Tech
Wristband enables wearers to control a robotic hand with their own movements
The next time you’re scrolling your phone, take a moment to appreciate the feat: The seemingly mundane act is possible thanks to the coordination of 34 muscles, 27 joints, and over 100 tendons and ligaments in your hand. Indeed, our hands are the most nimble parts of our bodies. Mimicking their many nuanced gestures has been a longstanding challenge in robotics and virtual reality.
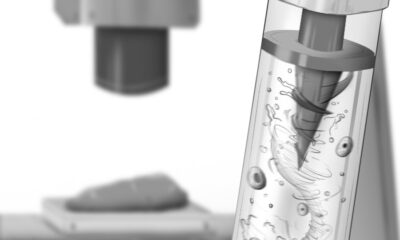
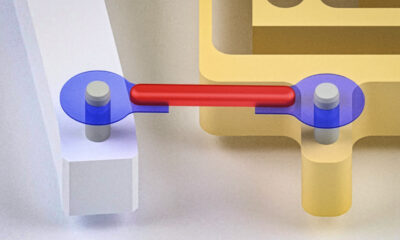
Now, MIT engineers have designed an ultrasound wristband that precisely tracks a wearer’s hand movements in real-time. The wristband produces ultrasound images of the wrist’s muscles, tendons, and ligaments as the hand moves, and is paired with an artificial intelligence algorithm that continuously translates the images into the corresponding positions of the five fingers and palm.
The researchers can train the wristband to learn a wearer’s hand motions, which the device can communicate in real-time to a robot or a virtual environment.
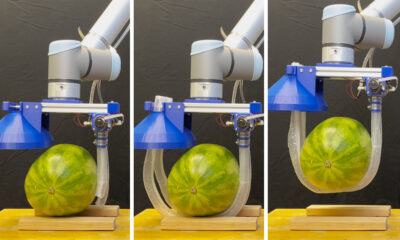
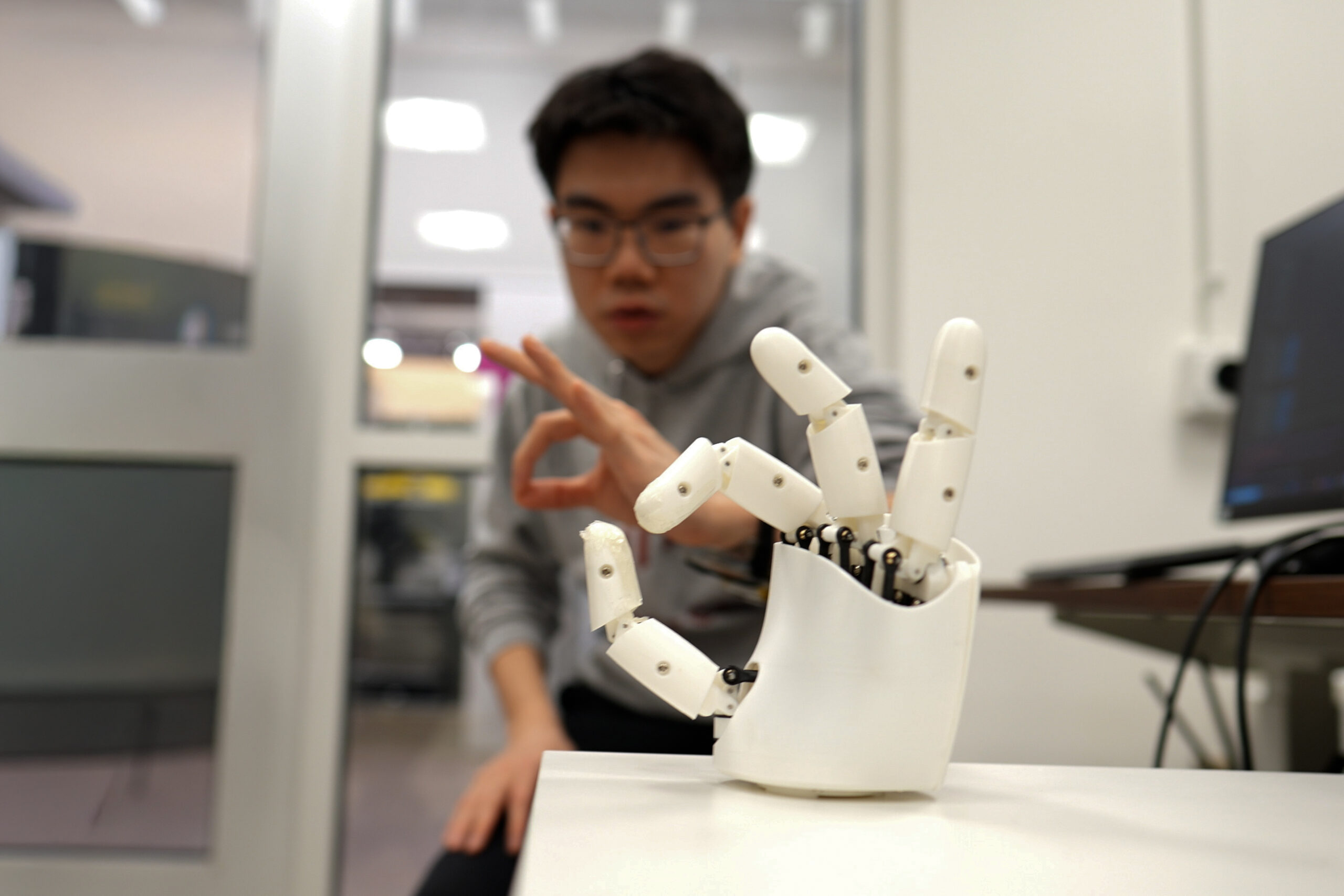
In demonstrations, the team has shown that a person wearing the wristband can wirelessly control a robotic hand. As the person gestures or points, the robot does the same. In a sort of wireless marionette interaction, the wearer can manipulate the robot to play a simple tune on the piano and shoot a small basketball into a desktop hoop. With the same wristband, a wearer can also manipulate objects on a computer screen, for instance pinching their fingers together to enlarge and minimize a virtual object.
The team is using the wristband to gather hand motion data from many more users with different hand sizes, finger shapes, and gestures. They envision building a large dataset of hand motions that can be plumbed, for instance, to train humanoid robots in dexterity tasks, such as performing certain surgical procedures. The ultrasound band could also be used to grasp, manipulate, and interact with objects in video games, design applications, or other virtual settings.
“We think this work has immediate impact in potentially replacing hand tracking techniques with wearable ultrasound bands in virtual and augmented reality,” says Xuanhe Zhao, the Uncas and Helen Whitaker Professor of Mechanical Engineering at MIT. “It could also provide huge amounts of training data for dexterous humanoid robots.”
Zhao, Gengxi Lu, and their colleagues present the wristband’s new design in a paper appearing today in Nature Electronics. Their MIT co-authors are former postdocs Xiaoyu Chen, Shucong Li, and Bolei Deng; graduate students SeongHyeon Kim and Dian Li; postdocs Shu Wang and Runze Li; and Anantha Chandrakasan, MIT provost and the Vannevar Bush Professor of Electrical Engineering and Computer Science. Other co-authors are graduate students Yushun Zheng and Junhang Zhang, Baoqiang Liu, Chen Gong, and Professor Qifa Zhou from the University of Southern California.
Seeing strings
There are currently a number of approaches to capturing and mimicking human hand dexterity in robots. Some approaches use cameras to record a person’s hand movements as they manipulate objects or perform tasks. Others involve having a person wear a glove with sensors, which records the person’s hand movements and transmits the data to a receiving robot. But erecting a complex camera system for different applications is impractical and prone to visual obstacles. And sensor-laden gloves could limit a person’s natural hand motions and sensations.
A third approach uses the electrical signals from muscles in the wrist or forearm that scientists then correlate with specific hand movements. Researchers have made significant advances in this approach, however these signals are easily affected by noise in the environment. They are also not sensitive enough to distinguish subtle changes in movements. For instance, they may discern whether a thumb and index finger are pinched together or pulled apart, but not much of the in-between path.
Zhao’s team wondered whether ultrasound imaging might capture more dexterous and continuous hand movements. His group has been developing various forms of ultrasound stickers — miniaturized versions of the transducers used in doctor’s offices that are paired with hydrogel material that can safely stick to skin.
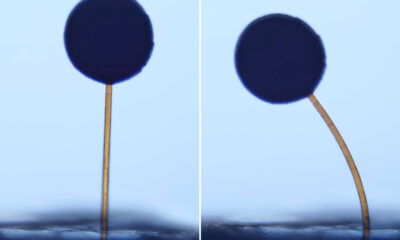
In their new study, the team incorporated the ultrasound sticker design into a wearable wristband to continuously image the muscles and tendons in the wrist.
“The tendons and muscles in your wrist are like strings pulling on puppets, which are your fingers,” Lu says. “So the idea is: Each time you take a picture of the state of the strings, you’ll know the state of the hand.”
Mapping manipulation
The team designed a wristband with an ultrasound sticker that is the size of a smartwatch, and added onboard electronics that are about as small as a cellphone. They attached the wristband to a volunteer’s wrist and confirmed that the device produced clear and continuous images of the wrist as the volunteer moved their fingers in various gestures.
The challenge then was to relate the black and white ultrasound images of the wrist to specific positions of the hand. As it turns out, the fingers and thumb are capable of 22 degrees of freedom, or different ways of extending or angling. The researchers found that they could identify specific regions in their ultrasound images of the wrist that correlate to each of these 22 degrees of freedom. For instance, changes in one region relate to thumb extension, while changes in another region correlate with movements of the index finger.
To establish these connections, a volunteer wearing the wristband would move their hand in various positions while the researchers recorded the gestures with multiple cameras surrounding the volunteer. By matching changes in certain regions of the ultrasound images with hand positions recorded by the cameras, the team could label wrist image regions with the corresponding degree of freedom in the hand. But to do this translation continuously, and in real-time, would be an impossible task for humans.
So, the team turned to artificial intelligence. They used an AI algorithm that can be trained to recognize image patterns and correlate them with specific labels and, in this case, the hand’s various degrees of freedom. The researchers trained the algorithm with ultrasound images that they meticulously labeled, annotating the image regions associated with a specific degree of freedom. They tested the algorithm on a new set of ultrasound images and found it correctly predicted the corresponding hand gestures.
Once the researchers successfully paired the AI algorithm with the wristband, they tested the device on more volunteers. For the new study, eight volunteers with different hand and wrist sizes wore the wristband while they formed various hand gestures and grasps, including making the signs for all 26 letters in American Sign Language. They also held objects such as a tennis ball, a plastic bottle, a pair of scissors, and a pencil. In each case, the wristband precisely tracked and predicted the position of the hand.
To demonstrate potential applications, the team developed a simple computer program that they wirelessly paired with the wristband. As a wearer went through the motions of pinching and grasping, the gestures corresponded to zooming in and out on an object on the computer screen, and virtually moving and manipulating it in a smooth and continuous fashion.
The researchers also tested the wristband as a wireless controller of a simple commercial robotic hand. While wearing the wristband, a volunteer went through the motions of playing a keyboard. The robot in turn mimicked the motions in real-time to play a simple tune on a piano. The same robot was also able to mimic a person’s finger taps to play a desktop basketball game.
Zhao is planning to further miniaturize the wristband’s hardware, as well as train the AI software on many more gestures and movements from volunteers with wider ranging hand sizes and shapes. Ultimately, the team is building toward a wearable hand tracker that can be worn by anyone, to wirelessly manipulate humanoid robots or virtual objects with high dexterity.
“We believe this is the most advanced way to track dexterous hand motion, through wearable imaging of the wrist,” Zhao says. “We think these wearable ultrasound bands can provide intuitive and versatile controls for virtual reality and robotic hands.”
This research was supported, in part, by MIT, the U.S. National Institutes of Health, the U.S. National Science Foundation, the U.S. Department of Defense, and Singapore National Research Foundation through the Singapore-MIT Alliance for Research and Technology.
Tech
Elon Musk Had ‘Hair-Raising’ Idea of Passing OpenAI On to His Kids, Sam Altman Says

Sam Altman took to the witness stand to defend his reputation in the Musk v. Altman trial on Tuesday, as Elon Musk’s lawyers peppered the OpenAI CEO with hours of questions regarding his alleged history of deceptive behavior.
The cross-examination was a much needed win for Musk, who has so far struggled to make a convincing case. Tuesday’s testimony included several heated exchanges in which the OpenAI CEO had to respond to allegations from former colleagues suggesting he’s untrustworthy.
Highlighting this evidence is not only important for Musk winning over a jury, but also for beating OpenAI in the court of public opinion. Days before the trial started, Musk texted OpenAI president Greg Brockman and told him that he and Altman would soon “be the most hated men in America.”
Musk’s lawsuit accuses Altman of effectively stealing the OpenAI charity, and taking the $38 million Musk donated to the nonprofit organization and using it to create a for-profit business worth more than $850 billion.
However, there was little evidence on Tuesday to address the gaps in Musk’s legal case. Altman and Sam Teller, Musk’s former chief of staff, testified on Tuesday that they did not recall Musk ever attaching any special conditions to his donations to OpenAI. Additionally, it appears increasingly likely that Musk filed his case too late, years after he made his last donation to OpenAI and developed suspicion that the organization had breached its charitable trust. By then, the statute of limitations had already expired.
Brockman and his wife, Anna, sat in the gallery alongside OpenAI’s chief futurist, Joshua Achiam. While Altman and Brockman were present to watch Musk on the witness stand, Musk did not stay for Altman’s testimony. (Flight records suggest he was traveling to the Washington, DC, area on Tuesday to fly to China with President Donald Trump.)
Before fielding questions from Musk’s lawyers, Altman had the chance to tell his side of the story, answering gentle questions from OpenAI’s lawyers. Wearing a purple tie, Altman painted himself as an entrepreneur and investor who’s always been fascinated by, and concerned about, the power of artificial intelligence.
Altman testified that Musk has long been obsessed with controlling OpenAI. He recalled “a particularly hair-raising moment” when Musk suggested that control of OpenAI should pass to his children if Musk were to die. “We didn’t feel comfortable with that,” Altman said. Altman also suggested that Musk’s attempt in 2018 to start an AI unit within Tesla—and offering him the chance to run it—felt like a “vague, lightweight threat” that Musk would effectively crush OpenAI with or without him.
Bombarding Altman
Steven Molo, Musk’s lawyer, wasted no time in his cross-examination, asking Altman: “Are you completely trustworthy?” as his first question. Altman responded that he believes so, and then Molo immediately asked whether the jury should trust the testimony he just gave. Altman responded, “That’s up to them. I’m not going to tell the jury what to think.” Here’s the heated exchange that followed, as best as WIRED could capture it:
Molo: Do you always tell the truth?
Altman: I’m sure there is some time in my life where I have not.
Molo: Do you tell lies to advance your business interests?
Altman: No.
Molo: Have you misled people with whom you do business?
Tech
IDCA datacentres report: Global concentration and the Goldilocks zone | Computer Weekly

Datacentre capacity has reached 67.7GW globally, with five countries accounting for 69% of that total, and the US alone accounting for 43%, according to the International Datacentre Authority’s (IDCA) Datacentre report 2026.
The study based its research on data from organisations such as the International Energy Agency, World Bank, United Nations and International Telecommunications Union, as well as governments, datacentre developers and operators.
It discovered that where datacentres account for 5% or more of electricity grid usage, there seemed to be a threshold at which public opposition rises significantly and governments move from incentives to regulation.
And while there was huge growth in the datacentre industry, whether a nation or region can profit optimally depended on using its resources wisely and attaining tech sector skills among 2.5% of the workforce, it found.
The US was the site for the most datacentre capacity, with 29.2GW of a global total 67.7GW. US datacentres accounted for 6% of the country’s electricity supply. Behind the US are: China, 8.5GW and 0.8% of electricity use; Germany, 5.5GW (9.5%), UK, 2GW (5.8%), and Japan, 1.7GW (1.5%). Those five states accounted for 69% of global datacentre capacity.
In the US, however, the IDCA research estimated that 13% of datacentre consumption – around 3GW – was unused but still live capacity.
China emerged as the “sleeping giant”, according to the report, because less than 1% of electricity production was devoted to datacentres, despite producing almost twice the amount of electricity as the US.
International haves and have-nots
The report concluded that 5% of electricity grid usage going to datacentres was the threshold at which public concern, government regulation and grid supply can be seen to increase. It pointed to the US, which has seen community pushback and connection difficulties in the Midwest, Texas and California, with multi-year delays in the ability to provision power new facilities.
Meanwhile, in Europe, the Netherlands, Germany, and Switzerland have exceeded the 9% consumption level, while that’s also the case for Singapore.
Also in Europe, the report found that countries with electricity grids driven by nuclear power – such as France, Slovakia and Slovenia – may relieve these constraints.
At the other end of the scale, it discovered that more than 70 countries devoted less than 0.1% of their power to datacentres, and for more than 30 countries that figure was less than 0.01%.
Datacentre energy use league table
Singapore used the highest proportion of its electricity to power datacentres at 19.5% of the total generated. Next in the IDCA report was Lithuania (11.1%), the Netherlands (9.7%), Denmark (8.4%), Ireland (8.2%), Estonia (6.9%), Luxembourg (6.3%), Germany (6.1%), Hong Kong (6%) and the US (6%). Further down the rankings are Australia (5.1%), the UK (3.6%), South Korea (2%), Japan (1.2%), and India and China (both 0.8%).
IDCA built what it described as an optimised national model of ideal consumption levels for each nation, noting that construction of new datacentres was contingent on stronger electricity grids and robust fibre-optic networks.
For developed nations, IDCA said 6.25% of national electricity consumption was an effective cap on datacentre growth – i.e., it was the point at which the correlation was very strong between datacentre consumption and political actions and community pushback that result in projects being cancelled or slowed.
Meanwhile, IDCA ranked countries by the headroom they possess to build datacentres without significantly needing to develop new electricity generation. Here, IDCA ranked countries by headroom measured in GW. China led the way with 58.9GW of headroom, followed by India (12.7GW), Russia (6.7GW), Japan (5.5GW), Brazil (4.5GW), Canada (3.6GW), South Korea (3.2GW), Saudi Arabia (2.6GW), Iran (2.4GW) and Mexico (2.4GW).
The water stress scale
IDCA pointed out that modern AI datacentres require liquid cooling but that a lot of pushback around perceived worries over water use are misguided. That’s because the latest direct-to-chip cooling systems are closed systems that recycle water somewhat similar to a car radiator.
Having said that, the IDCA report stated: “The vast majority of existing traditional cloud and enterprise facilities rely on older, less efficient cooling architectures like water-cooled chillers or evaporative cooling towers. In these legacy designs, water is evaporated to remove the latent heat of vaporisation from the air, and that evaporated water is never recovered.”
The IDCA report ranked countries on a “water stress” scale of 0-100, where those with deserts are unsurprisingly high on the scale and mountainous and riverine states at the low end. Most at risk are Bahrain (100), Belize (86), Libya (80), Kuwait (80) and South Sudan (73). The least at risk are Norway (0), New Zealand (0), Iceland (1), Canada (2) and Bhutan (3).
Servers per head differential of 100,000x
The IDCA report said there was a difference of 100,000x in the number of servers per head of population between the most and least dense in this respect. Providing connectivity alongside this, IDCA said there was an estimated 1.3 to 1.5 million km of subsea cables, in around 550 systems, with about 1,200 landing stations.
Out of these, there are around 70 landing stations in the US, 50 in the UK and more than 12 in countries that include the Philippines, Indonesia, Japan, Spain, Denmark, Sweden and some Middle Eastern countries. Meanwhile, there are around 14 million km of terrestrial cables in main networks.
IT jobs deficit
IDCA found that IT jobs worldwide account for between 0.1% and 4% of populations. According to IDCA, 2.5% of the workforce employed in tech was optimum to “to ensure a thorough, successful digital economy creation and management”, though this varied based on local conditions and expectations.
Overall, the IDCA found that there was a deficit of 100 million IT-related jobs worldwide, with developing nations accounting for 80% of that.
Ranking countries with the most deficit, top of the list was India, with a shortfall of 28.8 million in the IT workforce, followed by China (17.5 million), Pakistan (5.8 million), Nigeria (5.8 million), and Indonesia (5.3 million).
Gamma, Sigma and Goldilocks
The report covered a number of other areas in connection with datacentres that include datacentre security, standards, design, investment and community pushback. It also provided three indexes: Gamma, Sigma and Goldilocks, with countries ranked 0-100.
The Gamma index looked at technological and social factors in digital readiness. Top of the list was: Finland at 85 (with Scandinavia collectively ranking 83), the Netherlands (83), Estonia (80), New Zealand (79) and Switzerland (79). Bottom of the list was: Equatorial Guinea (4), South Sudan (12), Turkmenistan (17), Haiti (17), and Democratic Republic of Congo (19). The UK ranked 14th, with a score of 74.
The Sigma index integrated the Gamma index, with adjustments for stress on water and electricity grids, such as the amount of headroom they possess, for example. The Sigma index was topped by Finland (99), followed by Sweden (97), Norway (97), New Zealand (94) and Iceland (94). The UK was ranked 15th (84).
“The Sigma Index is useful in determining a nation’s overall suitability for rapid datacentre growth and the digital infrastructure that would accompany it,” the report said.
Finally, the IDCA report provided a Goldilocks index, which technological factors are separated from the rest then comparing those to the cost of living and income. That way, it hoped to provide an idea of countries for whom rapid development would not be disruptive and would hit “just right”. Top of the Goldilocks index was Colombia with a score of 5.2, followed by North Macedonia, China, South Africa and Montenegro, all on 5.2 except the last of these (5.1).
Tech
Microsoft releases rare zero-day free Patch Tuesday update | Computer Weekly

Microsoft has addressed around 140 newly discovered common vulnerabilities and exposures (CVEs) in its May Patch Tuesday update, but for the first time in a long time, the latest monthly drop contains no zero-day flaws, meaning that none of the issues in scope have been actively exploited or publicly disclosed.
But while a less panic-inducing drop will be welcomed by security teams around the world, the May 2026 Patch Tuesday update contains almost 20 critical severity flaws that will inevitably draw the attention of threat actors in the coming days and weeks.
Jack Bicer, Action1 director of vulnerability research, said: “Although the absence of zero-days is a positive sign, the high number of critical vulnerabilities – particularly compared to recent months – means organisations should still move quickly to evaluate and deploy updates across affected systems.”
This month’s update is also particularly significant as it heralds a critical Secure Boot certificate expiration deadline on 26 June, a few weeks from now. Devices that fail to receive updated Secure Boot certificates – which are now rolling out – face potentially catastrophic failures or as-yet-undiscovered security flaws that may prove impossible to fix.
“The May 2026 update cycle is a high-stakes bridge to the 26 June certificate expiration deadline, making fleet-wide rotation to new trust anchors the month’s absolute priority,” said Rain Baker, senior incident response specialist at Nightwing’s ShadowScout team.
“For those who haven’t patched for last month’s releases for the Windows Shell and Microsoft Defender bypass flaws, it is imperative that security teams give these the highest priority,” added Baker.
Bugs abounding
Among some of the critical updates issued this month is a fix for a Windows DNS Client remote code execution (RCE) flaw tracked as CVE-2026-41096. This vulnerability stems from a heap-based buffer overflow condition in Windows NetLogon and could enable an unauthenticated actor to take over the target system by sending it a malicious DNS response.
“Because DNS is a core networking service used across enterprise environments, exploitation could impact a large number of systems rapidly,” said Action1’s Bicer.
“Successful attacks may lead to widespread endpoint compromise, ransomware deployment, credential harvesting, and operational disruption across corporate networks.
Bicer added: “This CVE requires immediate attention considering its severity rating, network-based attack vector, no authentication requirements, and no user interaction. DNS-related vulnerabilities are especially dangerous because they target foundational network services that are broadly exposed across enterprise infrastructure.”
Also drawing attention this evening is CVE-2026-42898, another RCE issue, this one in on-prem versions of Microsoft Dynamics 365, which bears a common vulnerability scoring system (CVSS) score of 9.9. Again, this issue requires no user interaction and because it can impact systems beyond the original security scope of the vulnerable component, carries an extreme risk to enterprises.
Previous attacks on Dynamics 365 infrastructure have exposed important, privileged data, and because CRM environments plug into so many other important systems, successful exploitation could lead to wholesale compromise.
Meanwhile, Automox chief technology officer Jason Kikta weighed in on CVE-2026-41089, an RCE flaw in Windows Netlogon, and CVE-2026-40402, an elevation of privilege (EoP) vulnerability in Hyper-V.
“CVE-2026-41089 – CVSS 9.8 out of 10 – is a stack-based buffer overflow in Windows Netlogon,” explained Kikta. “An attacker sends a crafted network request to a domain controller. No authentication required. No user interaction required. If you’ve been doing this long enough, the description language sounds sadly familiar.
“I’d be careful drawing a direct line to Zerologon. The underlying bug is a stack overflow, not a crypto protocol flaw, and Microsoft has not labeled this one as wormable. The mechanism is different, but the blast radius is still ugly when you’re talking about pre-auth code execution on a domain controller.”
The Hyper-V issue can be exploited by a low-privileged account inside a guest virtual machine (VM) to execute code on the host with system-level privileges. Kikta warned that one compromised guest could serve as a pivot point for every other VM on the same host, and the host fabric into the bargain. Hosted desktop environments and shared virtualisation platforms are likely to be swiftly targeted.
“Multi-tenant VDI, on-premises virtualisation with untrusted workloads, or any Hyper-V host running guests you don’t fully control. Same-week, same-day patch depending on what’s on top of it,” Kikta advised.
Patch apocalypse?
Lacking though it is in zero-days, Redmond’s latest meaty update will do little to assuage the concerns of onlookers alarmed at the supposedly earth-shattering vulnerability discovery capabilities of Anthropic’s Claude Mythos frontier AI model.
Chris Goettl, vice president of security product management at Ivanti, said that these concerns were being taken seriously by many key software suppliers and other tech firms that are becoming far more aggressive in their patching in response to the changes of the past few weeks.
“Oracle announced a new release cadence starting in May 2026 to address the acceleration of vulnerability detection introduced by Mythos and other AI security models; monthly Critical Security Patch Update (CSPUs) will fill in the two-month gap between their quarterly Critical Patch Update (CPU),” he said.
“Apple is another early participant in Project Glasswing and has seen a recent spike in the number of exposures resolved. They typically average around 20 CVEs per iOS security update [but] for their most recent update on May 11, there is a spike of 52 CVEs resolved. Across the 11 Apple updates, the CVE counts range from 25 at the low end to 52 on the high end and Apple backported changes all the way to iPhone 6s and iOS 15. While there are not actively exploited vulnerabilities, there are a lot of updates to manage.”
Meanwhile, Mozilla, the backers of the Firefox browser, which is said to have had over 270 vulnerabilities identified after Claude Mythos was applied to it, has also moved to a more aggressive weekly cadence for its security updates since the release of Firefox 150.0.0 in April 2026 – version 150.0.3 of Firefox dropped earlier today (12 May).
-
 Tech1 week ago
Tech1 week agoDHS Demanded Google Surrender Data on Canadian’s Activity, Location Over Anti-ICE Posts
-

 Business1 week ago
Business1 week agoHeineken plans huge investment in hundreds of UK pubs ahead of World Cup
-

 Tech5 days ago
Tech5 days agoA new frontier: Identity stack evolves for agentic systems | Computer Weekly
-

 Tech4 days ago
Tech4 days ago‘Orbs,’ ‘Saucers,’ and ‘Flashes’ on the Moon: Pentagon Drops New UFO Files
-

 Business1 week ago
Business1 week agoIndia among most resilient large EMs, better placed for future global shocks; policy reforms & strong buffers help: Moody’s – The Times of India
-

 Fashion5 days ago
Fashion5 days agoNew orders in German manufacturing up 5% MoM in Mar 2026: Destatis
-

 Tech5 days ago
Tech5 days agoWhat Microsoft Executives Really Thought About OpenAI in 2018
-

 Sports5 days ago
Sports5 days agoShaheen Afridi achieves landmark feat during opening Test against Bangladesh