Tech
Contrastive learning framework can detect blockchain-based smart Ponzi schemes
Blockchain technologies are digital systems that work by distributing copies of information across several computers, also referred to as nodes, all of which are connected to a common network. These technologies underpin the trading of cryptocurrencies, as well as the functioning of other emerging digital services.
While blockchain technology opens new opportunities for the trading of cryptocurrencies, digital arts and other digital assets, they are also often used for fraudulent activities. Perhaps most notably, they are now widely used for fraudulent investment schemes known as smart Ponzi schemes.
In a smart Ponzi scheme, individuals are asked to invest in specific digital currencies or assets and sign a so-called smart contract that automatically draws money from them on a regular basis. Their investments might initially seem fruitful, yet the early investors are in fact being paid with the money invested by new individuals. After some time, the whole system collapses, as there are no longer enough resources to pay all investors.
In recent years, computer scientists and financial security experts have been trying to devise strategies to automatically detect these fraudulent schemes. Most solutions developed so far rely on deep learning algorithms trained to identify patterns associated with smart Ponzi schemes in blockchain transactions.
Despite their promise, to perform well, these deep learning-based techniques must be trained on large datasets containing blockchain transactions labeled by human experts. As labeling this data requires extensive time and resources, existing solutions might not be ideal for the reliable detection of smart Ponzi schemes in real-world settings.
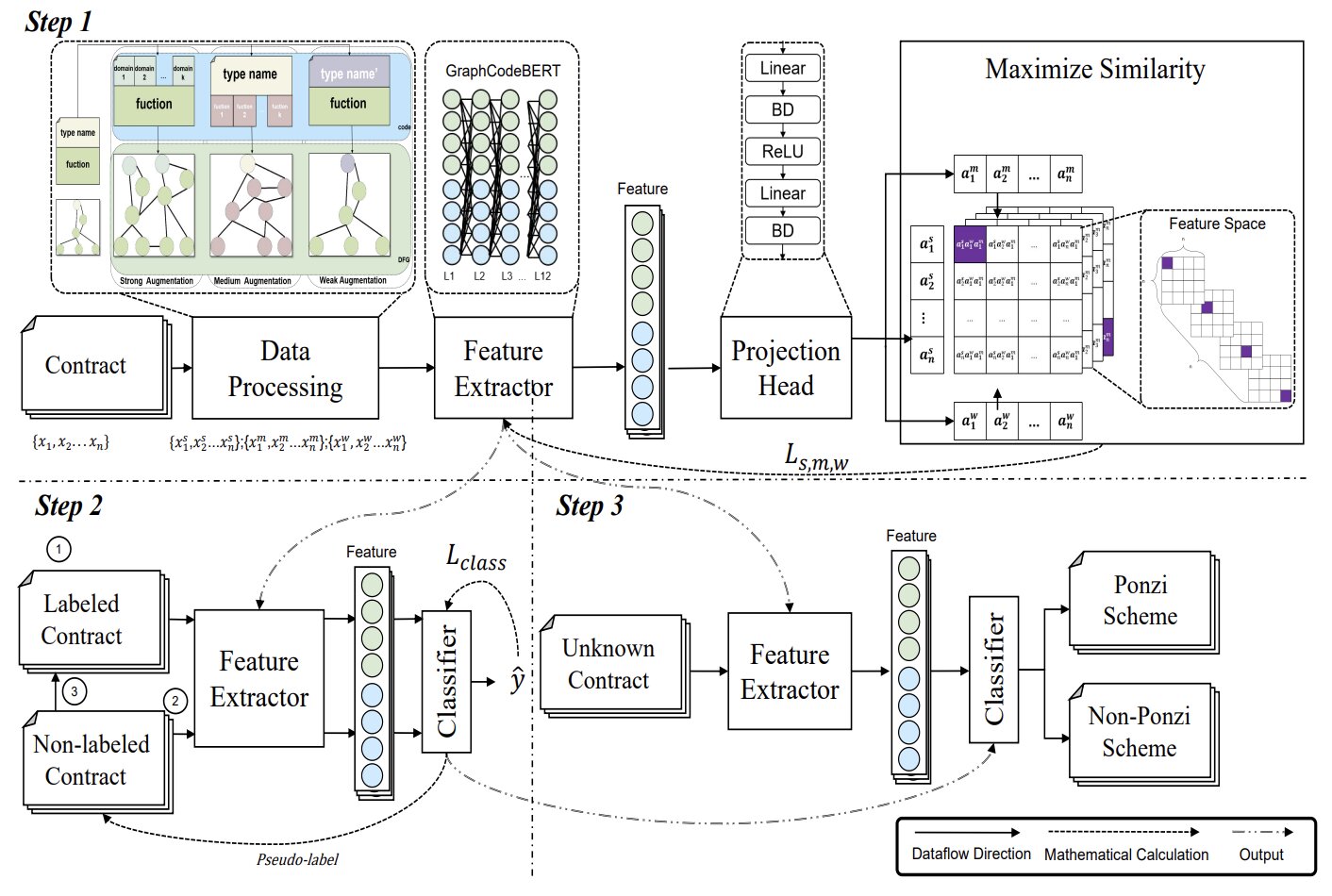
The University of Electronic Science and Technology of China, City University of Macau and Swinburne University of Technology recently developed CASPER (Contrastive Approach for Smart Ponzi detectER), a deep-learning-based framework that can detect smart Ponzi schemes with good accuracy without requiring labeled training data.
This new technique, introduced in a paper published on the arXiv preprint server, relies on models that can learn to detect these fraudulent activities by comparing the similarities and differences between different blockchain transactions.
“Traditional Ponzi scheme detection methods based on deep learning typically rely on fully supervised models, which require large amounts of labeled data,” wrote Weija Yang, Tian Lan and their colleagues in their paper. “However, such data is often scarce, hindering effective model training. To address this challenge, we propose a novel contrastive learning framework, CASPER (Contrastive Approach for Smart Ponzi detectER with more negative samples), designed to enhance smart Ponzi scheme detection in blockchain transactions.”
To pick up signs of smart Ponzi schemes in blockchain transactions, Yang, Lan and their colleagues employed an approach known as contrastive learning. This is a machine learning technique through which a computational model learns to tell different things apart by comparing them.
“By leveraging contrastive learning techniques, CASPER can learn more effective representations of smart contract source code using unlabeled datasets, significantly reducing both operational costs and system complexity,” wrote the researchers.
The team assessed the new Ponzi scheme detection technique in a series of tests, in which it was fed blockchain transactions from a publicly available dataset. Their framework performed remarkably well, despite being trained on a limited amount of labeled data.
“We evaluate CASPER on the XBlock dataset, where it outperforms the baseline by 2.3% in F1 score when trained with 100% labeled data,” the team wrote. “More impressively, with only 25% labeled data, CASPER achieves an F1 score nearly 20% higher than the baseline under identical experimental conditions. These results highlight CASPER’s potential for effective and cost-efficient detection of smart Ponzi schemes, paving the way for scalable fraud detection solutions in the future.”
In the future, the CASPER framework could be improved and tested on more real-world data, to further assess its potential for detecting and mitigating smart Ponzi schemes. Eventually, it could make its way into real-world settings, where it could help to protect digital currency investors against malicious activities.
Written for you by our author Ingrid Fadelli,
edited by Stephanie Baum, and fact-checked and reviewed by Robert Egan—this article is the result of careful human work. We rely on readers like you to keep independent science journalism alive.
If this reporting matters to you,
please consider a donation (especially monthly).
You’ll get an ad-free account as a thank-you.
More information:
Weijia Yang et al, CASPER: Contrastive Approach for Smart Ponzi Scheme Detecter with More Negative Samples, arXiv (2025). DOI: 10.48550/arxiv.2507.16840
© 2025 Science X Network
Citation:
Contrastive learning framework can detect blockchain-based smart Ponzi schemes (2025, August 24)
retrieved 24 August 2025
from https://techxplore.com/news/2025-08-contrastive-framework-blockchain-based-smart.html
This document is subject to copyright. Apart from any fair dealing for the purpose of private study or research, no
part may be reproduced without the written permission. The content is provided for information purposes only.
Tech
Dark Matter May Be Made of Black Holes From Another Universe

A recent cosmological model combines two of the most eccentric ideas in contemporary physics to explain the nature of dark matter, the invisible substance that makes up about 85 percent of all matter in the universe. To understand it, it’s necessary to look beyond the Big Bang we all know and consider two concepts that rarely intersect: cyclic universes and primordial black holes.
A Different Kind of Multiverse
There are different versions of the “multiverse.” The most popular model—that of the Marvel Cinematic Universe—proposes that there are as many universes as there are possibilities and that these versions of reality are parallel. Physics proposes something more sober and mathematically consistent: the cosmic bounce.
In this model, the universe is not born from a singularity, but expands, contracts, and expands again in an endless cycle. Each “universe” is not parallel, but sequential—that is, one arises from the ashes of the previous one.
Is it possible for something to survive the end of its universe and endure into the next? According to a paper published in Physical Review D, yes. Author Enrique Gaztanaga, a research professor at the Institute of Space Sciences in Barcelona, shows that any structure larger than about 90 meters could pass through the final collapse of a universe and survive the rebound. These “relics” would not only persist, but could also seed the formation of giant, unexplained structures observed in the early stages of the present-day universe. Moreover, they could be the key to understanding dark matter.
For decades, the dominant explanation for dark matter has been that it is an unknown particle or particles. But after years of experiments without direct detections, physicists have begun to explore alternatives. One of them proposes that dark matter is not an exotic particle, but an abundant population of small black holes that we overlook.
The idea is appealing, but it has a serious problem. For these black holes to explain dark matter, they would have to exist from the earliest moments of the universe, long before the first stars could collapse. There are indications that these objects could exist, but a convincing physical mechanism to explain their origin is lacking.
A Universe Born With Black Holes
This is where Gaztanaga’s newly proposed model shines. If cosmic bouncing allows compact structures to survive the collapse of the previous universe, then the current universe would have already been born with pre-existing black holes. They would not have to have been generated by extreme fluctuations or finely tuned inflationary processes, but would simply have been there from the first instant.
The assumption has the potential to solve two riddles at once: the origin of black holes and the nature of dark matter. If this model is correct, dark matter would not be a mystery of the early universe but rather a legacy of a cosmos that predates our own.
“Much work remains to be done,” Gaztanaga, also a researcher at the Institute of Cosmology and Gravitation at the University of Portsmouth, said in an article for The Conversation. “These ideas must be tested against data—from gravitational-wave backgrounds to galaxy surveys and precision measurements of the cosmic microwave background.”
“But the possibility is profound,” he added. “The universe may not have begun once, but may have rebounded. And the dark structures shaping galaxies today could be relics from a time before the Big Bang.”
This story originally appeared in WIRED en Español and has been translated from Spanish.
Tech
Europe’s Online Age Verification App Is Here

The European online age verification app is ready.
The app works with passports or ID cards, is built to be “completely anonymous” for the people who use it, works on any device (smartphones, tablets, and PCs), and is open source. “Best of all, online platforms can easily rely on our age verification app, so there are no more excuses,” said European Commission president Ursula von der Leyen at a press conference on Wednesday. “Europe offers a free and easy-to-use solution that can protect our children from harmful and illegal content.”
High Expectations
“It is our duty to protect our children in the online world just as we do in the offline world. And to do that effectively, we need a harmonized European approach,” von der Leyen said at Wednesday’s press conference. “And one of the central issues is the question, how can we ensure a technical solution for age verification that is valid throughout Europe? Today, I can announce that we have the answer.”
This answer takes the form of an open source app that any private company can repurpose, as long as it complies with European privacy standards and offers the same technical solution throughout the European Union. The user downloads the app, agrees to the terms and conditions, sets up a pin or biometric access, and proves their age through an electronic identification system, or by showing a passport or ID card (in which case biometric verification is also provided). The app does not store your name, date of birth, ID number, or any other personal information, according to the European Commission—only the fact that you are over a certain age.
After that, when a person using the app wants to access a social network (minimum age: 13), pornographic site (minimum age: 18), or any other age-protected content, if they are logged in from a computer, they need only scan the QR code shown on the site they want to visit. If, on the other hand, the person logs in from a smartphone, the app sends the proof of age directly. The platform does not access the document with which the user proved it in the first place.
Adoption Event
The need to introduce a common system for the entire European Union has been discussed for some time, and according to commission technicians, the technical work is now complete. Of course, it will still be possible to circumvent the system—all it takes is for an adult to lend their phone to a younger friend—but the technological architecture exists, and it will be up to EU member states to decide whether to integrate it into national digital wallets or develop independent apps.
“No More Excuses”
For the app to really be effective, platforms must be obligated to verify the age of their users—that’s where things get tricky. The Digital Services Act, which went into effect in 2024, requires “very large online platforms”—those with more than 45 million monthly users in the European Union—to take concrete steps to mitigate systemic risks related to child protection, with heavy penalties for noncompliance.
“And that’s why Europe has the DSA: to call online platforms to their responsibilities. Because Europe will not tolerate platforms making money at the expense of our children,” European Commission executive vice president Henna Virkkunen told a press conference. She added that after an investigation into TikTok, the European institutions plan to take similar action against Facebook, Instagram, and Snapchat, as well as four porn sites. “Since the platforms do not have adequate age verification tools, we developed the solution ourselves,” he concluded. In short, as von der Leyen also remarked, “there are no more excuses.”
Bare Minimum
So far, this is the European framework that sets the general rules. On this basis, member states can consider more restrictive measures. Italy was among the first to discuss how to regulate the use of social media by minors but has so far not landed on anything concrete. Elsewhere in the EU, France’s Emmanuel Macron has been a trailblazer on the issue, pushing France to discuss a rule to ban social networks for minors under the age of 15 entirely. So far, this measure has received broad political support—but the outcome depends largely on compatibility with the Digital Services Act and the availability of effective age verification systems like the app the European Commission just released.
This article originally appeared on WIRED Italia and has been translated.
Tech
Anthropic Plots Major London Expansion

Anthropic is moving into a new London office as it seeks to expand its research and commercial footprint in Europe, setting up a scrap between the leading AI labs for talent emerging from British universities.
The company, which opened its first London office in 2023, is moving to the same neighborhood as Google DeepMind, OpenAI, Meta, Wayve, Isomorphic Labs, Synthesia, and various AI research institutions.
Anthropic’s new, 158,000-square-foot office footprint will have space enough for 800 people—four times its current head count—giving it room to potentially outscale OpenAI, which itself recently announced an expansion in London.
“Europe’s largest businesses and fastest-growing startups are choosing Claude, and we’re scaling to match,” says Pip White, head of EMEA North at Anthropic. “The UK combines ambitious enterprises and institutions that understand what’s at stake with AI safety with an exceptional pool of AI talent—we want to be where all of that comes together.
UK government officials had reportedly attempted to coax Anthropic into expanding its presence in London after the company recently fell out with the US administration. Anthropic refused to allow its models to be used in mass surveillance and autonomous weapon systems, leading to an ongoing legal battle between the AI lab and the Pentagon.
As part of the expansion, Anthropic says it will deepen its work with the UK’s AI Security Institute, a government body that this week published a risk evaluation of its latest model, Claude Mythos Preview. According to Politico, the UK government is one of few across Europe to have been granted access to the model, which Anthropic has released to only select parties, citing concerns over the potential for its abuse by cybercriminals.
The increasing concentration of AI companies in the same London district is an important step in creating a pathway for research to translate into AI products, says Geraint Rees, vice-provost at University College London, whose campus is around the corner from Anthropic’s new office.
“This cluster didn’t emerge from a planning document. It grew because serious researchers and companies understand that proximity isn’t a nice-to-have,” he said last month, speaking at an event attended by WIRED. “That’s how the innovation system actually works. It’s not a clean, linear transfer from lab to market. It’s messier, richer, more human than that.”
-

 Entertainment1 week ago
Entertainment1 week agoQueen Elizabeth II emotional message for Archie, Lilibet sparks speculation
-

 Tech1 week ago
Tech1 week agoAzure customers up in arms over ‘full’ UK South region | Computer Weekly
-

 Tech1 week ago
Tech1 week agoAs the Strait of Hormuz Reopens, Global Shipping Will Take Months to Recover
-

 Fashion1 week ago
Fashion1 week agoCII submits 20-pt agenda to Indian govt to back firms hit by Iran war
-

 Tech1 week ago
Tech1 week agoThis AI Button Wearable From Ex-Apple Engineers Looks Like an iPod Shuffle
-

 Politics7 days ago
Politics7 days agoIndian airlines hit hardest after Dubai limits foreign flights until May 31
-

 Entertainment4 days ago
Entertainment4 days agoPalace left in shock as Prince William cancels grand ceremony
-

 Politics7 days ago
Politics7 days agoChinese, Taiwanese will unite, Xi tells Taiwan opposition leader