

Google notes that Apple patched vulnerabilities used by Coruna in the latest versions of its mobile operating system, iOS 26, so its exploitation techniques are only...
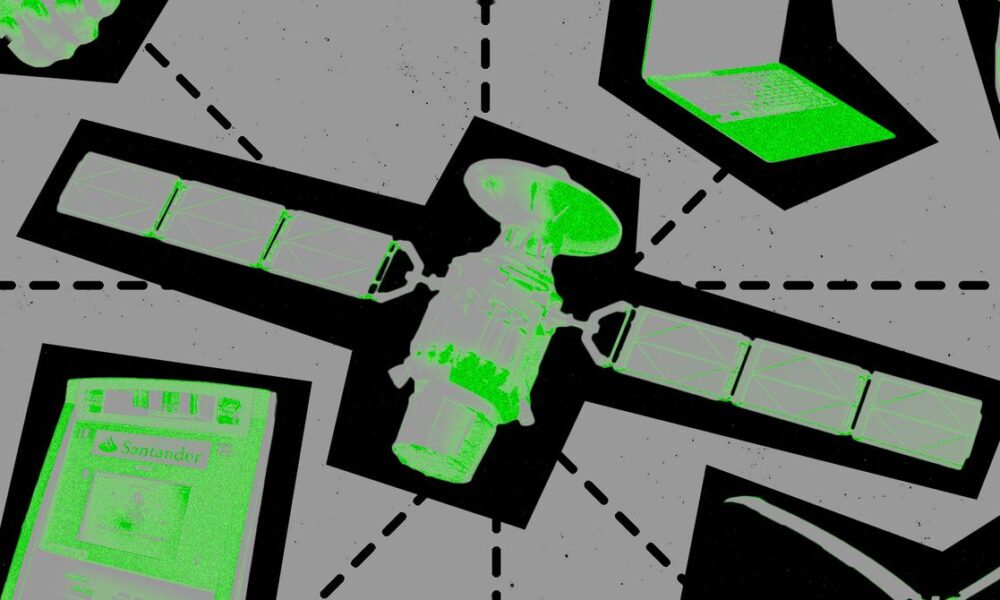

That suggests anyone could set up similar hardware somewhere else in the world and likely obtain their own collection of sensitive information. After all, the researchers...









































































