train increasingly powerful AI models, they have begun announcing ambitious plans to build custom chips that serve their own specific AI needs. OpenAI, for example, has also said it’s partnering with Broadcom to build custom accelerators, following a path similar to Meta’s.
Earlier this year, Meta was reported to be scaling back some of its in-house efforts to make high-end chips that would compete more directly with leading players like Nvidia. The company now appears eager to dispel that narrative by announcing this new road map for MTIA chips. But making custom silicon remains enormously expensive and technically complex, which means Meta will likely continue purchasing the majority of its AI hardware from other firms, at least in the near future.
That reality is reflected in the company’s recent chip buying spree. Meta unveiled its new MTIA chips shortly after announcing multibillion dollar deals with Nvidia and AMD. The social media giant has also signed an agreement to rent chips made by Google.
Tech
Iran war a melting pot for other cyber threats | Computer Weekly

State-backed cyber threat actors from the likes of Belarus, China and Pakistan are all ramping up their activity in the wake of the joint Israeli-US attack on Iran, even though their government paymasters are not directly involved in the war.
This is according to intelligence published by Proofpoint, which claims to have observed several such campaigns unfolding in the wild. It believes this wave of malicious activity reflects a mixture of threat actors opportunistically using the conflict to create lures in their routine options, and intelligence collection directly related to Middle Eastern governments and their allies.
“These campaigns were conducted by both known groups and previously unobserved actors, with suspected attribution to China, Belarus, Pakistan and Hamas,” wrote Proofpoint’s research team.
“The campaigns heavily relied on aspects of the conflict as topical lure content to engage the targets and often used compromised accounts belonging to government organisations to send phishing emails,” they said.
In one such campaign, Belarussian threat actor TA473, or Winter Vivern, impersonated a European Council president spokesperson relaying a statement on the European Union’s (EU’s) position on human rights, regional security and Iran’s alleged weapons of mass destruction.
It was sent to government organisations in both Europe and the Middle East – the first time Winter Vivern has been seen targeting the Middle East – and contained an HTML file which, if opened, displayed a decoy image while conducting an HTTP request in the background. However, said Proofpoint, for now at least, this request is likely intended for target tracking purposes only, as it neither observed nor retrieved any next-stage payloads.
At the same time, the China-linked UNK_InnerAmbush actor ran a phishing exercise targeting diplomats and government officials in the region. Using a compromised email address, it used the death of Ayatollah Khamenei as a lure, purporting to share “secret on-site images” obtained via the US Department of Foreign Affairs – which should be a dead giveaway to anybody with knowledge of American politics, as US foreign affairs are handled by the State Department.
Images of strikes
Days later, UNK_InnerAmbush pivoted to images of Israel’s strikes on Iran’s fossil fuel infrastructure, which have induced a major ecological disaster – but in all instances, the images were actually disguised Microsoft Shortcut (LNK) files, hosted in a password-protected ZIP or RAR archive on Google Drive. If opened, they ran executables that decrypted Cobalt Strike command and control (C2) payloads and loaded them into memory.
Meanwhile, despite their government’s non-involvement, Pakistan-aligned threat actor UNK_RobotDreams has been targeting the offices of Middle Eastern government organisations in neighbouring India, impersonating India’s Ministry of External Affairs – which is at least the correct terminology – with phishing emails purporting to advise on the security impacts of the war.
These emails contained a blurred decoy PDF attachment and a fake Adobe Reader button which, if opened, redirected to a threat actor-controlled URL that used geofencing to serve a tainted executable to its intended targets. The executable functioned as a .NET loader that retrieved a Rust backdoor from the threat actor’s C2 host via PowerShell.
“While several of these groups incorporated the war-themed lure content in operations that are largely consistent with typical targeting remits, others demonstrated a shift toward intelligence collection against Middle Eastern government and diplomatic entities,” wrote Proofpoint’s research team.
“This likely reflects an effort to gather regional intelligence on the standing, trajectory and broader geopolitical implications of the conflict. This suggests the conflict is being used both as a topical social engineering pretext and a driver of collection priorities for a range of state-aligned threat actors.”
Iran’s state APTs stirring
In contrast to the opening days of the war, during which they appeared to be lying low, leaving the virtual battlefield largely to hacktivists, Iran’s own network of state-linked threat actors is now beginning to make itself known.
Proofpoint said it had now observed TA453, or Charming Kitten, conducting phishing exercises against a US-based think tank, with its lures themed around a roundtable on air defence capabilities – although strictly speaking, this activity began before the outbreak of war.
Other Iranian threat actors, notably the Ministry of Intelligence and Security (MoIS)-linked Seedworm (aka MuddyWater, Static Kitten), have been targeting US airports, banks, non-profits and tech companies, according to intelligence from Cisco Talos.
While, as with Charming Kitten, much of this activity began in February, Cisco Talos noted the use of a previously unknown custom backdoor, dubbed Dindoor, which uses Deno – an open source JavaScript runtime – to execute.
Dindoor was first highlighted by Symantec and Carbon Black last week, and was linked to Seedworm by the use of certificates issued to aliases linked to other Seedworm malwares.
Brigid O’Gorman, senior intelligence analyst at the Symantec and Carbon Black Threat Hunter team, told our sister title, Cybersecurity Dive, that while this particular Seedworm campaign began before the current conflict, it puts the gang in a “potentially dangerous” position to be able to launch further attacks.
-

 Sports5 days ago
Sports5 days agoPakistan set for FIH Pro League debut | The Express Tribune
-

 Politics4 days ago
Politics4 days agoIndia let Iran warship dock the day US sank another off Sri Lanka, say officials
-

 Business4 days ago
Business4 days agoRestaurant group changes name after bid to buys pubs across the UK
-

 Entertainment4 days ago
Entertainment4 days agoHarry Styles kicks off new era with ‘One Night Only’ comeback show
-

 Business5 days ago
Business5 days agoHome heating oil: ‘Most of my pension has gone on home heating oil’
-

 Sports5 days ago
Sports5 days agoWinners and losers of the 2026 NHL trade deadline
-

 Entertainment5 days ago
Entertainment5 days agoKanye ‘Ye’ West trips during trial: ‘Is he asleep?’
-

 Tech1 week ago
Tech1 week agoGoogle’s Pixel 10a May Not Be Exciting, but It’s Still an Unbeatable Value





