Tech
When does it pay for housing associations to replace water and sewage pipes?

Waiting until water damage occurs is expensive. But it also doesn’t make financial sense to replace pipes too early. We looked into the best time to do it.
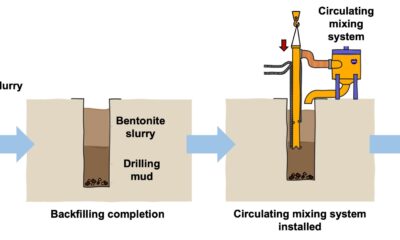
Many housing and condominium associations must decide whether to replace water and sewage pipes. The risk of water leakage needs to be weighed against the costs of fully or partially upgrading the pipe system. A systematic lifespan assessment can provide the board with a good basis for making the decision.
Leaks in water and sewage systems can occur in different ways, and the consequences vary depending on the location of the leak and which materials are affected.
- A leak in a hidden installation on a high floor can cause more damage than a leak in the basement.
- If the water supply is interrupted, several residential units could be result in extensive water damage. In the worst case, the homes would need to be rehabilitated, and the residents would have to move out while the damage is repaired.
- Small leaks are not always detected immediately, but over time can lead to significant damage, such as rot, mold and odor, as well as swelling and salt migration in structures.
Finding the right time for a complete or partial replacement of the water and sewage system is therefore both financially and practically worthwhile.
Researchers at SINTEF have been assessing the condition and remaining life of pipe systems for over 20 years, and we are regularly contacted by condominium owners who wonder whether and when they should replace their pipework. We conduct inspections and laboratory tests to assess the condition of the water and sewage system. Our assessments and recommendations are summarized in a report.
How we calculate condition and remaining lifespan
Age is a simple indicator for assessing the remaining life of pipes, and lifespan tables published by the SINTEF Byggforskserien (Building Research Design Guides) provide helpful guidance. However, age alone does not take into account factors such as load, temperature or water quality.
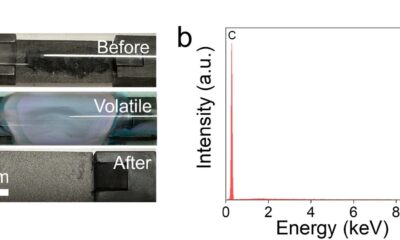
A more accurate assessment of the condition of pipes requires material samples and laboratory analysis (Norway’s NS 3424 standard, level 3). Remaining life is calculated based on the corrosion rate and remaining material thickness. However, such a calculation assumes that this rate is uniform. Changes in water quality and use can affect the corrosion rate, and the calculated remaining life is therefore only indicative.
It is also important to be aware that couplings and valves may have a shorter lifespan than pipes, and that hidden joints increase the risk of damage.
Material samples from critical points in the pipe system provide the best basis for a reliable assessment. Good sampling points can be easily identified if we have access to accurate and up-to-date drawings of the building and the pipe system.

Are the maps and terrain in sync?
However, it is not always practical to retrieve all samples, which might be hidden behind recesses in a bathroom, for example. In addition, the drawing may be outdated, and changes to the installation may have been made without being documented.
An inspection is therefore useful for assessing the correspondence between the drawings and actual installation. At the same time, a cost/benefit assessment should be made for each material sample. If the location for sampling is not easily accessible, the cost will be high.
The frequency of damage should also be included in the assessment. If several leaks have recently occurred, it would be natural to consider replacing the entire pipe system, even if the age indicates that the pipes could last longer. Previous replacements might have led to a confusing system with varying material quality and age.
Upgrade plan and prioritization
Once the condition and remaining life have been assessed, a decision must be made as to which measures should be implemented—and when. We recommend creating an upgrade plan in which necessary measures are prioritized based on technical condition, damage history and overall assessment.
Upgrade measures on the pipe system should be considered in connection with the condition of the wet rooms to avoid extensive demolition work. If the installations are generally in good condition, local repairs may be appropriate. In the event of a high risk of leakage due to varying quality of the wet room installations, or in the event of extensive wear, replacing the entire system may be more appropriate.
Coordinated rehabilitation includes replacing water and sewage pipes, sealing layers, drains, surfaces and electrical installations. The work involves noise and dust, especially during the demolition phase, and the bathroom will typically be out of service for 4–6 weeks. However, the result is a comprehensive system without weak interfaces.
Relining is a method for extending the service life of sewage pipes. Epoxy is applied to the inside of the pipes either by spraying or as a fiber stocking saturated with epoxy. This method can be considered if the water pipes have a longer remaining life than the sewage pipes. It requires less intervention and shorter downtime, but can still involve more difficult work if the drains have to be replaced.
Extensive work and significant costs are usually associated with maintaining and rehabilitating water and sewage systems in housing and condominium associations. A thorough life cycle assessment provides increased security that the chosen solution is correct, and it forms a solid basis for a predictable and effective maintenance plan.
Citation:
When does it pay for housing associations to replace water and sewage pipes? (2025, October 13)
retrieved 13 October 2025
from https://techxplore.com/news/2025-10-pay-housing-associations-sewage-pipes.html
This document is subject to copyright. Apart from any fair dealing for the purpose of private study or research, no
part may be reproduced without the written permission. The content is provided for information purposes only.
Tech
Anthropic Plots Major London Expansion

Anthropic is moving into a new London office as it seeks to expand its research and commercial footprint in Europe, setting up a scrap between the leading AI labs for talent emerging from British universities.
The company, which opened its first London office in 2023, is moving to the same neighborhood as Google DeepMind, OpenAI, Meta, Wayve, Isomorphic Labs, Synthesia, and various AI research institutions.
Anthropic’s new, 158,000-square-foot office footprint will have space enough for 800 people—four times its current head count—giving it room to potentially outscale OpenAI, which itself recently announced an expansion in London.
“Europe’s largest businesses and fastest-growing startups are choosing Claude, and we’re scaling to match,” says Pip White, head of EMEA North at Anthropic. “The UK combines ambitious enterprises and institutions that understand what’s at stake with AI safety with an exceptional pool of AI talent—we want to be where all of that comes together.
UK government officials had reportedly attempted to coax Anthropic into expanding its presence in London after the company recently fell out with the US administration. Anthropic refused to allow its models to be used in mass surveillance and autonomous weapon systems, leading to an ongoing legal battle between the AI lab and the Pentagon.
As part of the expansion, Anthropic says it will deepen its work with the UK’s AI Security Institute, a government body that this week published a risk evaluation of its latest model, Claude Mythos Preview. According to Politico, the UK government is one of few across Europe to have been granted access to the model, which Anthropic has released to only select parties, citing concerns over the potential for its abuse by cybercriminals.
The increasing concentration of AI companies in the same London district is an important step in creating a pathway for research to translate into AI products, says Geraint Rees, vice-provost at University College London, whose campus is around the corner from Anthropic’s new office.
“This cluster didn’t emerge from a planning document. It grew because serious researchers and companies understand that proximity isn’t a nice-to-have,” he said last month, speaking at an event attended by WIRED. “That’s how the innovation system actually works. It’s not a clean, linear transfer from lab to market. It’s messier, richer, more human than that.”
Tech
LG’s High-End Soundbar System Makes My Living Room Feel Like a Home Theater
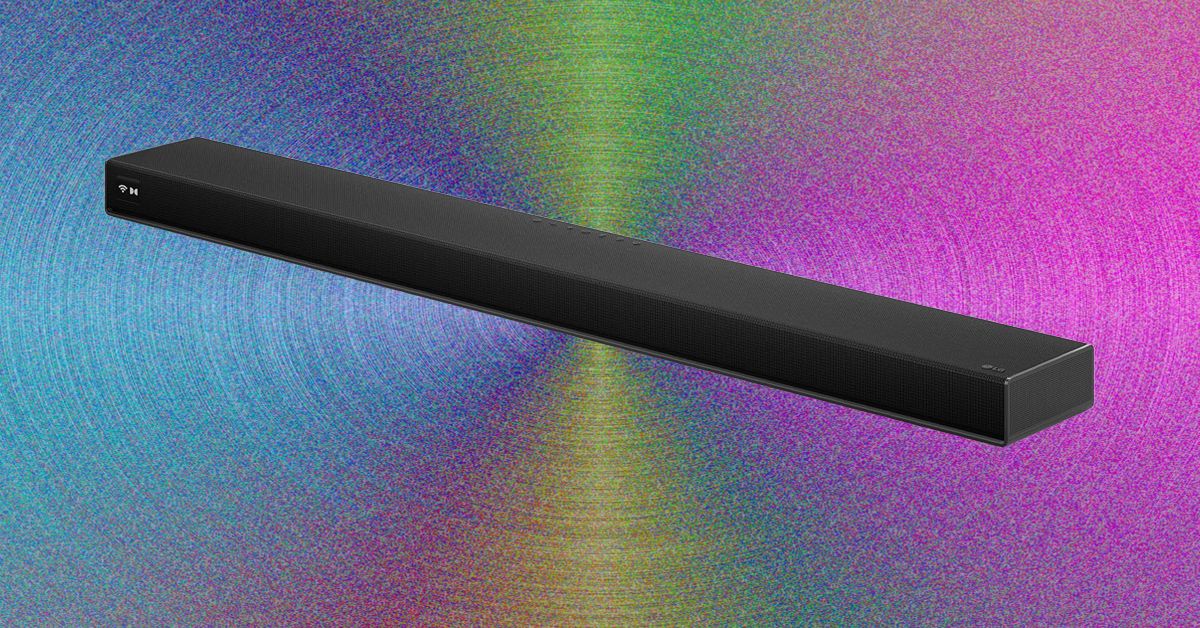
Setup was relatively quick and painless. You just have to unbox four speakers, a soundbar, and a subwoofer, attach their power cables, and plug in everything. Pairing happens through the LG ThinQ app, which allows you to set up the Sound Suite system and tune it to exactly where you’re sitting in the room using your cell phone’s microphone.
You can also set up each speaker to play music and group it with any other LG smart speakers you might have around your home, like the more affordable $250 M5 bookshelf speaker, to create a whole-home system.
Once all the components were synced, I plugged the soundbar into the C5 OLED via HDMI, and was able to easily control everything via the TV remote’s volume and mute buttons. More in-depth settings had to happen in the app, but if you’re anything like me, this won’t become a regular chore. You’ll set it how you like it once and move on. While the pairing functionality with the LG TV was nice, it’s not required–the eARC port lets the Sound Suite work perfectly with any modern TV.
The bar itself runs the show, with a black-and-white display on the far left that shows your mode and volume, among other settings. In the center of the bar and below each speaker, an LED light strip that also shows you the volume when you change it, which is a nice touch.
Getting Musical
Photograph: Parker Hall
The sound of the LG Sound Suite is full and cinematic, thanks in no small part to the extra dedicated speakers. Most competitors lack front left and right, simply opting to use the soundbar for these channels. As such, the width and breadth of the soundstage were bigger than most competitors I’ve tried, with only Samsung’s flagship HW-Q990F as a real contender. Even the Samsung lacked the lower-frequency audio quality that these LG speakers provide.
Tech
Cyber Essentials closes the MFA loophole but leaves some organisations adrift | Computer Weekly

On 27 April, the government backed security certification scheme, Cyber Essentials v3.3, takes effect and multi-factor authentication (MFA) becomes a pass-or-fail requirement for the first time.
If a cloud service your organisation uses offers MFA and you have not enabled it, you fail. No discretion, no partial credit, no route to remediate inside the assessment cycle.
This is the right call. I want to say that clearly, because what follows is a problem with the implementation, not the policy. MFA is the single most effective control against credential-based attacks, and the scheme has needed to stop tolerating its absence for a long time. The National Cyber Security Centre (NCSC), part of GCHQ, which developed Cyber Essentials and certification company, IASME have got this decision right.
But in the assessments we have conducted this year, I have seen two organisations that will hit a wall on 27 April, and I do not think they are unusual.
Train company could not deploy MFA
The first is a train operating company in the South East. Station operations rooms run on shared terminals where staff rotate through shifts in time-critical conditions. A transport union raised formal concerns that MFA would introduce delays at the keyboard that could affect train operations and, in their view, the safety of train movements.
The company listened and chose not to enable MFA in those environments. Under v3.2 they passed, with the relevant questions marked as non-compliant but not fatal. Under Cyber Essentials v3.3 they will fail.
Charity run by volunteers faces MFA hurdle
The second is a nationally known charity with hundreds of high street shops. The shops are staffed largely by volunteers many of whom work a few hours a week, and staff turnover is high.
The cost and management overhead of enrolling every volunteer onto MFA, using personal phones they may not have and authenticator apps they would not keep, was considered prohibitive. So MFA was never switched on. Same story: they passed under v3.2. Under v3.3 they fail.
Neither of these organisations is ignoring security. Both made considered decisions based on how their people actually work. The problem is not that they do not want to comply. It is that the standard toolkit of MFA methods, including SMS codes, authenticator apps on personal phones, and push notifications, does not fit a six-person shared terminal that has to be available in seconds, or a volunteer workforce that changes every week.
FIDO2 could offer solutions
The frustrating part is that there is a solution, and it is already proven in healthcare, manufacturing and retail. FIDO2 authentication delivered through NFC badge-taps lets a staff member authenticate in under two seconds: tap a badge, enter a short PIN, session opens.
It satisfies the MFA requirement by combining possession of the badge with knowledge of the PIN. It is faster than typing a password. Crucially, it is compliant, because each badge is enrolled as that individual’s unique FIDO2 credential, so the Cyber Essentials requirement for unique user accounts is met. Shared keys or shared PINs would not work. Individual badges do.
Need for better guidance
v3.3 explicitly recognises FIDO2 authenticators and passkeys as valid MFA methods. The compliance path is clear. What is missing is anyone telling the organisations most affected that this path exists.
That is the gap that must close. The NCSC and IASME have made the right policy decision; the scheme would be weaker without it.
But implementation guidance for shared-terminal, shift-based and high-turnover environments is thin, and these organisations are running out of time to find their way through it. Many of them hold Cyber Essentials because it is required for government contracts or in their supply chains; losing certification has a direct commercial cost.
The answer is not to soften the requirement. The answer is to make sure no one fails for lack of information about how to meet it.
Jonathan Krause is Founder and Managing Director of Forensic Control
-

 Entertainment1 week ago
Entertainment1 week agoQueen Elizabeth II emotional message for Archie, Lilibet sparks speculation
-

 Tech1 week ago
Tech1 week agoAzure customers up in arms over ‘full’ UK South region | Computer Weekly
-

 Tech1 week ago
Tech1 week agoAs the Strait of Hormuz Reopens, Global Shipping Will Take Months to Recover
-

 Fashion1 week ago
Fashion1 week agoCII submits 20-pt agenda to Indian govt to back firms hit by Iran war
-

 Tech1 week ago
Tech1 week agoThis AI Button Wearable From Ex-Apple Engineers Looks Like an iPod Shuffle
-

 Politics6 days ago
Politics6 days agoIndian airlines hit hardest after Dubai limits foreign flights until May 31
-

 Politics6 days ago
Politics6 days agoChinese, Taiwanese will unite, Xi tells Taiwan opposition leader
-

 Entertainment3 days ago
Entertainment3 days agoPalace left in shock as Prince William cancels grand ceremony