Tech
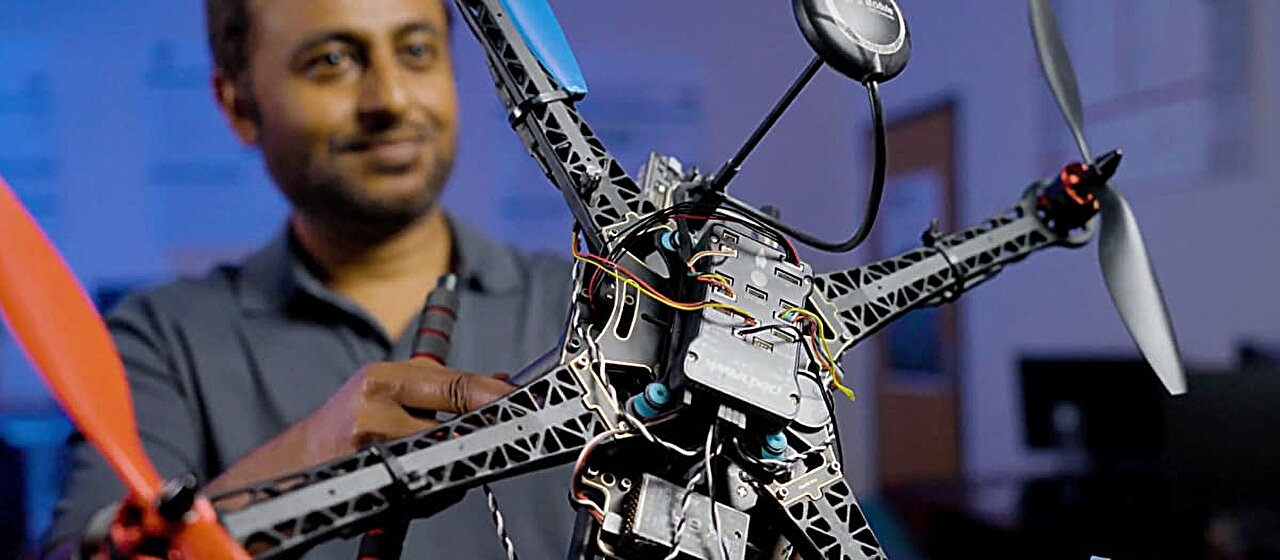
SHIELD activated: Researchers build defense to protect drones from cyberattacks
Fooled into following a hacker’s rogue commands, a drone is liable to do any number of things. Fly erratically. Speed up. Slow down. Hang suspended in the air. Reverse course. Take a new course. And, most dangerously: Crash.
What the compromised drone cannot do, however, is regain control. Lost to its original assignment—whether it’s delivering a package, inspecting an aging bridge or monitoring the health of crops—the machine is essentially useless.
At FIU, cybersecurity researchers have developed a series of countermeasures to fight back mid-flight against hostile takeovers.
Because drones are essentially flying computers, they are subject to the same software and hardware exploitation as their land-bound counterparts. But current drone-defense techniques fail to monitor all possible vulnerabilities.
FIU’s technology, called SHIELD, is different. Keeping watch over the entire control system, it picks up on subtle cues of malicious activity. It then identifies the kind of attack—even the stealthiest ones that often slip under the radar—before launching an attack-specific recovery process. The findings were presented at the IEEE/IFIP International Conference on Dependable Systems and Networks.
“Without robust recovery mechanisms, a drone cannot complete its mission under attacks, because even if it is possible to detect the attacks, the mission often gets terminated as a fail-safe move,” said Mohammad Ashiqur Rahman, lead researcher and associate professor in FIU’s Knight Foundation School of Computing and Information Sciences.
“What’s important about our framework is that it helps the system recover, so the mission can be completed.”
Safeguarding the security of drones may soon become more important than ever before. This summer, the Federal Aviation Administration proposed expanding commercial drone use across industries. From Amazon deliveries to agriculture, the FAA expects more businesses to deploy unmanned aircraft, raising questions about safety in the face of increasingly sophisticated cyber threats.
Traditionally, attack detection has revolved around sensors that help the drone perceive its surroundings and fly safely. But these sensors can be easily manipulated. For example, in “GPS spoofing,” hackers transmit fake coordinates to trick the drone into taking a different trajectory.
Sophisticated cyberattacks, though, bypass the sensors and go straight for the control or actuation system, sneaking malware into the drone’s hardware.
“This is why a detection and recovery system that only takes into account the sensors misses the bigger picture,” says Muneeba Asif, Ph.D. candidate in Rahman’s research group and study author. “It will be blind to other attacks that happen across the system and at different levels.”
SHIELD goes further by monitoring the drone’s entire control system. It detects abnormalities not just in sensors but also in the hardware. For example, the battery and computer components reveal a lot. Sudden surges in battery power or overworked processors are strong indicators that an attack is in progress.
The research team, which also includes FIU students Jean Tonday Rodriguez and Mohammad Kumail Kazmi, compares their approach to how a doctor arrives at a final diagnosis. A symptom (in this case, sensor data) doesn’t always reveal the underlying cause of an illness. Physical evidence (what’s happening with the battery), though, can provide a better idea of what’s going on.
And, just as every diagnosis dictates a different treatment, the researchers also find each attack needed a more tailored recovery plan.
Through multiple hardware-in-the-loop simulations in the lab, researchers learned that every attack leaves behind a unique signature and impacts the drone‘s system differently. So, the team trained AI machine learning models to spot abnormalities in the data, use the data to classify the attack and roll out the prescribed recovery protocol. In the lab, all of this happened in less than a second. Average detection time was 0.21 seconds, and recovery 0.36 seconds.
Next, Rahman’s research group will scale up testing, preparing SHIELD for real-world deployment.
With drones poised to reshape commerce, infrastructure monitoring, disaster response and more, FIU researchers say securing them is no longer optional.
“Reliable and secure drones are the key to unlocking future advancements,” Rahman said. “It’s our hope this work can play a role in moving the industry forward.”
More information:
Muneeba Asif et al, “I will always be by your side”: A Side-Channel Aided PWM-based Holistic Attack Recovery for Unmanned Aerial Vehicles, 2025 55th Annual IEEE/IFIP International Conference on Dependable Systems and Networks (DSN) (2025). DOI: 10.1109/dsn64029.2025.00070
Citation:
SHIELD activated: Researchers build defense to protect drones from cyberattacks (2025, October 7)
retrieved 7 October 2025
from https://techxplore.com/news/2025-10-shield-defense-drones-cyberattacks.html
This document is subject to copyright. Apart from any fair dealing for the purpose of private study or research, no
part may be reproduced without the written permission. The content is provided for information purposes only.
Tech
‘The Last Airbender’ Leaked Online. Some Fans Say Paramount Deserves the Fallout

The online leak of a full version of Avatar: Aang, The Last Airbender—a highly anticipated animated film in a multimedia fantasy franchise—has divided passionate fans while upsetting those who spent years working on the film.
The leaks began on X late on Saturday night, about six months before Aang was scheduled to premiere on Paramount+. User @ImStillDissin posted two short clips from the film. “Nickelodeon accidentally emailed me the entire Avatar aang movie,” he claimed. He also threatened to stream the entire movie if Paramount didn’t release an official trailer, and he posted a still from the movie’s end credits, revealing previously undisclosed voice-over cast and roles. The media from @ImStillDissin’s posts were later hit with copyright strikes and removed.
But within 48 hours, links to download the full movie appeared on 4chan and X, where some users also directly streamed the film. Across the web, fans said they had successfully pirated and watched what appeared to be a nearly finished and “beautiful” animated film.
While some argued that Paramount deserved to be punished because of certain creative and marketing decisions around the movie, others noted what a blow the leak was to the animators and production crew. A number of those team members took to social media to convey their sadness and frustration.
“We worked on the aang movie for years with the expectation that’d [sic] we’d get to celebrate all of our hard work in theaters. Just to see people unceremoniously leak the film and pass our shots around on twitter like candy,” animator Julia Schoel wrote Tuesday on X.
The user behind @ImStillDissin, who would not reveal his real name due to fear of legal repercussions, tells WIRED that he obtained the movie almost by chance and did not expect his posts to set off such a crisis in the entertainment world. “When I posted those clips I was purely trolling,” he says. “I was expecting a day of clout farming at best, not for the whole thing to blow up like this.”
(While WIRED has done its due diligence in verifying that the person speaking to us was behind the @ImStillDissin X account, we acknowledge that the hacking community is known to troll.)
According to @ImStillDissin, a screen-grabbed version of Avatar: Aang, The Last Airbender was circulating among people he knew from his days in the hacking community, one of whom shared it with him. “Broadly speaking, the supply chain for movies and TV is rife with insecure companies and vendors and lax checks,” he claims. He notes that two different SpongeBob SquarePants movies leaked months before their release dates in 2024. “Someone on 4chan who wasn’t happy at me drip-feeding stuff posted a copy of a draft script [of the new Avatar film] from like two years back,” says @ImStillDissin.
Neither Nickelodeon nor its parent company Paramount have confirmed a hack had taken place, nor have they issued a statement on the matter. They also did not respond to requests for comment.
Originally announced in 2021, Avatar: Aang, The Last Airbender marked the first production for Avatar Studios, a division of Nickelodeon’s animation department.
Some people felt justified in pirating and sharing the movie due to the recasting of voice actors. Last year, during a Reddit AMA, casting director Jenny Jue wrote that the voice cast from the Avatar TV show that aired on Nickelodeon in the 2000s was not returning due to efforts to “match actors’ ethnic/racial background to the characters they’re portraying.”
Tech
NASA Wants to Put Nuclear Reactors on the Moon

Having demonstrated that it has the operational capability to transport humans safely to the moon and back, the United States is moving on to its next major aim: It wants nuclear reactors in orbit and on the lunar surface by 2030. For such a feat, the National Aeronautics and Space Administration will have to work in conjunction with the Department of Defense and the Department of Energy.
In a post on X, the White House Office of Science and Technology Policy (OSTP) unveiled a document with new guidelines for federal agencies to establish the space nuclear technology road map for the coming years. This, they say, will ensure “US space superiority.”
At present, space instruments use solar power to operate. However, this is considered impractical for more complex purposes. Although technically there is always sunlight, the power is intermittent and almost always requires bulky batteries to store it.
Reactors produce fairly continuous energy for years through nuclear fission. They can also be used for so-called nuclear electric propulsion. Continuous output makes them the most viable option for lunar base subsistence, but they can also allow spacecraft to undertake long or complex missions without worrying about depleting a limited supply of chemical fuel.
Nuclear technology, in short, makes it possible to go farther, with more payload, for longer, and with fewer constraints.
According to the memorandum, the US goal is to put a medium-power reactor in orbit by 2028, with a variant designed for nuclear electric propulsion, and a first functional large reactor on the surface of the moon by 2030. To achieve this, both NASA and the Pentagon will develop energy technologies in parallel, using the current strategy of competition among contractors.
The reactors will have to be modular and scalable, and will have to include applications for both future life on the moon and space propulsion. For its part, the DOE will have to ensure that these projects have the fuel, infrastructure, and safety features necessary to achieve their objectives. In addition, the agency will evaluate whether the industry has the capacity to produce up to four reactors in five years.
The plan contemplates technologies that produce at least 20 kilowatts of electricity (kWe) for three years in orbit and at least five years on the lunar surface. In the meantime, they should have a design capable of raising power to 100 kWe. The first designs should arrive within a year.
Finally, the order tasks the OSTP with creating a road map for the initiative, noting obstacles and recommendations for addressing them.
“Nuclear power in space will give us the sustained electricity, heating, and propulsion essential to a permanent presence on the moon, Mars, and beyond,” OSTP posted. For his part, NASA administrator Jared Isaacman posted, “The time has come for America to get underway on nuclear power in space.” The message was followed by an emoji of a US flag.
The plan provides a common framework for each agency to work within. In the background, the race for space infrastructure is evidence of technological competition with China, which is also seeking advanced energy capabilities for the moon.
This story originally appeared in WIRED en Español and has been translated from Spanish.
Tech
AI Could Democratize One of Tech’s Most Valuable Resources
Nvidia is the undisputed king of AI chips. But thanks to the AI it helped build, the champ could soon face growing competition.
Modern AI runs on Nvidia designs, a dynamic that has propelled the company to a market cap of well over $4 trillion. Each new generation of Nvidia chip allows companies to train more powerful AI models using hundreds or thousands of processors networked together inside vast data centers. One reason for Nvidia’s success is that it provides software to help program each new generation of chip. That may soon not be such a differentiated skill.
A startup called Wafer is training AI models to do one of the most difficult and important jobs in AI—optimizing code so that it runs as efficiently as possible on a particular silicon chip.
Emilio Andere, cofounder and CEO of Wafer, says the company performs reinforcement learning on open source models to teach them to write kernel code, or software that interacts directly with hardware in an operating system. Andere says Wafer also adds “agentic harnesses” to existing coding models like Anthropic’s Claude and OpenAI’s GPT to soup up their ability to write code that runs directly on chips.
Many prominent tech companies now have their own chips. Apple and others have for years used custom silicon to improve the performance and the efficiency of software running on laptops, tablets, and smartphones. At the other end of the scale, companies like Google and Amazon mint their own silicon to improve the performance of their cloud-computing platforms. Meta recently said it would deploy 1 gigawatt of compute capacity with a new chip developed with Broadcom. Deploying custom silicon also involves writing a lot of code so that it runs smoothly and efficiently on the new processor.
Wafer is working with companies including AMD and Amazon to help optimize software to run efficiently on their hardware. The startup has so far raised $4 million in seed funding from Google’s Jeff Dean, Wojciech Zaremba of OpenAI, and others.
Andere believes that his company’s AI-led approach has the potential to challenge Nvidia’s dominance. A number of high-end chips now offer similar raw floating point performance—a key industry benchmark of a chip’s ability to perform simple calculations—to Nvidia’s best silicon.
“The best AMD hardware, the best [Amazon] Trainium hardware, the best [Google] TPUs, give you the same theoretical flops to Nvidia GPUs,” Andere told me recently. “We want to maximize intelligence per watt.”
Performance engineers with the skill needed to optimize code to run reliably and efficiently on these chips are expensive and in high demand, Andere says, while Nvidia’s software ecosystem makes it easier to write and maintain code for its chips. That makes it hard for even the biggest tech companies to go it alone.
When Anthropic partnered with Amazon to build its AI models on Trainium, for instance, it had to rewrite its model’s code from scratch to make it run as efficiently as possible on the hardware, Andere says.
Of course, Anthropic’s Claude is now one of many AI models that are now superhuman at writing code. So Andere reckons it may not be long before AI starts consuming Nvidia software advantage.
“The moat lives in the programmability of the chip,” Andere says in reference to the libraries and software tools that make it easier to optimize code for Nvidia hardware. “I think it’s time to start rethinking whether that’s actually a strong moat.”
Besides making it easier to optimize code for different silicon, AI may soon make it easier to design chips themselves. Ricursive Intelligence, a startup founded by two ex-Google engineers, Azalia Mirhoseini and Anna Goldie, is developing new ways to design computer chips with artificial intelligence. If its technology takes off, a lot more companies could branch into chip design, creating custom silicon that runs their software more efficiently.
-

 Fashion1 week ago
Fashion1 week agoIndia’s exports face reset as EU links trade to carbon metrics: EY
-

 Entertainment1 week ago
Entertainment1 week agoQueen Elizabeth II emotional message for Archie, Lilibet sparks speculation
-
 Entertainment1 week ago
Entertainment1 week agoLamar Odom shocking response to Khloé Kardashian account of his overdose
-

 Tech1 week ago
Tech1 week agoAzure customers up in arms over ‘full’ UK South region | Computer Weekly
-

 Tech1 week ago
Tech1 week agoAs the Strait of Hormuz Reopens, Global Shipping Will Take Months to Recover
-

 Fashion1 week ago
Fashion1 week agoCII submits 20-pt agenda to Indian govt to back firms hit by Iran war
-

 Tech7 days ago
Tech7 days agoThis AI Button Wearable From Ex-Apple Engineers Looks Like an iPod Shuffle
-

 Politics6 days ago
Politics6 days agoIndian airlines hit hardest after Dubai limits foreign flights until May 31