Tech
What is driving the rise of infostealer malware? | Computer Weekly

Cyber criminals would much rather log in than hack in. That’s why infostealer malware, designed to exfiltrate user credentials, browser data, messages, documents, images, and device information, is becoming more widespread. Stealing sensitive information opens a lot of doors for cyber criminals. They can log in using the stolen credentials and bypass multi-factor authentication with hijacked session cookies. They can take over accounts, commit fraud, craft better phishing campaigns, or simply sell the data to the highest bidder on the dark web.
Infostealer malware is a growing problem for cyber security teams, and our data tells us that attacks have the potential to cause significant damage to businesses. That is because lax security policies are creating the perfect conditions for infostealer attacks to thrive.
The scale of the problem
Socura and Flare recently analysed the digital footprint of the UK’s biggest companies, looking for stolen credentials across the clear and dark web. In total, we discovered 28,000 instances of stolen FTSE 100 employee credentials that had been leaked in infostealer logs. We also found cookies that were valid for several years, giving attackers another way to log in and bypass security controls like MFA.
Ideally, the UK’s corporate giants would be immune to these threats. After all, they have the budgets and the tools to be the most secure. Yet, despite their resources, they remain vulnerable. This raises a critical point: if the industry leaders are struggling to manage their threat exposure, then small and medium-sized businesses must face similar challenges.
Contributing factors
One of the major reasons that infostealer malware has been allowed to flourish is the blurred (almost invisible) line between corporate and personal IT. Employees are using their work devices, accounts, and applications at home and for personal use. They are using their personal devices for work tasks, too.
A surprisingly common source of infostealer malware is video games, specifically infected mods for popular games like Roblox, Fortnite and Grand Theft Auto. If you have an employee using a device to check their work emails and access sensitive documents, while also using the device for gaming (themselves or a family member), that poses a significant risk.
The threat of infostealer malware is being made even worse because employees continue to use the same weak passwords across all their accounts. Our research showed that more than half of FTSE 100 companies had at least one instance of an employee credential where the password was simply ‘password’. Likewise, these weak passwords or slight variations are often recycled across services used for business and personal purposes. If malware captures a login for one site, criminals will often test that password elsewhere, potentially unlocking a treasure trove of additional data they can use to further their objectives.
Recommended actions
To protect against the risks of infostealer malware, it is beneficial to take a multi-layered approach. This means looking at ways to prevent leaks, while also ensuring the business is resilient if leaks do occur, which they inevitably will at some point.
Following NCSC guidance is a great starting point. This might include employee education on password hygiene and the rollout of password managers. We also suggest implementing multi-factor authentication across the board, ideally using phishing-resistant options like passkeys to avoid sophisticated attacks.
It is also worth reviewing how personal devices and applications are managed, as these are common entry points for malware. Updating BYOD policies and implementing conditional access policies, to block users from accessing corporate resources based on factors such as device compliance and risk level, are also recommended.
Finally, proactive threat exposure monitoring allows businesses to spot leaked credentials on the dark web before they are exploited. We suggest implementing controls to flag unusual activity and automating response actions, such as initiating password resets and isolating machines, as soon as risks are identified.
Final thoughts
The threat of leaked credentials and infostealer malware might seem daunting, but there are definitive actions businesses can take to minimise the risk. This starts with acknowledging just how widespread this threat has become.
Cyber criminals would rather log in than hack in. Let’s make sure we stop handing them the keys and making their job as simple as turning a lock.
Anne Heim is threat intelligence lead at Socura, a provider of managed detection and response (MDR) services.
Tech
Some Women Are Obsessively Testing Their Vaginas to Optimize Them
Farrah was fed up with her vagina.
For the past two years, the 29-year-old dancer from Ohio had been dealing with severe pelvic pain and vaginal odor. “It was like 8/10, horrible core pain,” she says. “I couldn’t lie down. I couldn’t even work an office job. It was bad.”
When she visited doctors, she told them what she thought the culprit was: an allergic reaction to soy oil in a vat of water she’d swam in during a pirate-themed dinner theater performance. But they didn’t believe her. “They attempted to fix it with antibiotics,” she says. “And they just did nothing.”
So Farrah (who requested we withhold her full name to speak freely about health matters) started Googling her symptoms. That’s how she stumbled on Neueve, a vaginal health company that provides supplements, suppositories, and at-home vaginal microbiome testing kits.
She ordered a test from the company for $150, and it came back with a diagnosis: aerobic vaginitis (AV), a bacterial infection caused by an overgrowth of E. coli or streptococcus. She ordered supplements the company recommended, and she says the pain abated almost immediately. “I was just so glad to actually know what was wrong,” she says.
Farrah is one of a growing number of women who have used at-home tests to self-diagnose issues with the vaginal microbiome—an ecosystem of bacteria growing inside the vagina; the presence of “good” bacteria correlates with lower risk of STIs and other types of infections, according to numerous studies. The industry got a shoutout when the Silicon Valley entrepreneur Bryan Johnson recently posted on X that he had just given oral sex to his girlfriend, Kate Tolo, then followed up with a screengrab of her TinyHealth vaginal microbiome report. He proclaimed that she scored “100/100” and that hers was in the “top 1% of all vaginas” due to the dominance of Lactobacillus crispatus, a type of “good” bacteria found in the vagina.
Johnson’s thread garnered widespread mockery, with many questioning why Johnson would publicly quantify his partner’s vaginal health in such a fashion. But it also received replies from women online who are tracking their own vaginal microbiomes to treat their bacterial infections, to boost fertility, or just out of interest. Some even posted their results.
The market for at-home vaginal microbiome tests is growing—TinyHealth, the startup Tolo used, claims vaginal health testing sales spiked 2,000 percent within the first 48 hours of Johnson’s post—and similar companies include Juno Bio, which partners with Neueve; the UK-based Daye, and Evvy. But some experts believe there’s not yet enough research to support the long-term validity of such tests. None of the at-home kits on the market are approved by the FDA. There are also questions as to whether they empower women to take their health care into their own hands or simply create more anxiety for them.
Twenty-eight-year-old Samantha (she also requested a pseudonym given the sensitive nature of this topic) developed an interest in vaginal microbiome testing after experiencing a bout of bacterial vaginosis, or BV. She ordered a testing kit from Evvy upon the recommendation of the Facebook group Beyond BV, which offers support for women with recurring vaginal infections, and where they often post their own results.
Samantha found her test results useful, but she also noticed a distinct strain of paranoia within the group. For instance, when many women receive their results, they tend to focus on whether they have enough Lactobacillus crispatus, or “good” bacteria, in the vagina. “I’ll read posts where women are freaking out if they have like 97 percent crispatus and then they’ll retest and they’ll have like 60 percent and be really disappointed and scared,” she says. The opposite also holds true. “Women will post about having 100 percent crispatus and other women in the comments will just be like, ‘Oh, I’m so jealous, I’m having so many issues, I hope to be you one day.’”
Tech
These Discounted Pool-Cleaning Robots Free Up Time for Actually Swimming
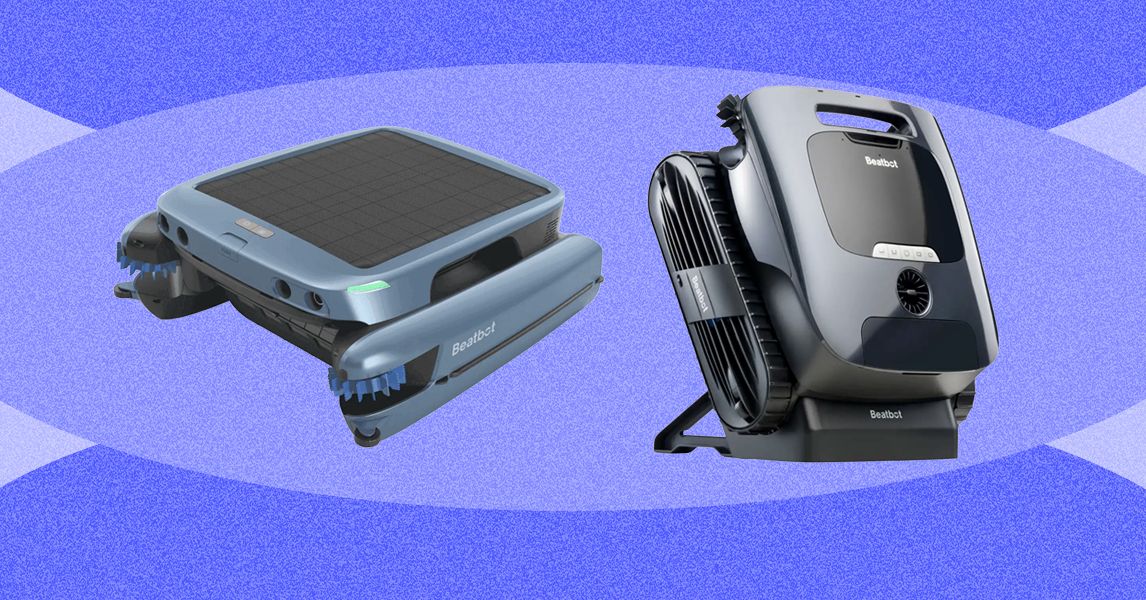
Just in time for summer, Beatbot’s pool-cleaning robots are on sale through the end of the month. If you’re on the hunt for smarter pool care, these are some of the best pool-cleaning robots on the market, and we haven’t seen them sell for less. Whether you’re tired of paying the pool guy or just don’t want to deal with whatever scary stuff is floating in the water, these robots can help.
Be sure to check out our related buying guides for more summer outdoors coverage, including the best bug sprays, the best sunscreens, and the best fitness trackers.
Beatbot iSkim Ultra Robotic Pool Skimmer for $599 ($400 off)
This surface skimmer is slow and methodical with its approach, which means it won’t slam into your pool’s walls while doing its job. Use the app to set schedules, monitor the temperature, dock the unit, adjust its speed, and more. It has a 9-liter basket that holds a ton of crud and features both solar and magnetic wireless charging. If you care mostly about surface cleaning, this deal is solid.
Beatbot Sora 30 for $699 ($300 off)
The middle-of-the-line Beatbot Sora 30 scrubs the walls, waterline, shallow areas, and floor of your pool for up to five hours at a time. It also returns to the surface on its own when the job is done or when its battery is low, minimizing the amount of effort you have to put in. You can retrieve it with one tap in the app, which also allows you to select a cleaning mode, monitor the bot’s progress, and more. It doesn’t have surface-skimming capabilities, but if you don’t mind handling that part manually, this is a handy device that takes care of your other pool-cleaning needs without any hassle.
Beatbot AquaSense 2 Ultra for $2,649 ($500 off)
If only the best pool-cleaning robot will do, this is the model you want. This top-shelf robot can do it all: skim the surface, scrub your floors, walls, and waterline with its five cleaning brushes, and even detect debris with AI. It can run for up to six hours at a time and will return to the surface and float when your pool is squeaky-clean (or when the battery gets low). It’s a little heavy at 29 pounds, but the trade-off is never having to manually clean your pool again.
Additional Beatbot Deals
Almost the entire Beatbot lineup is on sale. Here are a few more discounts on models that differ slightly from the versions we linked above.
Power up with unlimited access to WIRED. Get best-in-class reporting and exclusive subscriber content that’s too important to ignore. Subscribe Today.
Tech
Interview: Alwin Bakkenes, head of software engineering, Volvo Cars | Computer Weekly

Alwin Bakkenes, head of software engineering at Volvo Cars, reckons that leading a team to develop the technology stack powering the next generation of mobility at the automotive giant is one of the best jobs you can imagine.
“I’m not saying it’s always easy, but it’s incredibly rewarding and great fun,” he says. “People are passionate about our products, and you get instant feedback on the quality of what you do from consumers – whether that’s from friends, family or a community like Reddit. There’s just so much feedback, and that motivates and makes us better.”
Bakkenes reports to Volvo CTO Anders Bell and is a member of the extended executive management team that oversees operational governance. “I’m part of that group because software, of course, has a massive transformational impact on the company,” he says.
On a day-to-day basis, Bakkenes’ team works closely with technology and content partners to deliver customer experiences, with innovations in safe automation, core computing architecture and Android-based infotainment services. His team manages technology associated with Volvo’s advanced driver assistance systems (ADAS) and an in-house artificial intelligence (AI) factory.
“We also manage mobile network contracts because we operate in 85-plus countries globally,” he says. “So, we have a large scope, and our work defines a big part of how the vehicles behave and helps us to create different types of relationships with our customers.”
Connecting vehicles
Bakkenes joined Volvo in November 2022, having previously been vice-president at Aptiv, chairman of the board of directors at Smashing Ideas, and executive vice-president for automotive at Luxsoft.
One of his big achievements at Volvo has been leading the digital transformation that accompanied the unveiling of the EX60, the first car designed to launch with Google Gemini AI assistant and connectivity delivered by the Snapdragon Auto Connectivity Platform from Qualcomm Technologies.
As Computer Weekly discovered in January, the EX60 is the most intelligent Volvo and can travel 810km on a single charge. The car also has the latest iteration of HuginCore, the manufacturer’s in-house-developed core system for its software-defined vehicles (SDVs).
“Volvo Cars has always been known for safety,” says Bakkenes, referring to the journey the in-house software team has taken during its digital transformation. “Over the years, after we started to do innovations in terms of collision avoidance – because, of course, avoiding a collision is better than protecting people in a collision – we started to bring computer vision and radar into cars.”
Bakkenes says the software team learned that getting data from cars digitally would enable them to do even more. “So, we started making every single car connected and started doing more in-house development. We built an AI factory and built an in-house team of some 3,000 developers that build this software stack for us,” he says.
“One of our biggest accomplishments with the optimisation work that we did for the EX60, where we did our second-generation zonal architecture, was that we really simplified the approach. We reduced weight, a lot of packaging space, we made the technology much more efficient and made it applicable to every single car in our cycle plan.”
Digitising the stack
Bakkenes says the result of this digital transformation is that Volvo has transitioned from a mechanically oriented company to an organisation that successfully manages its technology base, with HuginCore sitting at the heart of its future automotive innovations.
“We now have a single tech stack strategy for our cars, which ultimately gives us more time to spend on building fantastic customer features and experiences,” he says. “And that’s one of the biggest parts of the journey that we’ve been on over the past few years.”
HuginCore features an electrical architecture, a core computer, zone controllers and software. The name Hugin comes from Nordic mythology – Odin had two ravens, Hugin and Munin. Bakkenes says Hugin was the raven who flew to scout and then whispered in Odin’s ear about everything in the vicinity.
“We now have a single tech stack strategy for our cars, which ultimately gives us more time to spend on building fantastic customer features and experiences”
Alwin Bakkenes, Volvo Cars
“That’s like what we are doing with the core system,” he says. “HuginCore perceives the world around it and gives us the right information to make decisions on avoiding collisions and more. It’s the core system and tech stack that we’re standardising on. And, of course, it’s much more than a piece of compute. It’s vehicle architecture, cloud infrastructure and factory infrastructure.”
Beginning with the EX60 implementation, Bakkenes says the aim is to ensure the company builds its innovations around this stack, rather than using multiple platforms. “Which is ultimately not how modern tech companies, like Apple, would do things,” he says, referring to the company’s shift to becoming a company that manages its technology foundation.
“For example, we have a partnership with a UK company called Brief that is really good at database analytics on battery cells and how you store energy as fast as possible. So, not only do we have a good, robust 800-volt system, we’re able to push a lot of energy into the cells for a prolonged period of time, meaning that we avoid the standard curves of charging cars.”
Delivering innovation
The progress made by Bakkenes and his team was recognised recently, with Volvo achieving S&P Global Mobility Level 5 capability in SDVs, the highest category in its assessment of automotive software maturity. Notably, Volvo is the only legacy manufacturer to have achieved this rating.
“They looked at what we were doing,” says Bakkenes, referring to the evaluation process. “We explained to them how we work and what the architecture looks like. Having a fully software-defined architecture means we should create significant customer benefits. So, we’re proud. It’s recognition that we’re doing good work.”
The recognition from S&P Global highlights Volvo’s attempts to improve vehicle functionality through software, including over-the-air updates to add safety features, unlock faster charging speeds, increase driving range and enhance user experiences. Bakkenes says the company’s digitisation is all about leaving behind traditional domain-based architectures.
The new approach being pioneered by Volvo focuses on three levels: a high-performance compute cluster where the team works with key partners, such as Nvidia and Qualcomm; zonal architecture with high-integrity applications that require low latency and fast response times, such as for safety-critical functions, including brakes and acceleration; and infotainment, where Volvo works closely with Google and its Android operating system (OS).
“We work very heavily with partners to build the foundations for that strategy. We work with Nvidia on developing the safety-critical, high-performance execution environment, so we can execute high-integrity applications on compute clusters, such as ADAS,” he says.
“We also work with Google deeply and closely, because the Android platform creates an openness and an ecosystem that is a fantastic foundation to build a modern infotainment system, which has customer-facing functionality, such as Gemini for conversational AI and Google Maps, and an open app store that we use to bring in massive amounts of content.”
Embracing AI
Volvo continues to hone its approach to SDVs. As Computer Weekly reported at the time, the company extended its partnership with Google in May 2025. Volvo believes that with Gemini in the car, drivers can better understand what they want through natural conversations.
As well as using AI services to boost internal operational efficiency, Bakkenes says the company uses emerging technology in two key product areas.
First, in collision-avoidance systems. With a strong heritage in vehicle safety, Volvo has collected millions of data points since 2020, all with customer consent, to improve ADAS.
“We’ve seen that building AI models that we train on what happens and what will go wrong – thereby preventig things from happening – is incredibly valuable,” he says. “So, we literally built a company, a subsidiary called Zenseact, which is part of my scope. I’m the chairman of the company, and it’s deeply integrated into our way of working in engineering.”
Second, Bakkenes says his team is focused on customer-oriented, AI-enabled products. Using tools such as Gemini, drivers will use in-car systems to plan routes, help schedule activities and organise their lives. “AI is not just about telling you things,” he says. “It’s about becoming more agentic and taking care of tasks in your life.”
While Volvo has made significant advances in AI with the launch of the EX60, the company is eager to ensure that drivers of older vehicles can also benefit from its data-powered services. To that end, the company recently announced that Google Gemini is rolling out to Volvo vehicles dating back more than five years. Bakkenes suggests this decision is a step change in how drivers interact with cars and how manufacturers support them.
“We’re bringing Gemini to every car we’ve produced since 2020,” he says. “Six years ago, we had no idea what a transformer-based conversational assistant was or would become. So, the fact that we can bring Gemini to those cars is fantastic.”
Scaling improvements
Bakkenes reflects on the digital transformation changes he’s overseen during the past few years and suggests his team is approaching what he calls “harvest time”.
“We now have a foundation where we have a good architecture,” he says. “We have a large amount of high-performance computing to grow and develop in the future. The foundation of the technology is there, and it’s about applying and scaling it.”
Bakkenes says the desire to push Gemini-powered services to older vehicles shows that his team’s efforts aren’t just focused on tomorrow’s technology – they’re also focused on supporting long-standing customers who have committed money to the car company.
“The harvesting part is about us saying, ‘OK, so now we can put more energy into enhancing the experiences’, and that means refining the user interface implementation, and tweaking and optimising it until you get a product that fits day-to-day usage perfectly,” he says. “We want our cars to keep improving over time.”
-

 Politics1 week ago
Politics1 week agoIran weighs US reply delivered via Pakistan as Trump signals opposition to deal terms
-
 Tech1 week ago
Tech1 week agoDHS Demanded Google Surrender Data on Canadian’s Activity, Location Over Anti-ICE Posts
-

 Business1 week ago
Business1 week agoHeineken to invest £44.5m in hundreds of pubs creating 850 jobs
-

 Entertainment1 week ago
Entertainment1 week agoJelly Roll reacts to daughter Bailee Ann’s major life milestone
-

 Business1 week ago
Business1 week agoHeineken plans huge investment in hundreds of UK pubs ahead of World Cup
-

 Tech4 days ago
Tech4 days agoA new frontier: Identity stack evolves for agentic systems | Computer Weekly
-

 Tech4 days ago
Tech4 days ago‘Orbs,’ ‘Saucers,’ and ‘Flashes’ on the Moon: Pentagon Drops New UFO Files
-

 Entertainment1 week ago
Entertainment1 week agoPassage: In memoriam










