Tech
Security flaws in portable genetic sequencers risk leaking private DNA data

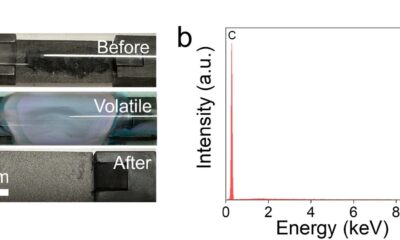
Portable genetic sequencers used around the world to sequence DNA have critical, previously unreported security vulnerabilities that could reveal or alter genetic information without detection, according to a new study.
Researchers from the University of Florida have, for the first time, exposed these security risks in devices from Oxford Nanopore Technologies, which produces nearly all the portable genetic sequencers in the world.
Alerted by the security researchers, Oxford Nanopore Technologies has rolled out updated software to patch the vulnerabilities. But out-of-date software, or unsecured internet systems, could still leave some DNA sequencers vulnerable to attack.
“No one in the world had looked at the security of these devices, which shocked me,” said Christina Boucher, Ph.D., a professor of computer and information science and engineering at UF, expert in bioinformatics, and co-author of the new report.
Boucher collaborated with Sara Rampazzi, Ph.D., also a professor of computer and information science and engineering, cybersecurity expert and project lead at UF, and students in the department to test Nanopore sequencers for security flaws. The study serves as a warning to the scientific community that new threats to genomic data urge a shift toward “secure-by-design” systems as portable DNA sequencers become increasingly common. The team published their findings in Nature Communications.
The researchers uncovered three vulnerabilities in the Oxford Nanopore MinION portable sequencer and its associated software. Two of these flaws allow an unauthorized user to improperly access the device and potentially copy or alter the DNA data without the authorized user’s knowledge. A third flaw opens the sequencer to a denial-of-service attack, which would halt the sequencing operation and make the device appear broken.
The Cybersecurity and Infrastructure Security Agency, the federal government’s cyber defense coordinator, verified these vulnerabilities in a report released Oct. 21. The report also provides instructions from Oxford Nanopore Technologies on how users can update their sequencers to address the security flaws.
Versions with older software would remain open to attack. This is especially possible when the portable sequencers are connected to insecure Wi-Fi networks or remote control is activated.
Costing just a few thousand dollars and able to operate anywhere in the world, these palm-sized sequencers have transformed the previously cumbersome and expensive work of sequencing DNA. But that portability contributes to the security risks of these devices because the sequencers must be connected to a computer to work.
“You are connecting a very specialized device to a general-purpose device like a laptop, which is intrinsically assumed to be secure,” said Rampazzi. “Instead, that laptop could be connected to an unsecured network, or it could be infected with malware or ransomware, especially if used in the field outside controlled environments.”
These nanopore sequencers are marketed only for research use and not to be used for clinical diagnosis. Yet even when restricted to research, these devices can be used to sequence the DNA of people.
The U.S. National Institute of Standards and Technology, which focuses on defining genomic cybersecurity and privacy guidelines, has only started to consider research use cases in distinction to clinical use in their latest draft guidelines, highlighting the increased attention on the topic and the lack of a clear standard.
Revealing these previously undiscovered vulnerabilities was only possible due to the interdisciplinary collaboration between the Rampazzi and Boucher labs. Boucher develops algorithms to better analyze DNA, while Rampazzi researches security flaws in critical systems ranging from medical devices, and self-driving cars to underwater data centers. Combining their expertise helped alert the community to a significant privacy threat.
“In bioinformatics, we haven’t been working as closely with the security community as I think we should be,” Boucher said.
More information:
Toward security-aware portable sequencing, Nature Communications (2025). DOI: 10.1038/s41467-025-66024-z
Citation:
Security flaws in portable genetic sequencers risk leaking private DNA data (2025, November 10)
retrieved 10 November 2025
from https://techxplore.com/news/2025-11-flaws-portable-genetic-sequencers-leaking.html
This document is subject to copyright. Apart from any fair dealing for the purpose of private study or research, no
part may be reproduced without the written permission. The content is provided for information purposes only.
Tech
Robotaxi Outage in China Leaves Passengers Stranded on Highways

An unknown technical problem caused a number of robotaxis owned by the Chinese tech giant Baidu to freeze on Tuesday in the middle of traffic, trapping some passengers in the vehicles for more than an hour.
In Wuhan, a city in central China where Baidu has deployed hundreds of its Apollo Go self-driving taxis, people on Chinese social media reported witnessing the cars suddenly malfunction and stop operating. Photos and videos shared online show the Baidu cars halted on busy highways, often in the fast lane.
A college student in Wuhan tells WIRED that she was stuck in a Baidu robotaxi with two friends for about 90 minutes on Tuesday. (She asked to be only identified with her last name, He, to protect her privacy.) The student says the car malfunctioned and stopped four or five times during the trip before it eventually parked in front of an intersection in eastern Wuhan. Luckily, it was not a busy road, and the group was not in immediate danger. The screen display in the car asked the passengers to remain in the car with seatbelt on and wait for a company representative to come “in five minutes,” according to a photo He shared with WIRED.
He says it took about 30 minutes to reach a Baidu customer representative on the phone. “They kept saying it would be reported to their superior. But they didn’t explain what caused [the outage] or let us know how long we needed to wait for the staff to come,” He says. But no one ever came, and after another hour of waiting, the three passengers decided to just get out and go home by themselves (the doors weren’t locked).
On Chinese social media, other passengers also complained about being unable to reach Baidu’s customer support. “I tried every way I could think of to call for help using the options the app showed, but the phone line wouldn’t go through, and when I pressed the SOS button it told me it was unavailable. So then what exactly is the SOS for?” wrote one person in a post on RedNote alongside a video showing the button not working. She said she had to force the door to open and get out of the car as traffic halted to a complete stop behind her robotaxi. “Apollo Go, you really owe me an apology,” she wrote.
Baidu didn’t immediately respond to a request for comment. Local police in Wuhan issued a statement around midnight in China that said the situation was “likely caused by a system malfunction,” but the incident is still under investigation. No one was injured and all passengers have exited the vehicles, the police added. It’s unclear how many of Baidu’s robotaxis may have been impacted.
One dash cam recording posted to RedNote shows a car passing 16 Apollo Go vehicles parked on the road in the span of 90 minutes. On several occasions, the video shows the driver narrowly avoiding hitting the robotaxis by braking or changing lanes at the last minute.
Others were apparently not as fortunate. In another RedNote post, a man claimed he crashed into one of the malfunctioning Baidu vehicles. The man wrote in the caption that he was driving over 40 mph on a highway when the car in front of him suddenly changed lanes to avoid the stopped robotaxi. He couldn’t react fast enough and ended up running into the self-driving car. Photos of the man’s orange SUV being towed away show that the car’s front-right fender was completely torn off, and other parts appeared to have sustained major damage.
Tech
Our Favorite Affordable Air Purifier Is Temporarily Even Cheaper

Tired of the stale, fetid air looming over your apartment like a cloud? Check out the Coway Airmega Mighty, an already wallet-friendly home air purifier that’s even cheaper right now as part of the Amazon Big Spring Sale. It’s currently marked down to just $154, a $76 discount from its typical price, but you’ll want to move quickly if you’re interested, as the deal is only available for a limited time.
Despite its low price tag and squat stature, the Airmega Mighty is capable of cleaning a substantial amount of space. At full bore, it can handle a 361-square-foot space, although you’ll get the best performance, and save your ears, if you’re closer to a 200-square-foot room. If you don’t want it running constantly, there are built-in timers to automatically shut off after 1, 4, or 8 hours, or you can use Eco Mode, which will run until the Might doesn’t sense any dirty air for half an hour.
That’s right, the Airmega Mighty has a built-in air quality sensor, and it reflects the current state of the air quality using a colored light with three levels. It uses those readings to automatically adjust the fan speed and timing settings on the fly, as well as giving you a peak into how bad the air you’re breathing right now is for you. While it lacks integration with smart home setups like Google Home, it makes up for it by handling all of its own business without Wi-Fi or extra apps on your phone.
While the Coway Airmega Mighty is available in three colors, only the black and silver model is currently discounted, so you’ll have to pay full price if it doesn’t match your living room’s color scheme. We’ve put in the work testing every air purifier we could get our hands on, so make sure to check out the full guide if you’re trying to clean up your space. The Coway is discounted as part of Amazon’s Big Spring Sale, and we’ve got the best deals from products we’ve tested gathered in one place if you want to save some bucks.
Tech
In a Big Reversal, Zohran Mamdani Tells NYC Agencies to Use TikTok

New York City mayor Zohran Mamdani, who rode a social media-fueled campaign to Gracie Mansion, is reversing an Eric Adams–era directive barring TikTok from government-owned devices. Local agencies will now be able to post about their projects on the app, though with new guardrails to protect city networks.
“The Mamdani administration is committed to using every tool in our toolbox to communicate with New Yorkers,” says the email to agencies, obtained by WIRED. “At a moment when people are turning to city government for information about free services, emergency situations, upcoming events, and more, we want to open up new avenues of communication with the public and help deliver the information New Yorkers need.”
In August 2023, then-mayor Adams barred the use of TikTok on government devices, joining the ranks of other state and federal agencies that at the time deemed the app a major security risk. Adams spokesperson Jonah Allon said then that the city’s Cyber Command office had decided that TikTok, which was owned by the Chinese-based company ByteDance, “posed a security threat to the city’s technical networks and directed its removal from city-owned devices.”
The directive resulted in a number of popular city-run accounts shutting down, including accounts for the NYC Departments of Sanitation and Parks and Recreation. As of Tuesday morning, the accounts’ bios read, “This account was operated by NYC until August 2023. It’s no longer monitored.”
Now, these TikTok accounts will be allowed to reopen with a few new rules aimed at protecting the security of NYC’s networks and devices while allowing agencies to communicate with citizens on the popular app. In order to use TikTok, agencies will be required to use separate, government-issued devices for the app that “cannot contain sensitive or restricted data, and they cannot be used for email, internal systems, or privileged access,” according to the email to agencies. Agencies will designate specific staff from media and press offices to run the TikTok accounts with city government emails, not personal ones.
“In a fragmented media landscape, more and more people—especially younger people—are looking beyond the four corners of their television screen to stay informed,” Mamdani said in a statement to WIRED. “Our responsibility is simple: Meet people where they are. That means stepping outside our comfort zones and communicating in ways that reflect how New Yorkers actually live, work, and connect.”
Mamdani’s rule reversal comes after his November election that relied heavily on social media to conduct voter outreach. Mamdani leveraged TikTok to recruit volunteers and amplify his policy platform. Over his first few months in office, Mamdani has continued to leverage social media platforms, publishing a variety of public-service announcements related to city-run programs.
Ahead of dangerous winter weather in January, Mamdani published a video to the official @nycmayor account on Instagram asking New Yorkers to sign up for the city’s free emergency communications program, NotifyNYC. The program netted more than 32,000 new subscribers in the four days after the video was released, according to stats provided by Mamdani’s office. Last year, New York City Emergency Management ran a $240,000 advertising round for NotifyNYC, acquiring around 48,000 new subscribers. Mamdani also created a handful of videos asking New Yorkers to join a Department of Sanitation snow-shoveling program. Around 5,000 people signed up, tripling the number previously enrolled in the program.
The situation has also changed for the app. In January 2026, TikTok finalized a deal with the Trump administration to form a new US-based version of the company run by American investors, including Oracle. The consortium of American investors staved off a nationwide ban of the app.
-

 Politics1 week ago
Politics1 week agoAfghanistan announces release of detained US citizen
-

 Sports1 week ago
Sports1 week agoBroadcast industry CEO says consolidation is ‘essential’ to compete for NFL soaring media rights prices
-

 Business1 week ago
Business1 week agoProperty Play: Home flippers see smallest profits since the Great Recession, real estate data firm says
-

 Entertainment1 week ago
Entertainment1 week agoUN warns migratory freshwater fish numbers are spiralling
-

 Tech1 week ago
Tech1 week agoCan a Home Appliance Fix the Problem of Soft-Plastic Waste?
-

 Business1 week ago
Business1 week agoGold prices soar in Pakistan – SUCH TV
-

 Fashion1 week ago
Fashion1 week agoICE cotton slips on weaker crude, profit booking
-

 Business1 week ago
Business1 week agoMore women are entering wealth management, but few are in advisory roles, study finds