Tech
Underground data fortresses: The nuclear bunkers, mines and mountains being transformed to protect data from attack

It’s a sunny June day in southeast England. I’m driving along a quiet, rural road that stretches through the Kent countryside. The sun flashes through breaks in the hedgerow, offering glimpses of verdant crop fields and old farmhouses.
Thick hawthorn and brambles make it difficult to see the 10ft-high razor-wire fence that encloses a large grassy mound. You’d never suspect that 100ft beneath the ground, a hi-tech cloud computing facility is whirring away, guarding the most valuable commodity of our age: digital data.
This subterranean data center is located in a former nuclear bunker that was constructed in the early 1950s as a command-and-control center for the Royal Air Force’s radar network. You can still see the decaying concrete plinths that the radar dish once sat upon. Personnel stationed in the bunker would have closely watched their screens for signs of nuclear missile-carrying aircraft.
After the end of the cold war, the bunker was purchased by a London-based internet security firm for use as an ultra-secure data center. Today, the site is operated by the Cyberfort Group, a cybersecurity services provider.
I’m an anthropologist visiting the Cyberfort bunker as part of my ethnographic research exploring practices of “extreme” data storage. My work focuses on anxieties of data loss and the effort we take—or often forget to take—to back-up our data.
As an object of anthropological inquiry, the bunkered data center continues the ancient human practice of storing precious relics in underground sites, like the tumuli and burial mounds of our ancestors, where tools, silver, gold and other treasures were interred.
The Cyberfort facility is one of many bunkers around the world that have now been repurposed as cloud storage spaces. Former bomb shelters in China, derelict Soviet command-and-control centers in Kyiv and abandoned Department of Defense bunkers across the United States have all been repackaged over the last two decades as “future-proof” data storage sites.
I’ve managed to secure permission to visit some of these high-security sites as part of my fieldwork, including Pionen, a former defense shelter in Stockholm, Sweden, which has attracted considerable media interest over the last two decades because it looks like the hi-tech lair of a James Bond villain.
Many abandoned mines and mountain caverns have also been re-engineered as digital data repositories, such as the Mount10 AG complex, which brands itself as the “Swiss Fort Knox” and has buried its operations within the Swiss Alps.
Cold war-era information management company Iron Mountain operates an underground data center 10 minutes from downtown Kansas City and another in a former limestone mine in Boyers, Pennsylvania.
The National Library of Norway stores its digital databanks in mountain vaults just south of the Arctic Circle, while a Svalbard coal mine was transformed into a data storage site by the data preservation company Piql. Known as the Arctic World Archive (AWA), this subterranean data preservation facility is modeled on the nearby Global Seed Vault.
Just as the seeds preserved in the Global Seed Vault promise to help re-build biodiversity in the aftermath of future collapse, the digitized records stored in the AWA promise to help re-boot organizations after their collapse.
Bunkers are architectural reflections of cultural anxieties. If nuclear bunkers once mirrored existential fears about atomic warfare, then today’s data bunkers speak to the emergence of a new existential threat endemic to digital society: the terrifying prospect of data loss.
Data, the new gold?
After parking my car, I show my ID to a large and muscular bald-headed guard squeezed into a security booth not much larger than a payphone box. He’s wearing a black fleece with “Cyberfort” embroidered on the left side of the chest. He checks my name against today’s visitor list, nods, then pushes a button to retract the electric gates.
I follow an open-air corridor constructed from steel grating to the door of the reception building and press a buzzer. The door opens on to the reception area: “Welcome to Cyberfort,” receptionist Laura Harper says cheerfully, sitting behind a desk in front of a bulletproof window which faces the car park. I hand her my passport, place my bag in one of the lockers, and take a seat in the waiting area.
Big-tech pundits have heralded data as the “new gold”—a metaphor made all the more vivid when data is stored in abandoned mines. And as the purported economic and cultural value of data continues to grow, so too does the impact of data loss.
For individuals, the loss of digital data can be a devastating experience. If a personal device should crash or be hacked or stolen with no recent back-ups having been made, it can mean the loss of valuable work or cherished memories. Most of us probably have a data-loss horror story we could tell.
For governments, corporations and businesses, a severe data loss event—whether through theft, erasure or network failure—can have a significant impact on operations or even result in their collapse. The online services of high-profile companies like Jaguar and Marks & Spencer have recently been impacted by large-scale cyber-attacks that have left them struggling to operate, with systems shutdown and supply chains disrupted.
But these companies have been comparatively lucky: a number of organizations had to permanently close down after major data loss events, such as the TravelEx ransomware attack in 2020, and the MediSecure and National Public Data breaches, both in 2024.
With the economic and societal impact of data loss growing, some businesses are turning to bunkers with the hope of avoiding a data loss doomsday scenario.
The concrete cloud
One of the first things visitors to the Cyberfort bunker encounter in the waiting area is a 3ft cylinder of concrete inside a glass display cabinet, showcasing the thickness of the data center’s walls. The brute materiality of the bunkered data center stands in stark contrast to the fluffy metaphor of the “cloud,” which is often used to discuss online data storage.
Data centers, sometimes known as “server farms,” are the buildings where cloud data is stored. When we transfer our data into the cloud, we are transferring it on to servers in a data center (hence the meme “there is no cloud, just someone else’s computer”).
Data centers typically take the form of windowless, warehouse-scale buildings containing hundreds of servers (pizza box-shaped computers) stored in cabinets that are arranged in aisles.
Data centers are responsible for running many of the services that underpin the systems we interact with every day. Transportation, logistics, energy, finance, national security, health systems and other lifeline services all rely on up-to-the-second data stored in and accessed through data centers.
Everyday activities such as debit and credit card payments, sending emails, booking tickets, receiving text messages, using social media, search engines and AI chatbots, streaming TV, making video calls and storing digital photos all rely on data centers.
These buildings now connect such an incredible range of activities and utilities across government, business and society that any downtime can have major consequences. The UK government has officially classified data centers as forming part of the country’s critical national infrastructure—a move that also conveniently enables the government to justify building many more of these energy-guzzling facilities.
As I sit pondering the concrete reality of the cloud in Cyberfort’s waiting area, the company’s chief digital officer, Rob Arnold, emerges from a corridor. It was Arnold who arranged my visit, and we head for his office—through a security door with a biometric fingerprint lock—where he talks me through the logic of the bunkered data center.
“The problem with most above-ground data centers is they are often constructed quickly, and not built to withstand physical threats like strong winds, car bombs or server theft from breaking and entering.” Arnold says that “most people tend to think of the cyber-side of data security—hackers, viruses and cyber-attacks—which dangerously overlooks the physical side.”
Amid increasing geopolitical tension, internet infrastructure is now a high-value target as “hybrid” or “cyber-physical” sabotage (when cyber-attacks are combined with physical attacks) becomes increasingly common.
The importance of physical internet security has been highlighted by the war in Ukraine, where drone strikes and other attacks on digital infrastructure have led to internet shutdowns. While precise details about the number of data centers destroyed in the conflict remain scant, it has been observed that Russian attacks on local data centers in Ukraine have led many organizations to migrate their data to cloud facilities located outside of the conflict zone.
Bunkers appeal to what Arnold calls “security-conscious” clients. He says, “It’s difficult to find a structure more secure than a bunker”—before adding dryly: “The client might not survive the apocalypse, but their data will.”
Cyberfort specializes in serving regulated industries. Its customer base includes companies working in defense, health care, finance and critical infrastructure. “Our core offering focuses on providing secure, sovereign and compliant cloud and data-center services,” Arnold explains in a well-rehearsed sales routine. “We do more for our customers than just host systems—we protect their reputations.”
Arnold’s pitch is disrupted by a knock at the door. The head of security (who I’m calling Richard Thomas here) enters—a 6ft-tall ex-royal marine wearing black cargo trousers, black combat boots and a black Cyberfort-branded polo shirt. Thomas is going to show me around the facility today.
The entrance to the bunker is located up a short access road. Engineered to withstand the blast and radiation effects of megaton-level thermonuclear detonations, this cloud storage bunker promises its clients that their data will survive any eventuality.
At the armor-plated entrance door, Thomas taps a passcode into the electronic lock and swipes his card through the access control system. Inside, the air is cool and musty. Another security guard sits in a small room behind bulletproof plexiglass. He buzzes us through a metal mantrap and we descend into the depths of the facility via a steel staircase, our footsteps echoing in this cavernous space.
The heavy blast doors and concrete walls of the bunker appear strangely at odds with the virtual “walls” we typically associate with data security: firewalls, anti-virus vaults, and spyware and spam filters. Similarly, the bunker’s military logics of enclosure and isolation seem somewhat outdated when faced with the transgressive digital “flows” of networked data.
However, to dismiss the bunkered data center as merely an outmoded piece of security theater is to overlook the importance of physical security—today and in the future.
We often think of the internet as an immaterial or ethereal realm that exists in an electronic non-place. Metaphors like the now retro-sounding cyberspace and, more recently, the cloud perpetuate this way of thinking.
But the cloud is a material infrastructure composed of thousands of miles of cables and rows upon rows of computing equipment. It always “touches the ground” somewhere, making it vulnerable to a range of non-cyber threats—from thieves breaking into data centers and stealing servers, to solar storms disrupting electrical supplies, and even to squirrels chewing through cables.
If data center services should go down, even for a few seconds, the economic and societal impact can be calamitous. In recent years we have seen this first-hand.
In July 2020, the 27-minute Cloudflare outage led to a 50% collapse in traffic across the globe, disrupting major platforms like Discord, Shopify, Feedly and Politico. In June 2021, the Fastly outage left some of the world’s most visited websites completely inaccessible, including Amazon, PayPal, Reddit, and the New York Times.
In October 2021, Meta, which owns Facebook, WhatsApp and Instagram, experienced an outage for several hours that affected millions of social media users as well as hundreds of businesses.
Perhaps the largest internet outage yet occurred in July 2024 when the CrowdStrike outage left supermarkets, doctors’ surgeries, pharmacies, airports, train providers and banks (among other critical services) unable to operate. This was described by some in the industry as “one of the largest mass outages in IT history”.
Internet architecture now relies on such a complex and fragile ecosystem of interdependencies that major outages are getting bigger and occurring more often. Downtime events can have a lasting financial and reputational impact on data center providers. Some attempts to quantify the average cost of an unplanned data center outage range from US$9,000 to US$17,000 (about £12,500) per minute.
The geographic location of a data center is also hugely important for data protection regulations, Thomas explains, as we make our way down a brightly lit corridor. “Cyberfort’s facilities are all located in the UK, which gives our clients peace of mind, knowing they comply with data sovereignty laws.”
Data sovereignty regulations subject data to the legal and privacy standards of the country in which it is stored. This means businesses and organizations must be careful about where in the world their data is being relocated when they move it into the cloud. For example, if a UK business opts to store its data with a cloud provider that uses data centers based in the US, then that data will be subject to US privacy standards which do not fully comply with UK standards.
In contrast to early perceptions of the internet as transcending space, eradicating national borders and geopolitics, data sovereignty regulations endow locality with renewed significance in the cloud era.
The survival of data at all costs
Towards the end of the corridor, Thomas opens a large red blast-proof door—beyond which is a smaller air-tight door. Thomas waves his card in front of an e-reader, initiating an unlocking process: we’re about to enter one of the server rooms.
“Get ready,” he says, smiling, “It’s going to be cold and loud!” The door opens, releasing a rush of cold air. The server room is configured and calibrated for the sole purpose of providing optimal conditions for data storage.
Like any computer, servers generate a huge amount of heat when they are running, and must be stored in constantly air-conditioned rooms to ensure they do not overheat. If, for any reason, a server should crash or fail, it can lead to the loss of a client’s valuable data. Data center technicians work in high-pressure conditions where any unexpected server downtime could mean the end of their job.
To try and make sure the servers run optimally, data centers rely on huge amounts of water and energy, which can significantly limit the availability of these resources for the people who live in the vicinity of the buildings.
An average data center consumes an estimated 200 terawatt hours of electricity each year. That’s around 1% of total global electricity demand, which is more than the national energy consumption of some countries. Many of these facilities are powered by non-renewable energy sources, and the data center industry is expected to emit 2.5 billion metric tons of carbon dioxide by 2030.

In addition, to meet expectations for “uninterruptible” service levels, data centers rely on an array of fossil fuel-based back-up infrastructure—primarily diesel generators. For this reason, the Green Web Foundation—a non-profit organization working to decarbonize the internet—has described the internet as the world’s largest coal-powered machine. Data centers are also noisy and have become sites of protest for local residents concerned about noise pollution.
Amid hype and speculation about the rise of AI, which is leading to a boom in the construction of energy-hungry data centers, the carbon footprint of the industry is under increasing scrutiny. Keen to highlight Cyberfort’s efforts to address these issues, Thomas informs me that “environmental impact is a key consideration for Cyberfort, and we take our commitment to these issues very seriously.”
As we walk down a cold aisle of whirring servers, he explains that Cyberfort actively sources electricity from renewable energy supply chains, and uses what he calls a “closed loop” cooling infrastructure which consumes minimal fresh water.
‘Like the pyramids’
After our walk through the server room, we begin to make our way out of the bunker, heading through another heavy-duty blast door. As we walk down the corridor, Thomas promotes the durability of bunkers as a further security selling point. Patting the cold concrete wall with the palm of his hand, he says, “Bunkers are built to last, like the pyramids.”
Bunker scholars have long noted that these buildings are as much about time as they are about space. Bunkers are designed to preserve and transport their contents through time, from an apocalyptic present into a safe future.
Writers such as Paul Virilio, W.G. Sebald and J.G. Ballard were drawn to the decaying bunkers of the Second World War and, like Thomas, compared them with enduring megastructures which have outlived the civilizations that built them. In his 1975 book Bunker Archaeology, Virilio famously compared the abandoned Nazi bunkers along the coast of France with “the Egyptian mastabas, the Etruscan tombs, the Aztec structures.”
The bunker’s durability invites us to take a long-term view of our own data storage needs, which will only increase over the course of our lives.
For technology behemoths like Apple and Google, cloud storage is a key strategic avenue for long-term revenue growth. While the phones, laptops and other digital devices they make have limited lifespans, their cloud services offer potentially lifelong data storage. Apple and Google encourage us to perpetually hoard our data rather than delete it, because this locks us into their cloud subscription services, which become increasingly expensive the more storage we need.
Apple’s marketing for its cloud storage service, iCloud, encourages users to “take all the photos you want without worrying about space on your devices.” Google has made “archive” rather than “delete” the default option on Gmail. While this reduces the likelihood of us accidentally deleting an email, it also means we are steadily consuming more of our Gmail capacity, leading some to purchase more Google Drive storage space.
Cloud hoarders
It is also increasingly difficult to operate off-cloud. Internal storage space on our digital devices is dwindling as the cloud becomes the default storage option on the majority of digital products being developed. Users must pay a premium if they want more than the basic local storage on their laptop or smartphone. Ports to enable expandable, local storage—such as CD drives or SD card slots—are also being removed by tech manufacturers.
As our personal digital archives expand, our cloud storage needs will continue to grow over our lifetimes, as will the payments for more and more cloud storage space. And while we often imagine we will one day take the time to prune our accumulations of digital photos, files, and emails, that task is often indefinitely postponed. In the meantime, it is quicker and easier to simply purchase more cloud storage.

Many consumers simply use whichever cloud storage service is already pre-installed on their devices—often these are neither the cheapest nor most secure option. But once we commit to one provider, it is very difficult to move our data to another if we want a cheaper monthly storage rate, or simply want to switch—this requires investing in enough hard drives on which to download the data from one cloud provider and upload it to another. Not everyone is tech-savvy enough to do that.
In 2013, bank reforms in the UK introduced a switching service which enabled consumers to easily move their money and payments to different banks, in order to access more favorable rates.
Cloud migration services are available for businesses, but until a cloud storage equivalent of the bank switching service is developed for the general public, many of us are essentially locked into whichever cloud provider we have been using. If our data really is the new gold, perhaps we should require cloud providers to offer incentives to deposit it with them.
Some providers now offer “lifetime” cloud packages with no monthly or yearly payments and no inactivity clause. However, the cloud market is volatile, defined by cycles of boom-and-bust, with providers and their data centers constantly rebranding, closing and relocating. In this landscape of mergers and acquisitions, there is no guarantee that lifetime cloud providers will be around long enough to honor these promises.
In addition, the majority of consumer cloud providers currently only offer a maximum of a few terabytes of storage. In the future, most of us will probably need a lot more than this, which could mean a lot more data centers (roughly 100 new data centers are set to be constructed in the UK alone within the next five years). We may also see more bunkers being repurposed as data centers—while some providers, such as Florida-based Data Shelter, are considering building entirely new bunker structures from scratch to house digital data.
Resurfacing
Thomas and I arrive at the steel staircase leading back up to the outside world. The guard buzzes us back through the turnstile, and Thomas unlocks and opens the door. The sunlight stings my eyes.
Back in the reception area, I thank Arnold and Thomas for my surreal trip into the depths of subterranean data storage. The Cyberfort data center is a site of extreme contrasts, where the ethereal promise of the cloud jars with the concrete reality of the bunker.
Sitting in my car, I add to my fieldnotes that the survival of data—whether entombed in bunkers or stored in “lifetime” cloud accounts—is bound to the churn of markets, and depends upon the durability of the infrastructure and organizations behind it.
Permanence, in the digital age, is always provisional. One can’t help but imagine future archaeologists discovering this bunker and rummaging through the unreadable remains of our lost digital civilization.
This article is republished from The Conversation under a Creative Commons license. Read the original article.![]()
Citation:
Underground data fortresses: The nuclear bunkers, mines and mountains being transformed to protect data from attack (2025, September 27)
retrieved 27 September 2025
from https://techxplore.com/news/2025-09-underground-fortresses-nuclear-bunkers-mountains.html
This document is subject to copyright. Apart from any fair dealing for the purpose of private study or research, no
part may be reproduced without the written permission. The content is provided for information purposes only.
Tech
Can OpenAI’s ‘Master of Disaster’ Fix AI’s Reputation Crisis?
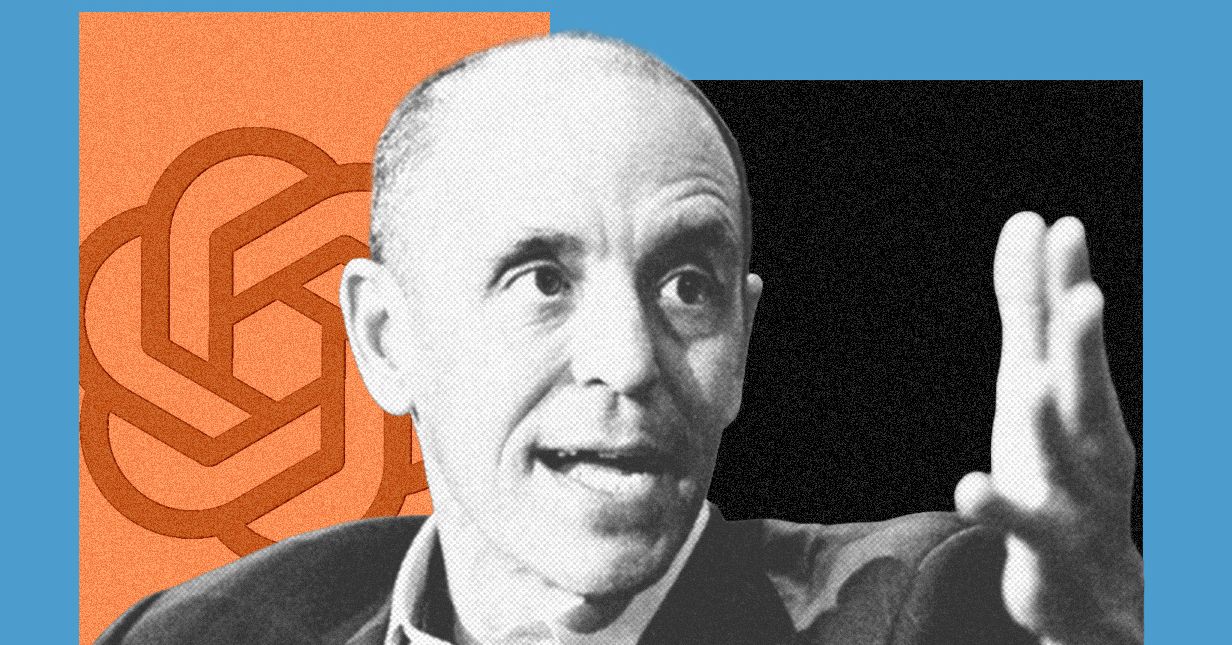
Three months ago, OpenAI cofounder Greg Brockman told me his concerns about a mounting public relations crisis facing artificial intelligence companies: Despite the popularity of tools like ChatGPT, an increasingly large share of the population said they viewed AI negatively. Since then, the backlash has only intensified.
College commencement speakers are now getting booed for talking about AI in optimistic terms. Last month, someone threw a Molotov cocktail at OpenAI CEO Sam Altman’s San Francisco home and wrote a manifesto advocating for crimes against AI executives. No one has more to lose from this reputation crisis than OpenAI.
The person tasked with trying to fix it is Chris Lehane, OpenAI’s chief of global affairs and a veteran political operative. I sat down with him this week to discuss what I’d argue are his two biggest challenges yet: convincing the world to embrace OpenAI’s technology, while at the same time persuading lawmakers to adopt regulations that won’t hamper the company’s growth. Lehane views these goals as one in the same.
“When I was in the White House, we always used to talk about how good policy equals good politics,” says Lehane. “You have to think about both of these things moving in concert.”
After working on crisis communications in Bill Clinton’s White House, Lehane gave himself the nickname “master of disaster.” He later helped Airbnb fend off regulators in cities that viewed short-term home rentals as existing in a legal gray area, or as he puts it, “ahead of the law.” Lehane also played an instrumental role in the formation of Fairshake, a powerful crypto industry super PAC that worked to legitimize digital currencies in Washington. Since joining OpenAI in 2024, he’s quickly become one of the company’s most influential executives and now oversees its communications and policy teams.
Lehane tells me public narratives about how AI will change society are often “artificially binary.” On one side is the “Bob Ross view of the world” that predicts a future where nobody has to work anymore and everyone lives in “beachside homes painting in watercolors all day.” On the other is a dystopian future in which AI has become so powerful that only a small group of elites have the ability to control it. Neither scenario, in Lehane’s opinion, is very realistic.
OpenAI is guilty of promoting this kind of polarizing speech in the past. CEO Sam Altman warned last year that “whole classes of jobs” will go away when the singularity arrives. More recently he has softened his tone, declaring that “jobs doomerism is likely long-term wrong.”
Lehane wants OpenAI to start conveying a more “calibrated” message about the promises of AI that avoids either of these extremes. He says the company needs to put forward real solutions to the problems people are worried about, such as potential widespread job loss and the negative impacts of chatbots on children. As an example of this work, Lehane pointed to a list of policy proposals that OpenAI recently published, which include creating a four-day work week, expanding access to health care, and passing a tax on AI-powered labor.
“If you’re going to go out and say that there are challenges here, you also then have an obligation—particularly if you’re building this stuff—to actually come up with the ideas to solve those things,” Lehane says.
Some former OpenAI employees, however, have accused the company of downplaying the potential downsides of AI adoption. WIRED previously reported that members of OpenAI’s economic research unit quit after they became concerned that it was morphing into an advocacy arm for the company. The former employees argued that their warnings about AI’s economic impacts may have been inconvenient for OpenAI, but they honestly reflected what the company’s research found.
Packing Punches
With public skepticism toward AI growing, politicians are under pressure to prove to voters they can rein in tech companies. To combat this, the AI industry has stood up a new group of super PACs that are boosting pro-AI political candidates and trying to influence public opinion about the technology. Critics say the move backfired, and some candidates have started campaigning on the fact that AI super PACS are opposing them.
Lehane helped set up one of the biggest pro-AI super PACs, Leading the Future, which launched last summer with more than $100 million in funding commitments from tech industry figures, including Brockman. The group has opposed Alex Bores, the author of New York’s strongest AI safety law who is running for Congress in the state’s 12th district.
Tech
Meta Is in Crisis, Google Search’s Makeover, and AI Gets Booed by Graduates

Leah Feiger: Let’s invest.
Zoë Schiffer: They have that going for a while.
Leah Feiger: It wasn’t full Google, but it—
Zoë Schiffer: Somewhat there.
Leah Feiger: —had that vibe. To me, someone so on the outside of this in every single way, I know about these layoffs because they’ve been, A) so chaotic, but B) in some ways, needlessly so. Not to say that other tech companies aren’t firing scores of workers all the time. That feels like something we discuss on this podcast frequently, but this is happening with such a large runway and in a way that’s making employees feel so terrible about themselves.
Brian Barrett: Well, because it’s not just the layoffs, right? It’s also, even if you stay there, if you’re not culled from the herd, you are going to have to deal with this world in which you’ve got spyware on your laptops training AI to probably take your job at some point, right?
Zoë Schiffer: Explain that a little bit.
Brian Barrett: Meta announced, and this was more public, that they were going to put software on employee laptops that would monitor their keystrokes and how they move their cursors and basically how they do their job as Meta engineers and use that as training data for their own internal models to try to make their AI models better because they’re running out of other sources.
Zoë Schiffer: And could you opt out of that, Brian?
Brian Barrett: That’s a great question. I’m so glad you asked. You could not opt out.
Zoë Schiffer: I felt you didn’t know the answer to that one.
Brian Barrett: In fact, when an employee asked in a very public forum within Meta, “Hey, could we not do this?” Zoë, the response was?
Zoë Schiffer: Oh, absolutely you’re going to do this and shame on you for asking. And some of the employees who are staying, actually thousands of the employees who are staying, are getting drafted into the AI ranks. We published a piece today that was kind of about the morale inside the company, but also how there’s been this mad dash to use up perks and stipends that employees have. But one of the things that’s said at the end was that remaining employees are being asked to join AI teams. So whatever your job was previously, they’re internally getting drafted. You’re getting drafted into the AI ranks, now your job is going to look quite different.
Brian Barrett: That’s like 7,000 people.
Zoë Schiffer: Yes.
Leah Feiger: I’ve actually heard people use the word raptured.
Zoë Schiffer: Oh, my gosh.
Leah Feiger: Isn’t that—
Zoë Schiffer: And I wish we had that in the story.
Leah Feiger: I’m so sorry, but raptured into other teams. All of a sudden one day they’ve just disappeared. After this layoff, has Zuckerberg and co proposed a sort of coherent leadership plan or proposal? What happens after this?
Tech
Why the 2026 Hurricane Season Might Not Be That Bad

Atlantic hurricane season is almost upon us, and the early signs indicate it might be less active than usual. But that’s no reason to delete your weather app and ignore the forecast.
The National Oceanic and Atmospheric Administration is predicting eight to 14 named tropical systems, of which three to six will become hurricanes and one to three will be Category 3 or higher.
“What’s driving this forecast is largely an El Niño event,” said NOAA administrator Neil Jacobs.
Characterized by a tongue of hot water stretching across the Pacific, El Niño is likely to emerge this summer. That stretch of warm ocean rearranges weather patterns around the world. In the case of the tropical Atlantic, El Niño stirs up winds that make it hard for hurricanes to spin up. Those that do can sometimes be torn apart by what’s going on in the upper atmosphere. (The opposite is true in the Pacific, and NOAA is predicting a very active season in that ocean basin.)
During the three past super El Niños, accumulated cyclone energy—a metric that factors in storms’ strength and longevity—was well below normal.
That said, El Niño, even an extremely strong one, is only one of many factors that impact hurricane season. Hot local ocean temperatures can help storms form and gain strength, and the Atlantic is currently warmer than normal.
At the same time, Sahara dust can gum up the atmosphere and inhibit storms from forming. It’s also notoriously hard to predict when plumes of it will kick up. That’s what happened last year, when a below-average number of named storms formed despite an active forecast. Despite the lower-than-expected activity, last year still spawned Hurricane Melissa, one of the strongest storms to ever make landfall in the Atlantic basin.
All of which is to say that the seasonal forecast is a handy guide for what to expect, and it’s great for federal and state agencies to preposition supplies and resources. But it’s what happens with individual storms that ultimately matters.
“Even though we’re expecting a below average season in the Atlantic, it’s important to understand it only takes one,” Jacobs said, noting that even in quiet years, Category 5 storms have still made landfall.
The Trump administration has slashed staffing at NOAA and reduced the collection of some data, such as weather balloons, that can impact forecasts. Jacobs touted the value of new observations, including aerial drones that will be deployed operationally for the first time.
NOAA has also ramped up the use of artificial intelligence weather models trained on historical data. During the 2025 hurricane season, the agency tested an experimental hurricane model developed with Google DeepMind. Late last year, it also rolled out a suite of AI weather models to use in operational forecasting, in addition to traditional weather models that use equations to forecast the weather.
The agency says that the AI version of its flagship model provides better prediction of the tracks of tropical cyclones—the generic name for hurricanes—though it lags traditional weather models in predicting their intensity.
-

 Fashion1 week ago
Fashion1 week agoItaly’s Zegna Group’s Q1 growth boosted by strong organic performance
-

 Entertainment6 days ago
Entertainment6 days agoWhere Pete Davidson, Elsie Hewitt stand after breakup: Details revealed
-

 Business1 week ago
Business1 week agoTui issues update on summer jet fuel shortage fears
-

 Business1 week ago
Business1 week agoJersey Election 2026: Cost of living concern in St Helier Central
-

 Entertainment1 week ago
Entertainment1 week agoEmilia Clarke recalls near-death incident while filming ‘Game of Thrones’
-

 Fashion1 week ago
Fashion1 week agoGlobal cotton production, stocks to fall; consumption to rise: WASDE
-

 Politics6 days ago
Politics6 days agoRising diesel costs from Iran war strain US school budgets
-

 Fashion1 week ago
Fashion1 week agoUS’ Kontoor Brands’ posts strong Q1, plans Lee divestiture